Use Fiddler to capture websocket packet within non-browser runtime (like Node.js)
If you would like to skip the zig-zag and find the answer quickly, click me
Recently I'm involved in a project which needs to analyze packet of high-level protocol( MQTT , AMQP ) over Websocket. It is quite easy to capture Websocket packet from browser.
Chrome has some support for WS packet capture.
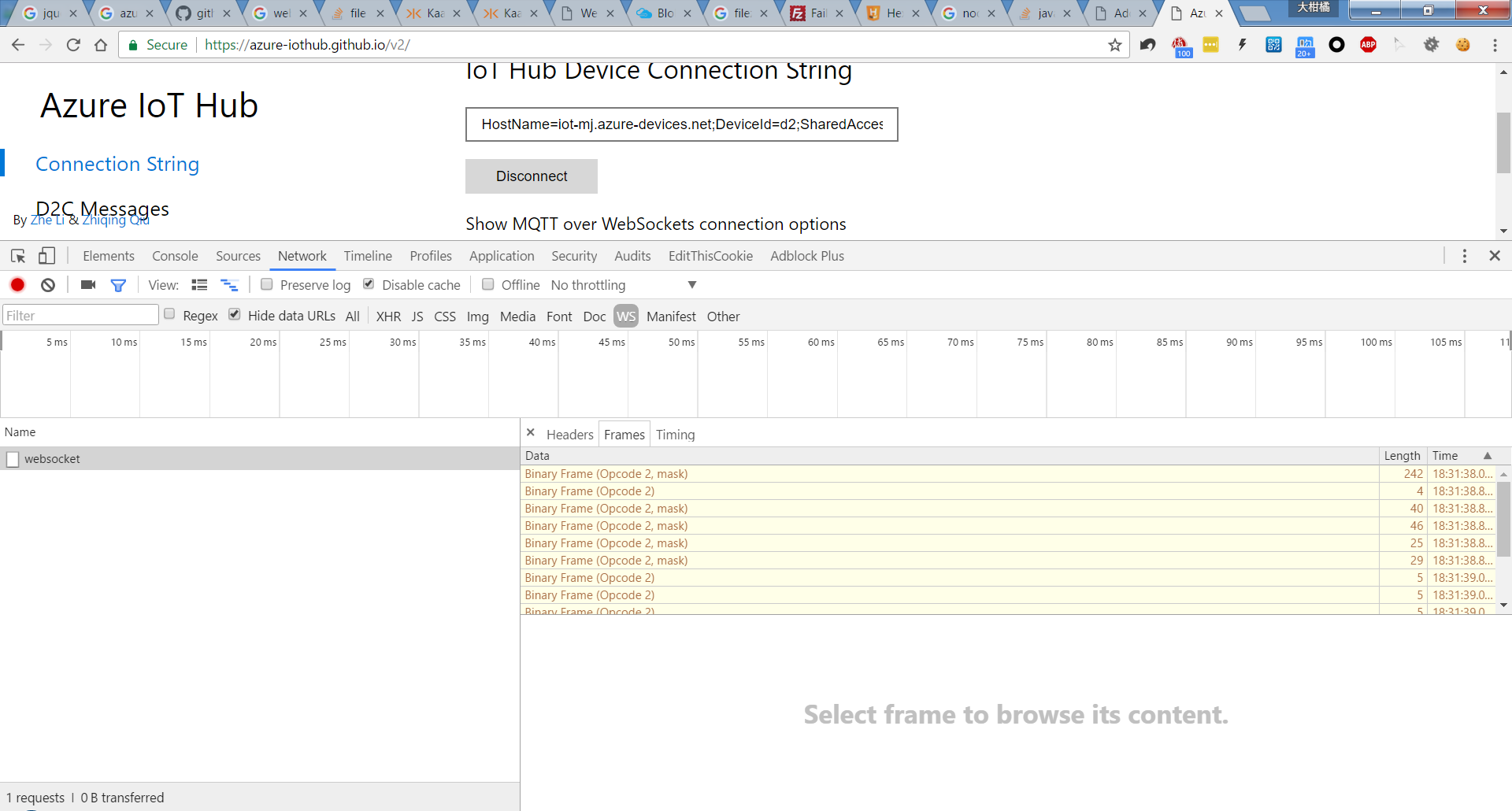
However, high-level protocol send Binary data frame, and we can't easily see the binary content.
