Team Services October Extensions Roundup – Rugged DevOps
This month the focus is on making your DevOps environment rugged. According to Puppet, teams leveraging DevOps are deploying 200x more frequently and leveraging 90% more OSS components. Many of these teams, however, have not integrated security into their processes. The teams who have, spend 50% less time fixing security issues later. With this roundup we’ll look at three extensions that add support for OSS security and license validation, as well as code scanning, to ‘shift left’ your security and assist you in spending less time to build more secure software.
WhiteSource
See it in the Marketplace: https://marketplace.visualstudio.com/items?itemName=whitesource.whitesource
If your project leverages OSS, then you need to consider using WhiteSource. This extension adds a build task that enables critical OSS management scenarios once connected with your WhiteSource account.
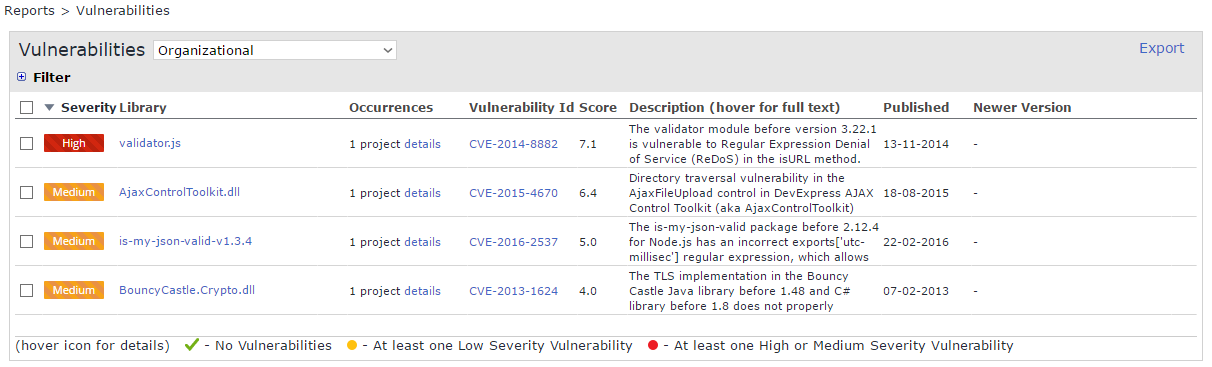
- Secure Your Open Source Usage – automatically detect OSS components and dependencies being used in your project without the need to scan your code using the WhiteSource build task and your repositories
- Get Real-Time Alerts on Security Vulnerabilities – get alerted whenever a component with a known security vulnerability is added to your project, or when new vulnerabilities are found in components you’re already using. You can also set up alerts for component licenses based on your pre-defined policies, security fixes, and component versioning
- Automat Your Open Source Approval Process – Using pre-defined policies with your WhiteSource account, you can automate the approval or rejection of newly added OSS components based on licenses, vulnerabilities, severe software bugs, quantity of newer versions and more
HPE Security Fortify VSTS extension
See it in the Marketplace: https://marketplace.visualstudio.com/items?itemName=fortifyvsts.hpe-security-fortify-vsts
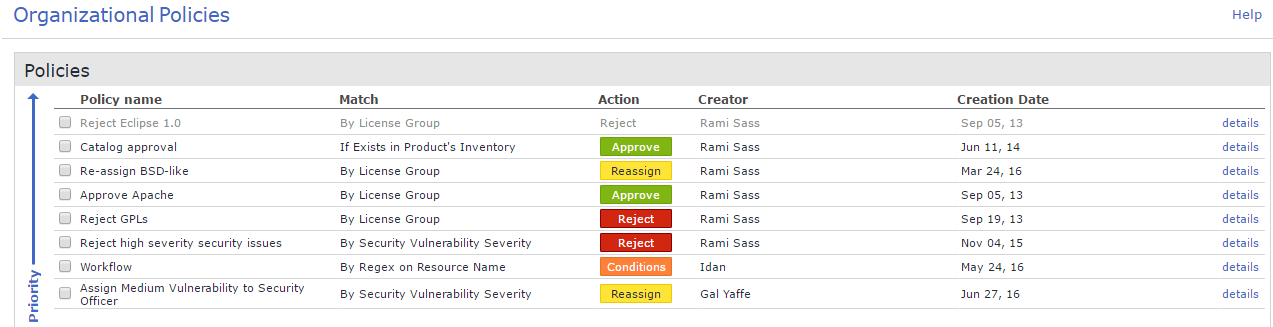
This extension adds 4 build tasks and enables you to leverage HPE Fortify for their two major offerings: Fortify SCA and Fortify on Demand.
