Secure Web Services on Windows Azure Web Sites for Windows Store Applications
This blog post discusses how to secure web services on Windows Azure Web Sites for Windows Store applications.
Introduction to Windows Azure Web Sites
Windows Azure Web Sites is a highly scalable web application hosting service on Windows Azure. From the Windows Azure management portal, customers can quickly create a blank website, a website with a SQL database, or a website based on a template in the open source gallery such as blogs, CMS, eCommerce, forums, galleries and Wikis.
There are three hosting modes for Windows Azure Web Sites: Free, Shared and Reserved.
· Free - Out of the box, Windows Azure allows you to create and host up to 10 web-sites in a free, shared, multi-tenant hosting environment. This free shared option limits 165MB/day of content or 5GB/month, and therefore is suitable for Web Sites to be used for demo, development or testing.
· Shared - The shared mode doesn’t have the limits of the free mode. The first 5 GB/month of bandwidth you serve with a shared web-site is free, and then you pay the standard “pay as you go” Windows Azure outbound bandwidth rate for outbound bandwidth above 5 GB. A web-site running in shared mode provides the ability to map multiple custom DNS domain names to a site.
· Reserved – The reserved mode allows you to choose from Small, Medium or Large VM instances and run your sites in isolated environment. Unlike shared mode, there is no per-site cost when running in reserved mode. Instead you pay only for the reserved instance VMs you use – and you can run any number of web-sites you no extra cost.
With each hosting mode you can scale out resources for your Web Sites by increasing or decreasing instances from 1 to 3 or from 3 to 1 (in Preview). You can deploy a site using the shared mode option to begin with, and then dynamically scale up to the reserved mode if needed.
Windows Azure Web Sites is ideal for hosting modern web applications and services. To find out how Windows Azure Web Sites differ from other hosting services such as Windows Azure web roles and Virtual Machines, read Brian Swan’s blog post, “Windows Azure Web Sites, Web Roles, and VMs: When to use which?” or at https://blogs.msdn.com/b/silverlining/archive/2012/06/27/windows-azure-Web Sites-web-roles-and-vms-when-to-use-which.aspx
For more information on pricing details of Windows Azure Web Sites, visit https://www.windowsazure.com/en-us/pricing/details/#web-sites
Secure Web Services on Windows Azure Web Sites
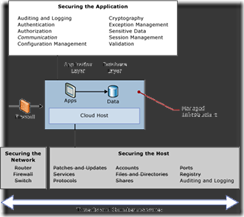
You can find information from the web about common threats to web applications and best practices for securing applications running on the Microsoft platform. Below is a high-level diagram from the “Windows Azure Security Guidance” white paper that outlines common threats and countermeasures related to the application infrastructure and securities for applications -- authentication, authorization, auditing and logging, etc.
Most if not all best practices for securing web applications are applicable to applications and services running in Windows Azure. However, securing services in Windows Azure depends on services and capabilities that are unique to the cloud computing platform and therefore it is worth discussion of some of the security measures in the article.
WCF Services on Windows Azure Web Sites
WCF services can be implemented in one of the two types: WCF SOAP Service and WCF REST service. For information on when to use WCF SOAP Service vs. WCF REST service, read MSDN articles below:
· “SOAP, REST, and More”, Jon Flanders, https://msdn.microsoft.com/en-us/magazine/dd942839.aspx
· “Operation-based SOAP vs. Resource-based REST”, Robert Dizon, https://msdn.microsoft.com/en-us/library/vstudio/hh323724(v=vs.100).aspx
Both of these services can be hosted on Windows Azure Web Sites. When Windows Azure Active Directory is used to authenticate users, security practices are be implemented similarly for these services. When user authentication is done through identity service providers such as Microsoft accounts, Google, Facebook and Yahoo, security practices are be implemented similarly for these services.