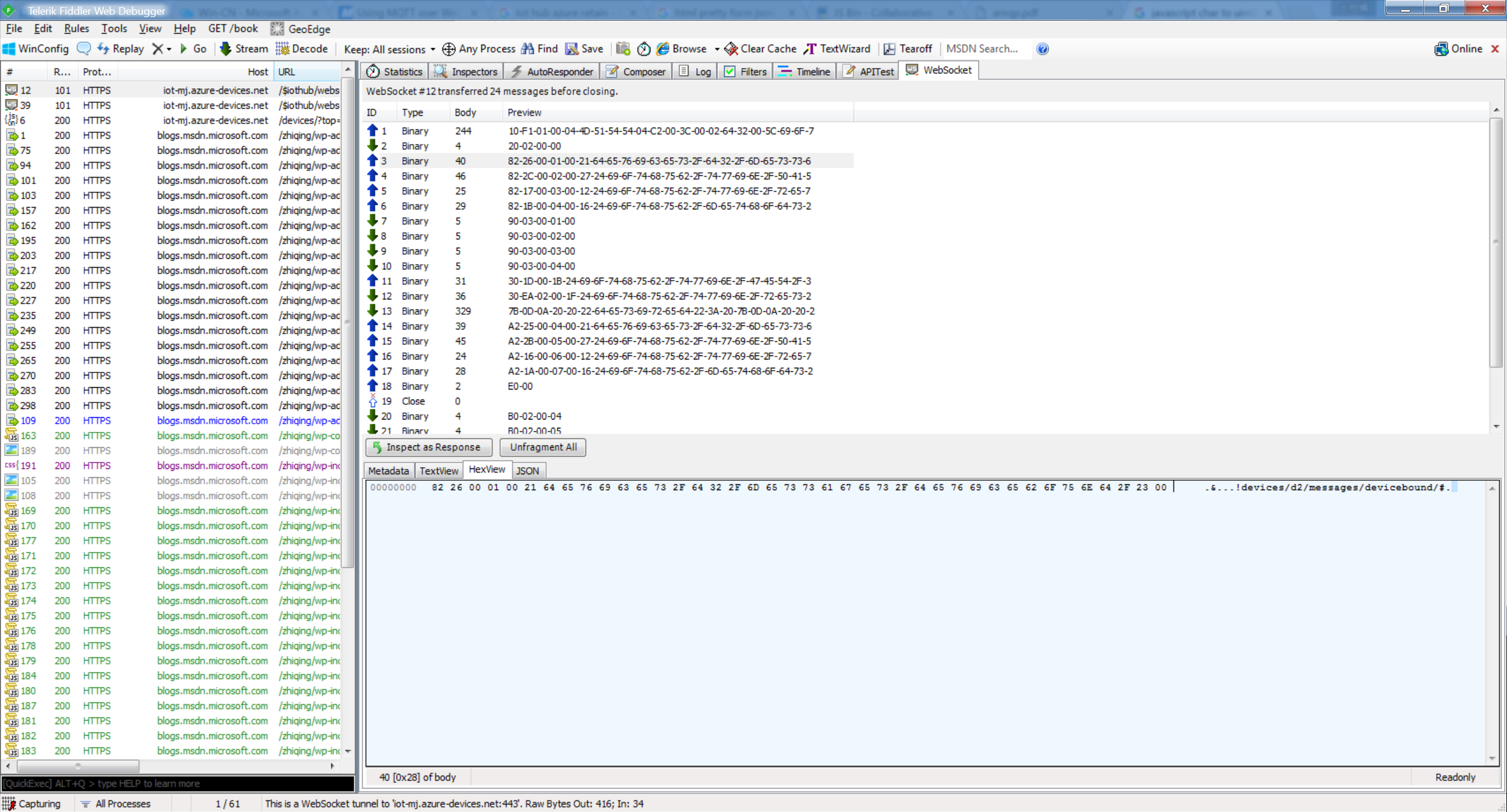
Fortunately, Fiddler can help us! Fiddler will show a tab "WebSocket" and we can easily see the full content of packets in Websocket like this:
But how to capture packet which doesn't come from browser, but from other runtime (for example Node.js)?
I tried npm config first,
npm config set proxy https://127.0.0.1:8888 npm config set https-proxy https://127.0.0.1:8888
It seems that this proxy setting only works for requests between client and npm server.
