Taking the next step with Windows Vista SP1
Back in December, I mentioned some changes were coming with WGA in Windows Vista. I want to say first that I'm excited about the step forward we're taking with SP1 and proud of the work that has gone into it. I'm excited both about the changes we've made to the user experience that we talked about and also about what we've done in Windows Vista SP1 to combat two of the most common methods we've seen for trying to hack product activation in Windows Vista.
First let me recap the changes to the customer experience that are included in SP1. "Reduced Functionality Mode" (RFM) has been removed from the product and replaced with a notifications-based experience. The purpose of the notifications-based experience is to differentiate between a genuine and activated copy of Windows Vista and one that is not, and do so in a way that maintains system functionality such as logon, access to the familiar desktop etc. This new experience means that systems that are not activated during their grace periods (initial activations as well as those due to hardware changes) or that fail our validation may have this experience.
The experience coming in SP1 is common across the activation and validation scenarios and here's what it's going to look like.
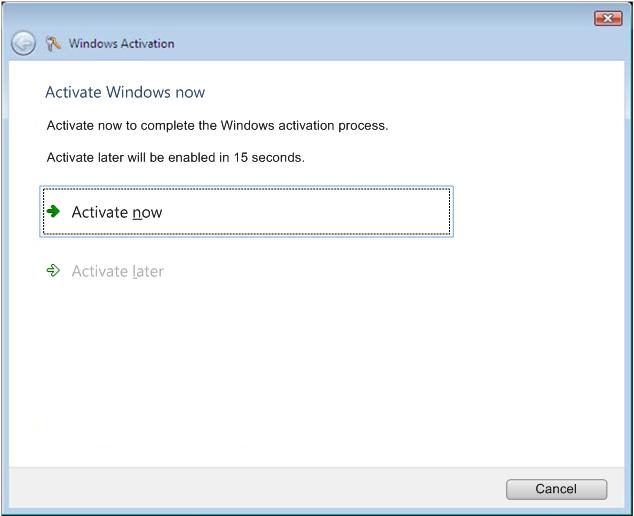
After the activation grace period has been exceeded the next logon will present the user with a message that directs the customer to activate that copy of Windows. That dialog includes a fifteen second delay before it can be dismissed. If a customer chooses to activate that copy of Windows they will be shown a number of ways to accomplish that. If they want to skip activation at that time they can wait for the fifteen seconds and choose "Activate Later" and they will be logged in to their desktop.
When the desktop is loaded, the background wallpaper color will be set to black. This setting will be confirmed and reset every hour meaning that a user can change the wallpaper to a favorite image but each hour after being logged in, the system will reset the desktop background to black. When that happens, a system tray balloon notification will advise the customer to activate their copy of Windows.
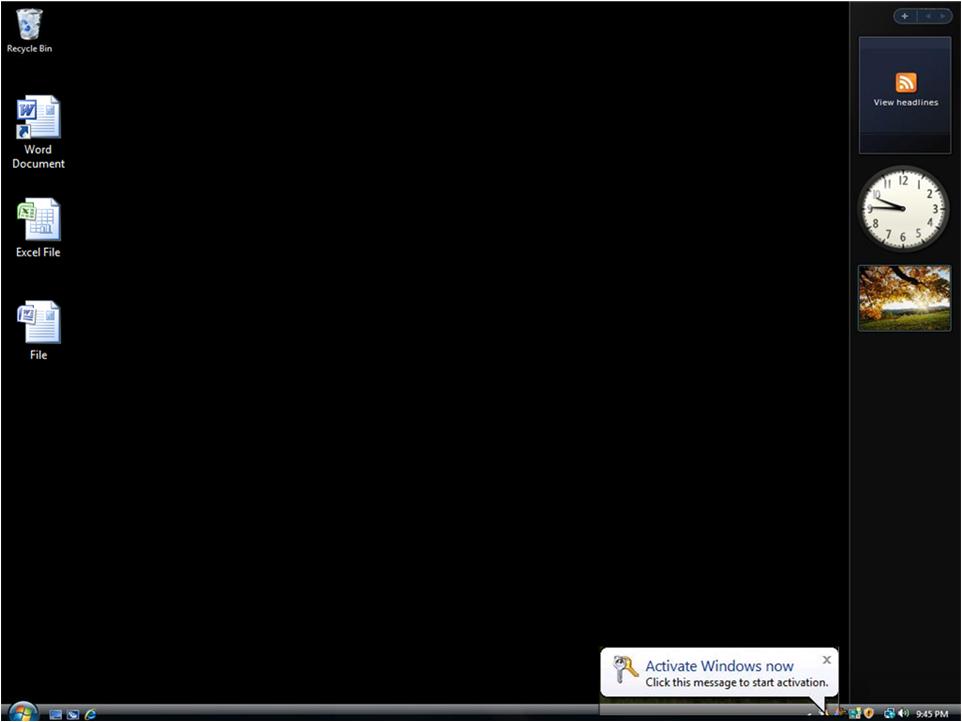
Again, if the user clicks the Activate message they will be presented with a number of ways to activate their copy of Windows.