In the “Windows Azure Security Guidance” white paper, four security architectural options for WCF services have been identified and addressed. In each option there is Windows Azure Active Directory (AD). Windows Azure Active Directory (Windows Azure AD) is a modern, REST-based service that provides identity management and access control capabilities for your cloud applications. Find more info on Windows Azure AD at https://www.windowsazure.com/en-us/home/features/identity/
Option 1: WCF (SOAP) Service with Service Identity
In this scenario, Windows Azure AD Access Control is used to issue SAML tokens that will be handled by WIF at the WCF (SOAP) service. See diagram below.
Option 2: WCF (SOAP) Service With Federated Authentication, Identities In Active Directory
In this scenario, Windows Server ADFS is deployed and issues tokens to the agent that needs to access the WCF (SOAP) service. The agent then uses the token to submit request to the WCF (SOAP) service.
Option 3: WCF (REST) Service With Service Identities
In this scenario, Windows Azure AD Access Control is used to issue Simple Web Token (SWT) tokens. The application parses the SWT token on the REST service side manually or with a custom handler that is plugged into a WIF pipeline.
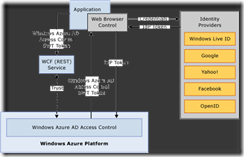
Option 4: WCF (REST) Service with Live ID / Microsoft Account, Facebook, Google, Yahoo!, Open ID
In this scenario, a public Internet identity such as Microsoft Live ID or Facebook is used to authenticate users and Windows Azure AD Access Control to issue SWT tokens. The application parses the SWT token on the REST service side manually or with a custom handler that is plugged into a WIF pipeline. Note that web browser control is used for client applications such as Windows Phone 8 to collect end user credentials because Internet identities mainly support passive profile scenarios (web apps) that rely on browser redirects, which is unavailable in client applications.
ASP.NET WebAPI Services
Introduced first with the release of ASP.NET 4 Beta, ASP.NET Web API is a new framework for creating HTTP services that can reach a broad range of clients including browsers and mobile devices. ASP.NET Web API is also an ideal platform for building RESTful services.
ASP.NET WebAPI services can be deployed and hosted on Windows Azure Web Sites. You can find a tutorial on how to build “Mobile-friendly REST service using ASP.NET Web API and SQL Database” by using the Publish Web wizard in Visual Studio 2012 at https://www.windowsazure.com/en-us/develop/net/tutorials/rest-service-using-web-api
ASP.NET API Quick Reference is available at https://www.asp.net/web-pages/overview/more-resources/asp-net-web-pages-api-reference, and examples from “List of ASP.NET Web API and HttpClient Samples” at https://blogs.msdn.com/b/webdev/archive/2012/08/26/asp-net-web-api-and-httpclient-samples.aspx
Security for ASP.NET WebAPI services hosted on Windows Azure Web Sites works similarly to that for WCF REST services. Windows Azure AD Access Control is used to issue Simple Web Token (SWT) tokens. The application parses the SWT token on the REST service side manually or with a custom handler that is plugged into a WIF pipeline.
An example of “Claim-based-security for ASP.NET Web APIs using DotNetOpenAuth” is available from a Microsoft application development manager Zulfiqar Ahmed at https://zamd.net/2012/05/04/claim-based-security-for-asp-net-web-apis-using-dotnetopenauth/
Conclusion
Windows Azure Web Sites provides great support for hosting web services such as WCF SOAP service, WCF REST service and the newly released ASP.NET WebAPI service. Securing web services in the public cloud computing environment is imperatively important. Windows Azure AD becomes the center piece for managing security for web services in Windows Azure. Applications can rely on not only security services available on Windows Azure and Windows Server such as Windows Identity Foundation, AD Federation Service, and Windows Azure AD Access Control, but also Internet Identity services such as Live ID /Microsoft Account, Facebook, Google, Yahoo, etc. These secured services on Windows Azure Web Sites are accessible securely to web apps, rich client apps, mobile apps and other services.
![clip_image005[1] clip_image005[1]](https://msdntnarchive.blob.core.windows.net/media/MSDNBlogsFS/prod.evol.blogs.msdn.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/43/49/metablogapi/8284.clip_image005%5B1%5D_thumb.gif)