Spectre mitigation changes in Visual Studio 2017 Version 15.7 Preview 3
With Visual Studio 2017 version 15.7 Preview 3 we have two new features to announce with regards to our Spectre mitigations. First, the /Qspectre switch is now supported regardless of the selected optimization level. Second, we have provided Spectre-mitigated implementations of the Microsoft Visual C++ libraries.
Complete details are available in context in the original MSVC Spectre mitigation post on VCBlog. Changes in Update 3 are also listed below.
In previous versions of MSVC we only added Spectre mitigations when code is being optimized. In Visual Studio 2017 version 15.7 Preview 3 we’ve added support for /Qspectre regardless of your optimization settings. This feature is currently only available in Visual Studio version 15.7 Preview 3 and future releases.
We’re also adding Spectre-mitigated implementations of the Microsoft Visual C++ libraries. Visual Studio 2017 version 15.7 Preview 3 includes runtime libraries with mitigation enabled for a subset of the Visual C++ runtimes: VC++ start-up code, vcruntime140, msvcp140, concrt140, and vcamp140. We also include static library equivalents of those libraries. We are providing static linking support and App Local deployment only; the contents of the Visual C++ 2017 Runtime Libraries Redistributable have not been modified.
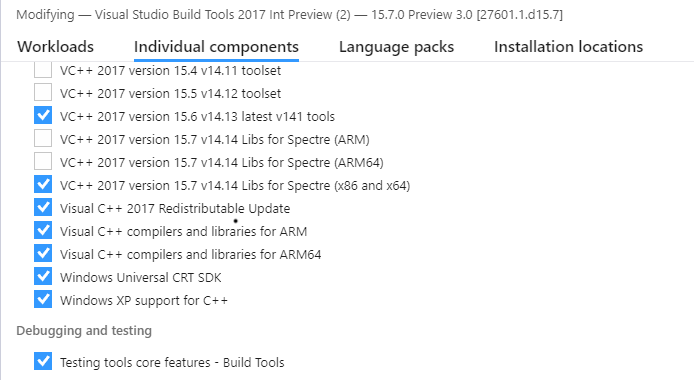
You must select these libraries for installation in the VS Installer under the Individual Components tab:
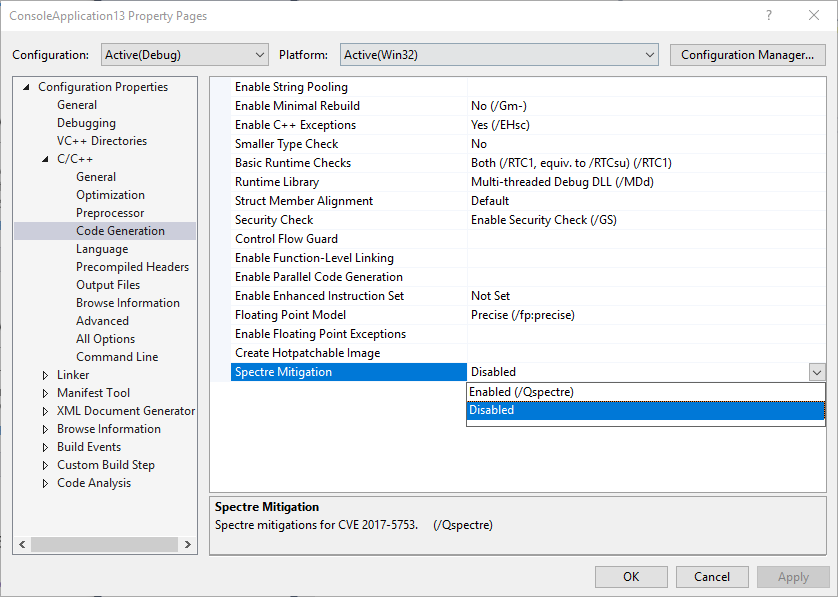
To enable Spectre mitigations for both your code and library code, simply select “Enabled” under the “Code Generation” section of the project Property Pages:
Current status
The following table shows the status of supported features in the versions of Visual Studio with Spectre mitigations available in the MSVC toolset:
| Visual Studio Version (as of April 4, 2018) | /Qspectre with optimizations | /Qspectre without optimizations | X86 and Amd64 | Arm and Arm64 | Mitigated libs |
|---|---|---|---|---|---|
| VS 2015 Update 3 | — | — | — | — | — |
| VS 2017 RTW 15.0 (26228.23) | ✔ | — | ✔ | — | — |
| VS 2017 15.5.5 | ✔ | — | ✔ | — | — |
| VS 2017 15.6 | ✔ | — | ✔ | ✔ | — |
| VS 2017 15.7 | ✔ | ✔ | ✔ | ✔ | ✔ |
In closing
We on the MSVC team are committed to the continuous improvement and security of your Windows software which is why we have taken steps to enable developers to help mitigate variant 1. We encourage you to recompile and redeploy your vulnerable software as soon as possible. Continue watching this blog and the @visualc Twitter feed for updates on this topic.
If you have any questions, please feel free to ask us below. You can also send us your comments through e-mail at visualcpp@microsoft.com, through Twitter @visualc, or Facebook at Microsoft Visual Cpp. Thank you.

 Light
Light Dark
Dark
0 comments