HPE Fortify’s SCA provides a security source code analysis using a multitude of security coding rules and guidelines for a broad set of programming languages. There are two build tasks added by this extension that enable Fortify SCA
- Fortify Static Code Analyzer Installation – You’ll run this task to automatically install the Fortify SCA software to your build agent. You just provide the Fortify license file and this will install unless SCA is already present. It will also configure it with the Fortify rule packs the license entitles you to.
- Fortify Static Code Analyzer Assessment – This task actually runs the SCA as a build step, leverages all the proper parameters, and can output the results of your scan as build artifacts.
Fortify on Demand delivers security as a service and consists of a static scan that is audited by their team of experts, or a dynamic scan that mimics real-world hacking techniques and attacks using both automated and manual techniques to provide comprehensive analysis of complex Web applications and services. Two build tasks are included in this extension
- Fortify on Demand Static Assessment – this requests a static assessment as a build step and performs the necessary upload to the Fortify on Demand service. You can be notified based on your own preferences and your results will be in your Fortify Portal
- Fortify on Demand Dynamic Assessment – this requests a dynamic scan as a build step. Before using this task you’ll need to configure your dynamic scan settings in your Fortify on Demand portal. At the portal, you’ll configure the URL where your application is being deployed and hosted.
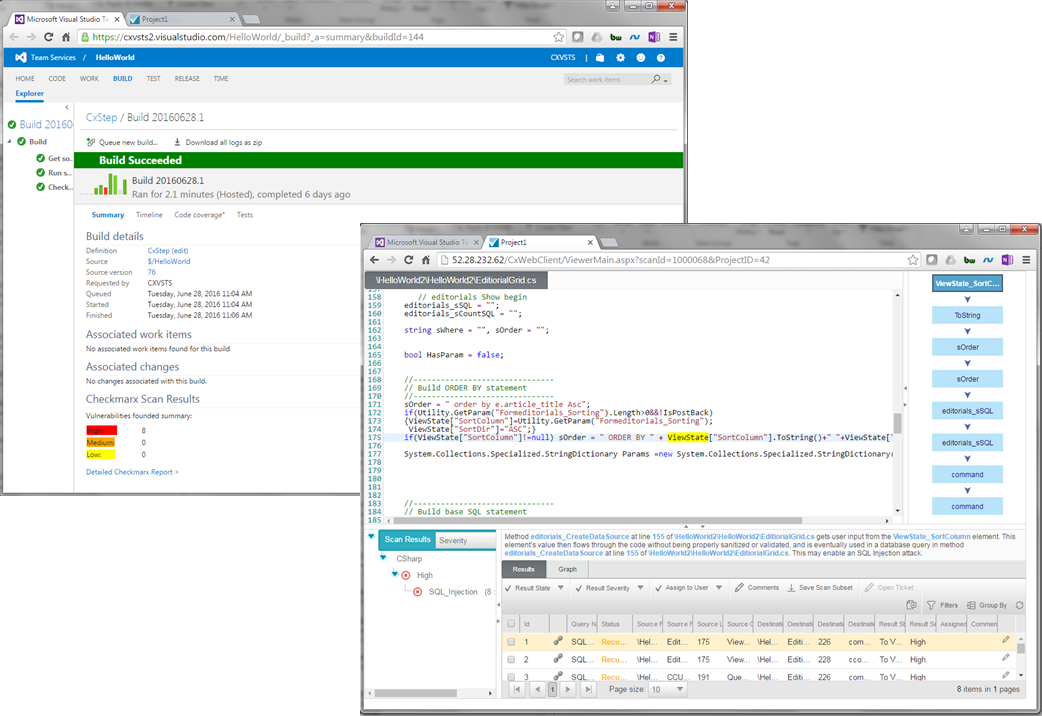
Checkmarx
See it in the Marketplace: https://marketplace.visualstudio.com/items?itemName=checkmarx.cxsast
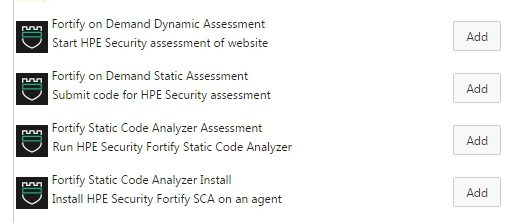
If security at speed is what you’re looking for, give Checkmarx a look. This extension offers Static Source Code Analysis and what separates them from the competition are their features like incremental scanning and best fix location. The ability to only scan new or modified code keeps your build process fast, but still gives peace of mind that you will find your specific security flaws before they become problems. Best fix location even goes as far to highlight where you should fix your code.
To use the build task, you’ll just need to configure a service endpoint with your Checkmarx account to use with the build task.
Are you using an extension you think should be featured here?
I’ll be on the lookout for extensions to feature in the future, so if you’d like to see yours (or someone else’s) here, then let me know on Twitter!


 Light
Light Dark
Dark
0 comments