Uninstall Windows XP Mode and Delete VHD Files
I have blogged about Windows XP Mode and application compatibility in a previous post and a recent post that referenced an article “Windows 7's XP Mode: what it is, how it works, who it's for” by Peter Bright. In this post I will discuss how to uninstall Windows XP Mode and how to remove a VHD file using a custom tool when necessary.
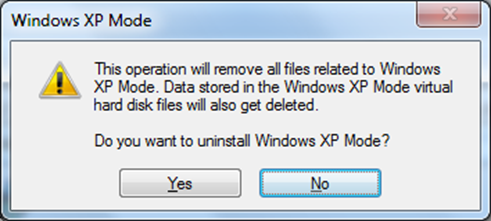
If for any reason you want to remove XP Mode from your Windows 7 computer, it is very straightforward to do so: go to the Control panel, select Windows XP Mode and uninstall it.
This action will remove two VHD files that have been installed at two default locations on your computer. Note that your Virtual PC is still enabled, which means you can still create and run Virtual PC images.
- C:\Users\<username>\AppData\Local\Microsoft\Windows Virtual PC\Virtual Machines\Windows XP Mode.vhd (the file size is about 428MB)
- C:\Program Files\Windows XP Mode\Windows XP Mode base.vhd (about 1.12GB)
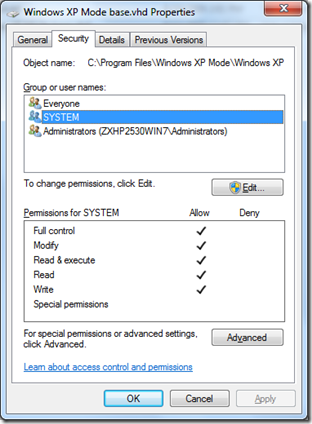
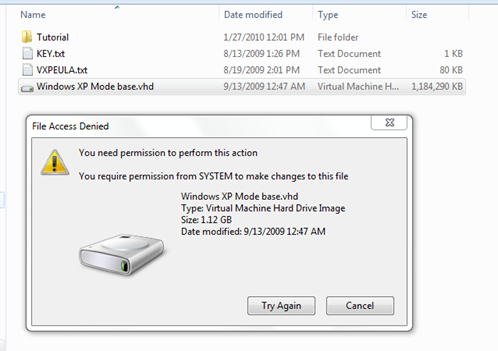
However, you may have to remove the “Windows XP Mode base.vhd” file manually if you ever left a copy of the file on the same computer, which was my case. The problem is that you cannot remove the VHD file because it is system protected and only the System account has Full Control rights on it as shown below.
In other words, even if you logged on with an administrator privileged account, you wouldn’t have much luck: the System account permission was required and you as a local administrator didn’t have the required permission. So the question is, how you could delete the file?
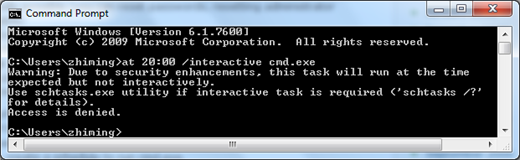
Thanks to Microsoft’s new search engine, Bing, I got several clues on how to run an interactive command line session (cmd.exe) under the System account. One clue as described in this post was to use the AT scheduler to launch a session under the System account, but this approach worked for XP only. If you try to run the following command line on Windows 7, you receive an “Access is denied” error.
at 20:00 /interactive cmd.exe
As suggested in the error message above, I tried the schtask utility. However the interactive session is only enabled if the /RU user is currently logged on at the time the job runs and the task runs only if the user is logged in.
schtasks /Create /SC ONCE /ST 20:00 /RU "NT AUTHORITY\SYSTEM" /RP /TN DeleteVHD /TR "cmd.exe"
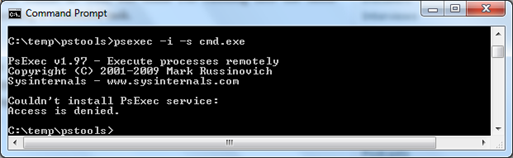
Another clue as outlined in this post was to use the psexec tool. If you try to run the following command line on Windows 7 (you have to download and install the pstools first), you receive an “Access is denied” error. As you can see, Windows 7 has tightened security in a big way.
psexec -i -s cmd.exe
At this point I felt I was pretty much out of the option, but I didn’t want to reformat my computer in order to get rid of the stubborn VHD file. As I continued to search for a possible solution, I realized that if I could set NTFS permissions on a file programmatically I might be able to grant Full Control permissions to a local administrator account and the problem would be solved. So I decided to proceed with this approach.
Those of us who have done programming work with XP or earlier versions of OS probably remember how this could be done with the Active Directory Service Interface (ADSI) APIs, as documented in this Microsoft Support article. But on Windows 7, you can use the managed code for folder and file related operations. There is a great example in an MSDN File Security Class article. I downloaded the sample code, created a VS2010 console app and made some minor changes. As shown in the code below, all I had to do was to grant FullControl permissions to a local administrator account which I specified.
//replace file name and account name
string fileName = "c:\\temp\\Windows XP Mode base.vhd";
string accountName =@"domainorcomputername\username";// Add the access control entry to the file.
AddFileSecurity(fileName, accountName, FileSystemRights.FullControl, AccessControlType.Allow);// Remove the file
File.Delete(fileName);
Once the console application was compiled, I copied it to the folder where the VHD file was located and scheduled the following task.
schtasks /Create /SC ONCE /ST 20:00 /RU "NT AUTHORITY\SYSTEM" /RP /TN GrantFileFullControl /TR "c:\temp\GrantFilePermission.exe"
I then issued a command to run the scheduled task immediately.
schtasks /run /TN GrantFileFullControl
The custom tool successfully added FullControl permissions to the file for the specified administrator account, but didn’t actually delete the file. I was puzzled for a moment. Fortunately, when I hit the DEL button manually, the file was gone! I almost couldn’t believe that it actually worked.
You can download the VS2010 tool here (C#).