Leveraging OMS Log Search to Track Policy and Permission Changes
In this post, we look at how we can leverage the Security and Audit solution in OMS and using log searches to track changes in audit policies and account permissions based on the audit events theAudit Collection Services (ACS) in OpsMgr collects and reports on.
In ACS, there are 4 Policy related SSRS audit reports available out-of-the-box that allow the user to track policy and permission changes in their IT environment:
- The Policy: Account Policy Changed Report,
- The Policy: Audit Policy Changed Report,
- The Policy: Object Permissions Changed, and
- The Policy: Privilege Added Or Removed
The Security and Audit solution in OMS Log Analytics however provides a comprehensive view into your organization’s IT security posture with built-in search queries for notable issues that require your attention.
Adding the Security and Audit solution to an OMS workspace will allow Windows security events, Windows application events, and Windows firewall logs to be collected using direct agents or MMA agents that the user enabled.
For further information, refer to Security and Audit solution in Log Analytics by Bill Anderson.
To retrieve and analyze the security events highlighted by these 4 ACS Audit Reports in OMS Log Analytics, the SQL query search conditions used in these reports can be used as the filter expressions in OMS log search queries against records collected by the Security and Audit solution.
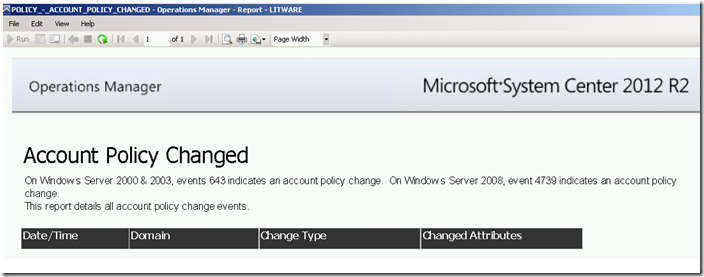
Policy: Account Policy Changed Report:
The report returns information on account policy changes in the domain within a given date/time range by searching for security event 4739 stored in the ACS database.
Running this report for a specific date/time range via the Reporting workspace in the OpsMgr Operations Console or the Reporting site will produce the following SSRS Report:
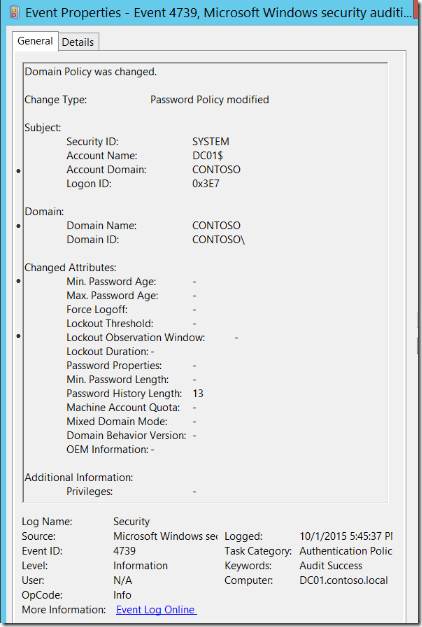
Here is an example of a 4739 – Domain Policy was changed security event as shown at the Windows Security Auditing technical documentation on TechNet:
For more information about Event 4739, visit https://technet.microsoft.com/en-us/itpro/windows/keep-secure/event-4739
The main part of the SQL query used in the RDL file of the Account Policy Changed Report is:
| SELECT *FROM AdtServer.dvAllWHERE (EventId = 643 OR EventId = 4739) AND (CreationTime >=@StartDate) AND (CreationTime <= @EndDate) |
The search condition from this SQL Query can be used as the filter expression of OMS log searches against Security and Audit solution records like the following example:
A search query to return all records of type SecurityEvent with EventID field containing 643 or 4739, limiting the result to the Activity, Computer, TimeGenerated and EventData fields:
SecurityEvent
| where EventID==643 or EventID==4739
| project Computer, Activity, TimeGenerated, EventData
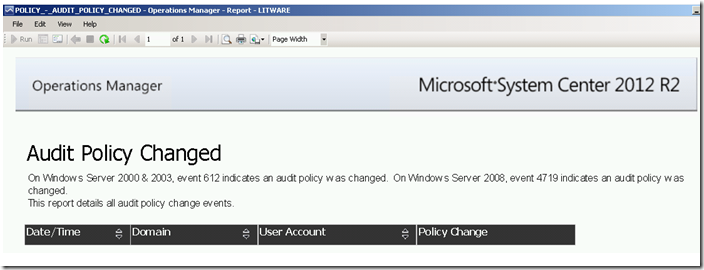
Policy: Audit Policy Changed Report
The report returns information on system audit policy changes within a given date/time range by searching for security event 4719 stored in the ACS database.
