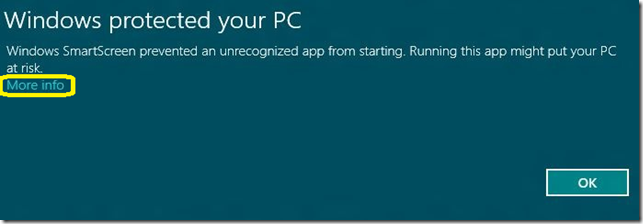
Windows SmartScreen prevented an unrecognized app from running. Running this app might put your PC at risk
When you try to install a ClickOnce application on Windows 8 OS, it is intercepted by the SmartScreen filter. It would show the below screenshot:
Though the application is signed with a certificate from Verisign, still the publisher name is displayed as unknown. SmartScreen dialog should be the same as for any other executable, with a "More Info" option, and "Run Anyway" button. Windows SmartScreen alerts users before running unrecognized programs downloaded from the Internet. Microsoft has extended the SmartScreen feature of Internet Explorer to Windows as well to protect users from malware. In general, SmartScreen Protection shows the above message when you try to run a newly released program or an application that has not yet established a reputation. Even though one can easily disable the SmartScreen Protection feature in Windows 8, we don’t advise you to turn off the protection.
In addition to Strong Name signing the assembly, which VS offers support for (via project property pages), you will need to Authenticode sign. There is no direct support for Authenticode signing from Visual Studio; however, it’s easy to add as a post-build step, like so, by inserting these lines into your project file:
<Target Name="BeforePublish">
<Exec Command=""$(WindowsSdkDir)bin\signtool.exe" sign
/f "path_to_your_certificate"
/d signed_content_description
/du signed_content_URL
/t https://timestamp.(vendorwebsite)
/v "path_to_your_exe (in the obj\$(ConfigurationName) directory)"" />
</Target>
The /d is a string description and /du is an url that points to additional description. These two are optional parameters.
Example:
<TargetName="BeforePublish">
<ExecCommand=""C:\Program Files (x86)\Microsoft SDKs\Windows\v7.1A\Bin\signtool.exe" sign /f "MyCert.pfx" /p "password" /t https://timestamp.verisign.com/scripts/timstamp.dll "C:\Projects\obj\Release\App.exe"" />
</Target>
Once this is done, the SmartScreen will continue to warn about the application until the certificate develops a reputation. But it would display a valid publisher name instead of unknown publisher.
*P.S. The goal of the Application Reputation experience is to warn users, when appropriate, that a downloaded application has not yet established a reputation.
Reputation is established by SmartScreen® service intelligence algorithms based on how an application is used by Windows and Internet Explorer users. Reputation may be based on the downloaded application or can also be assigned to the publisher based on digital certificate information. Only Authenticode Certificates issued by a CA that is a member of the Windows Root Certificate Program can establish reputation. Digital certificates allow data to be aggregated and assigned to a single certificate rather than many individual programs. Although not required, programs signed by an EV code signing certificate* can immediately establish reputation with SmartScreen reputation services even if no prior reputation exists for that file or publisher. EV code signing certificates also have a unique identifier which makes it easier to maintain reputation across certificate renewals.
At this time, both Symantec and DigiCert are offering EV code signing certificates as described in the blog Microsoft SmartScreen & Extended Validation (EV) Code Signing Certificates