Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
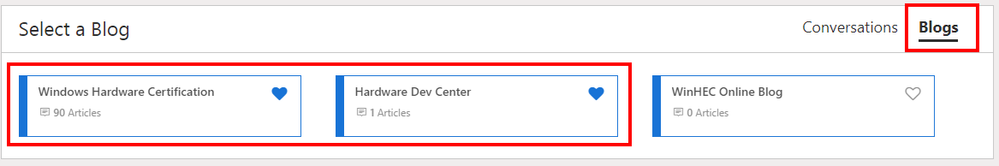
Windows Hardware Certification
URL
Copy
Options
Author
invalid author
Searching
# of articles
Labels
Clear
Clear selected
1607
audio certification
audio certification requirement update
audio device certification
bde wlk test
bitlocker tpm and recovery password tests
certification fees
certifying devices for windows 8 1
certifying windows 8 devices
changes to uefi signing policy
Dashboard
dashboard updates
device audio hardware architecture
download mutt software
Drivers
driver signing
driver signing changes
errata expiration guidelines
fast track windows 8 1 certification
fast track windows 8 1 certification certifying windows 8 devices certifying devices for windows 8 1
february 2014 qfe
hardware certification
hardware certification billing
hardware certification billing alias
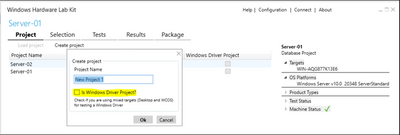
hardware certification kit
hardware certification submission fees update
hck
hck errata
hck filter publication
hck filter publication schedule
hck filters
hck qfe 05 hck hardware certification kit whck windows hardware certification kit hck update
hck qfe 06
hck qfe 07
hck qfe 08
hck qfe 08 bug
hck qfe 08 fix
hck qfe 09
hck qfe 10
hck qfe 11
hck qfe 12
hck qfe 8 removal
hck requirements changes
hck update
logo license agreement for hardware version 2014
mutt
mutt software package update available
Network Additional Qualifications
precision touchpad certification
precision touchpad certification faq
pre submission testing for uefi submissions
ptp certification
ptp certification faq
qfe 006
self test submission
self test submission for touch device and precision touchpad certification
service pack testing policy
sign a uefi app
sign a uefi driver
storage performance cs
supermutt
system sleep and pnp disable and enable with io before and after certification test
tablet products
test sign uefi modules
touch device certification
uefi signing policy
uefi signing submissions
uefi submissions
use of the windows symbol on devices
verify uefi submissions
waiver to the windows logo license agreement
whck
windows 1607
windows 8 1 update testing policy
windows 8 1 update testing requirements
windows certification
windows dev center hardware dashboard
windows dev center hardware dashboard updates
windows hardware certification
windows hardware certification blog
windows hardware certification kit
windows hardware certification kit hck
windows hardware certification requirement changes certification requirement changes certification requirement changes for january 2014
windows logo
windows logo license agreement
Windows Server 2022
windows server catalog
windows service pack or update release testing policy
windows symbol
windows update testing policy
- Home
- WinHEC Online
- Windows Hardware Certification
Options
- Mark all as New
- Mark all as Read
- Pin this item to the top
- Subscribe
- Bookmark
- Subscribe to RSS Feed





Latest Comments