Ok, you say, that's great but you've said this all before? How often is this likely to happen to the average customer? Well, in SP1 we will disable two of the most common exploits to our product activation technology. This means that users who have the exploits loaded on their systems will find those exploits disabled by SP1, and they will be asked to activate their copy of Windows Vista.
Here's how that's going to work.
Users of Windows Vista Service Pack 1 who previously had bypassed activation with the OEM BIOS or Grace Timer exploits should expect to find those exploits disabled by Windows. Once these exploits are disabled, the users will be prompted to activate their copy of Windows. If a customer doesn't activate within the required grace period they will receive frequent notifications alerting them that their system may not be genuine and what they need to do. The timing of when customers will first see the "Activate Your Copy of Windows" message can vary depending on what exploit is running on their system. Customers whose systems have the OEM BIOS exploit, for example, may not see anything for 15 days due to the way activation was set up for our OEM partners. Systems that have the Grace Timer exploit will be immediately prompted to activate once SP1 is installed.
So what about customers who DON'T install SP1 for a while? Is there some way they can tell if they're running one of these exploits? Why yes, in fact, there is.
Later this month Microsoft will release an update to Windows Vista through Windows Update that will enable Gold and SP1-installed systems to detect the presence of the Grace Timer and OEM BIOS exploits then alert the customer of their presence. The dialog box (shown below) also provides customers with guidance about what they can do to fix it and provides a Web link for more details, so that customers can learn about the particular exploit and learn how to disable and remove it. If they are a victim of software piracy, the linked Web pages will provide information on how to get genuine software.
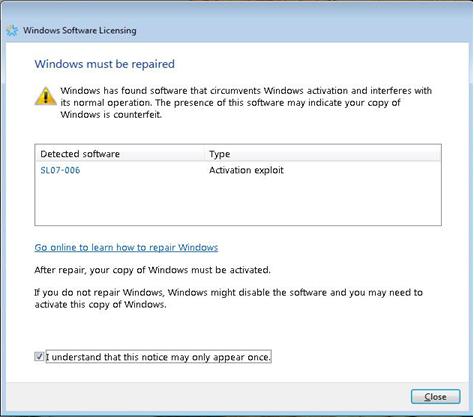
It's important to note that this update does not disable the exploits it finds –it simply alerts customers that exploits exist. When we first release the update that enables Windows Vista to detect the exploits we will also make available a separate removal tool as a download. In the future we will integrate the removal of the exploits with the detection. I'm expecting to see that integration in our next release. We also wanted to minimize any interruption for genuine customers so if a Windows Vista customer does not have an exploit on their system, they won't see any dialog box after the update is applied. It's that simple.
By providing this kind of technology, we want to make sure our customers are able to have the best Windows experience possible.
As always, I welcome your feedback.