All About "Application Locked"
I have been working on this post slowly for several days, but Reed and Steve are seriously kicking my butt on posting solid developer-focused technical security content. Read their blog - they covered a lot of this material sooner and better than I did.
Some non-touchscreen Windows Mobile devices ship with a set of security policies that prevents developers from adding their own codesigning certificates. I don't know of any touchscreen devices that ship like that - it's possible to configure those devices to be locked down but none ship like that by default as far as I know. For some of these devices, it's possible to tweak the security policies via supported methods so you can install development certs,debug, and develop privileged applications. Internally we call this "the user is manager" meaning that the user has the ability to freely modify any software setting on the phone. In this post I'll describe how to figure out the security policies on your device and how to figure out if you are "application locked" or not.
For this post I'll assume that the end goal is to get the SDK certificates (sdkcerts.cab) installed on the phone. Once you've done that, you can run the remote registry editor from the SDK, develop and sign your own programs and do whatever you want.
Try This First
Let me get to the point first - I'd recommend two things, in order of likelihood of success
- Use the Device Security Manager. It has a great facility for inspecting the security policies and cert stores of a connected device, and even has a menu option to install the SDK certs for you.
- Try installing the unsigned sdkcerts.cab on the device. There are a few cases where the Security Manager tool errs on the side of caution and tells you that you can't install the certs, but they will really work via unsigned cab. I'll describe this case below.
If either of those work, the SDK certs are installed and you can now develop, change security policies, do whatever you want.
Local security policies
There are several security policies that come into play here. To install the SDK certs you need the highest level of trust on the device. (manager)
Unsigned CAB policy: If policy is set to 0, then unsigned CABs won't install. The typical role is User Auth which means the CABs will install but they have a similar set of privileges as code running at the Normal level. If this policy is set to Manager, then the unsigned CABs have all privileges, and you can use the unsigned cab technique to change any setting.
Two-tier security policy: If this is set to "One-tier" then CAB files and programs have the ability to change any setting on the device. Some smartphone devices ship in one-tier mode. Those phones are definitely not application locked - you can use the unsigned cab technique to apply any setting.
Grant Manager policy: This policy contains a list of roles that are elevated to manager. If this role contains "User Auth" then every action taken by the user has full administative access. Installing the setup XML from a cab file counts as one of those actions, so if grant manager contains User Auth, you can again use the unsigned cab technique to change any setting.
RAPI security policy: I think it's pretty uncommon for this policy to be open when the previous policies are be locked down, but if this policy is set to Open (2) then all of the API calls over Activesync are processed as trusted/manager, so you'll be able to change any setting or security policy using RAPI.
Inspecting security policies with the Device Security Manager
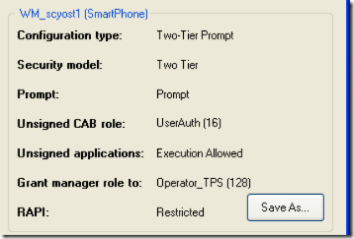
Here's the default configuration for a Windows Mobile "Standard" non-touch-screen device. All of the security policies mentioned above are in their restricted state. You won't be able to install the SDK certs onto a phone like this. It is possible to run unsigned untrusted code, so you can write some classes of apps, but the development and debugging experience is not great. The Device Security Manager will tell you that it can't install the SDK certs on a device like this. This is typically what most people mean when they say "Application Locked".
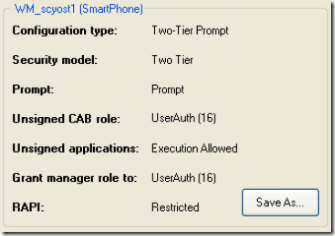
Here's another possible configuration. On this phone, the Grant Manager policy is set to "User Auth". This means that an unsigned cab will install with full privilege, after the prompt. The Device Security Manager still thinks this phone is locked down, so you'll need to install the unsigned cab by hand.
For a default Windows Mobile 6 SDK install, the SDKCerts cab is located at "C:\Program Files\Windows Mobile 6 SDK\Tools\Security\SDK Development Certificates\Certs.cab". Copy this CAB to a device configured like the above, and it will successfully install. Once the SDK certs are installed, you can write your own programs and use all the development tools that ship with the SDK.