Running this report for a specific date/time range via the Reporting workspace in the OpsMgr Operations Console or the Reporting site will produce the following SSRS Report:
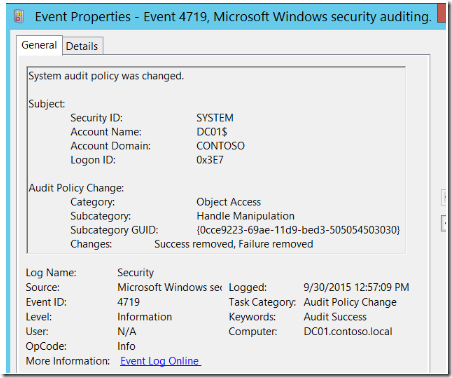
Here is an example of a 4719 – System audit policy was changed security event as shown at the Windows Security Auditing technical documentation on TechNet:
For more information about Event 4719, visit https://technet.microsoft.com/en-us/itpro/windows/keep-secure/event-4719
The main part of the SQL query used in the RDL file of the Audit Policy Changed Report is:
|
SELECT *FROM AdtServer.dvAll AS dvAll_1WHERE (EventId = 4719) AND (CreationTime >= @StartDate) AND (CreationTime <= @EndDate) |
The search condition from this SQL Query can be used as the filter expression of OMS log searches against Security and Audit solution records like the following example:
A search query to return all records of type SecurityEvent with EventID field containing 612 or 4719, limiting the result to the Activity, Computer, TimeGenerated and EventData fields:
SecurityEvent
| where EventID==612 or EventID==4719
| project Computer, Activity, TimeGenerated, EventData
SELECT *FROM AdtServer.dvAllWHERE (EventId = 4670) AND (CreationTime >= @StartDate) AND (CreationTime <= @EndDate) |
The search condition from this SQL Query can be used as the filter expression of OMS log searches against Security and Audit solution records like the following example:
A search query to return all records of type SecurityEvent with EventID field containing 4670, limiting the result to the Activity, Computer, TimeGenerated and EventData fields:
SecurityEvent
| where EventID==4670
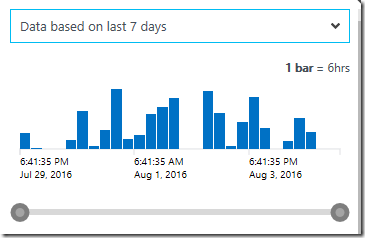
| project TimeGenerated, Activity, Computer, EventDataHere is an example of what would be shown on the time selector in the user interface of the portal if this log search query found some matching records:
SELECT * FROM AdtServer.dvAll AS dvAll_1WHERE (EventId = 4704 OR EventId = 4705) AND (CreationTime >= @StartDate) AND (CreationTime <= @EndDate) |
The search condition from this SQL Query can be used as the filter expression of OMS log searches against Security and Audit solution records like the following example:
A search query to return all records of type SecurityEvent with EventID field containing 621 or 622 or 4704 or 4705, limiting the result to the TimeGenerated, Activity and EventData fields:
SecurityEvent
| where EventID between (608 .. 609) or EventID between (621 .. 622) or EventID between (4704 .. 4705)
| project TimeGenerated, Activity, Computer, EventData
To view the complete mapping between all Audit Collection Services (ACS) SSRS reports and search queries used in OMS Log Analytics, refer to:
https://blogs.msdn.microsoft.com/wei_out_there_with_system_center/2016/07/25/mapping-acs-reports-to-oms-search-queries/