Restrict the website for a particular Crypto Protocol
I have seen this issue several times and thought I would blog about it for everyone’s benefit.
Enterprises have their preference of restricting their website to a particular cryptographic protocol/algorithm and hence would like to disable other.
Here is a very good knowledge base article Article ID: 245030 for the same but it hasn’t mentioned anything about Windows Server 2008. Let me tell you the article holds true for Windows Server 2008 as well.
Just recently a customer wanted to disable all but SSL 3.0 for their website on the server.
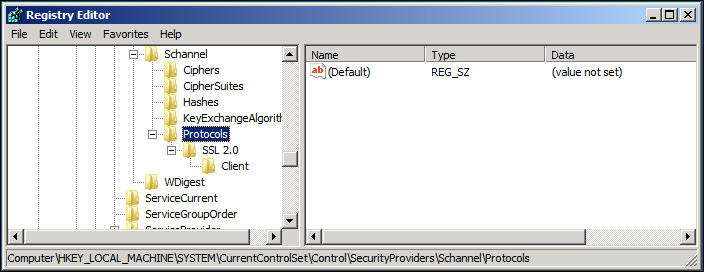
Open Registry Editor (regedit.exe) and go to HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\Schannel\Protocols on Windows Server 2008, you will see the following entry By Default.
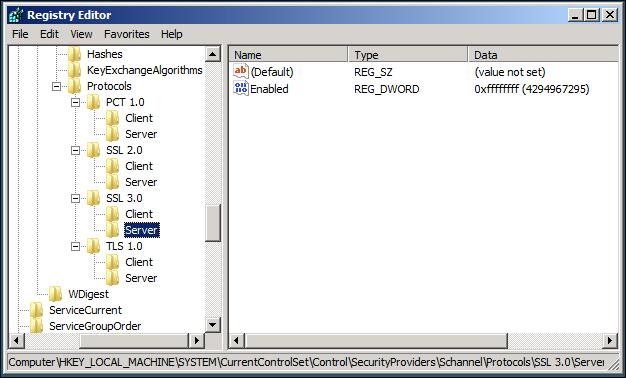
You will have to add the following keys..
- PCT 1.0\Client
- PCT 1.0\Server
- SSL 2.0\Client
- SSL 2.0\Server
- SSL 3.0\Client
- SSL 3.0\Server
- TLS 1.0\Client
- TLS 1.0\Server
Create a DWORD "Enabled"=dword:00000000 to Disable and "Enabled"=dword:ffffffff to Enable the above protocol.
Here is a simple test to verify the same:
Open Internet Explorer, go to Tools –> Internet Options –> Advanced under Security you will see Use SSL 2.0, Use SSL 3.0 and Use TLS 1.0.
I have enabled only SSL 3.0 in the registry and hence would uncheck all but Use SSL 2.0. Browse the website and I get “Internet Explorer cannot display the webpage”. Good.
Now select SSL 3.0 and uncheck all others and now the webpage is displayed on https. Run the sniffer tool and you can verify that the server is now opened for SSL 3.0 only.
Good luck :)…