And also tried ways in this answer on SO, but also no luck.
Finally I found this fantastic tool,Proxifier. According to its description, it allows network applications that do not support working through proxy servers to operate through a SOCKS or HTTPS proxy and chains.
Here's the detailed steps:
1.Configure two settings in Proxifier
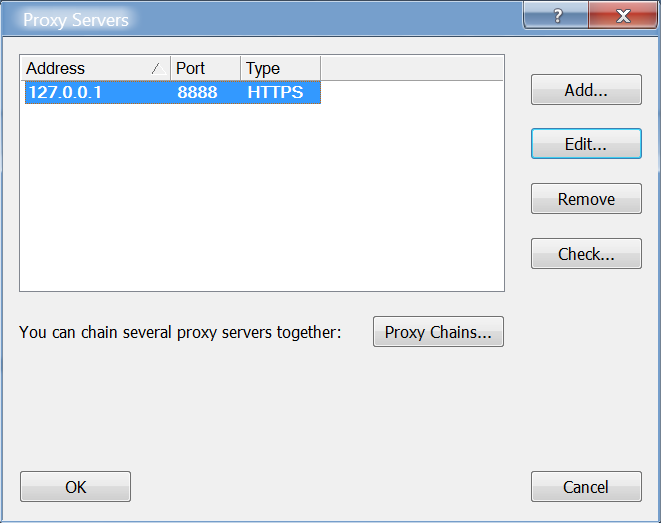
a.Proxy server setting:
Profile->Proxy server , set Fiddler proxy server here.
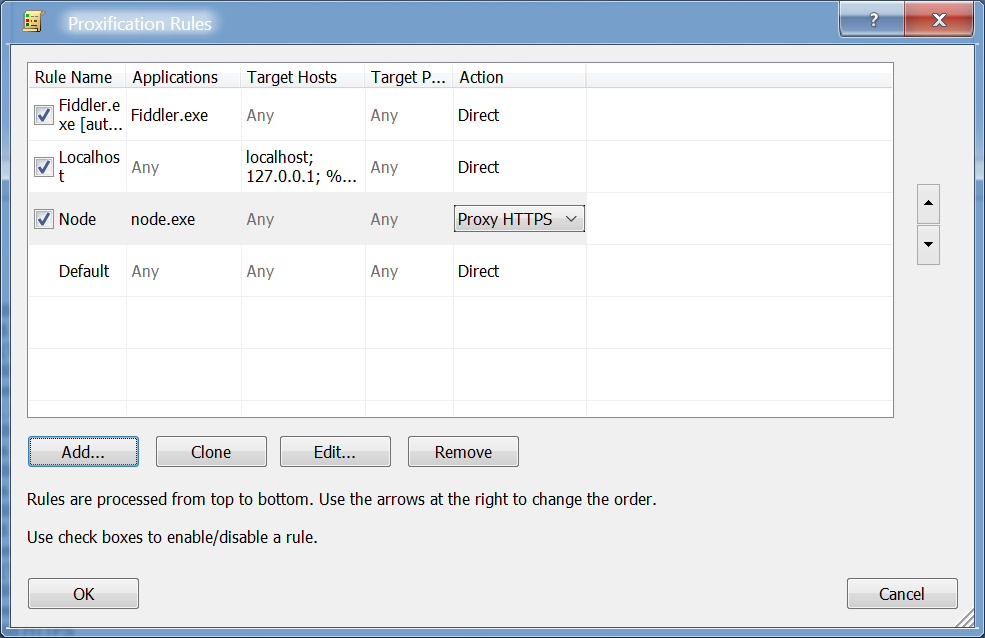
b.Rule setting:
We have to configure a few rules:
- set Fiddler.exe traffic not go through proxy, or the will be infinite loop
- set your taget application go through proxy
2. If your application use websocket over TLS/SSL, the self-signed certificate provided by Fiddler will be rejected. Trust Fiddler root certificate in system CA list doesn't work.(It seems that Node maintains its own trusted list) So we can configure an environment variable to solve this.
For Windows CMD:
[bash]
set NODE_TLS_REJECT_UNAUTHORIZED=0
[/bash]
For Windows Powershell:
[powershell]
$env:NODE_TLS_REJECT_UNAUTHORIZED = 0
[/powershell]
For unix:
[bash]
export NODE_TLS_REJECT_UNAUTHORIZED=0
[/bash]
Run your application and enjoy!