Windows Identity Foundation Tools for Visual Studio 11 Part III: Connecting With a Business STS (e.g. ADFS2)
Welcome to the third walkthrough of the new WIF tools for Visual Studio 11 Beta! This is about using the tools to trust a business identity provider, such as an ADFS2 instance.
The complete series include Using the Local Development STS, manipulating common config settings, connecting with a business STS, get an F5 experience with ACS2.
Let’s say that you downloaded the new WIF tools (well done! ![]() ) and you went through at least the first walkthrough. All this testing stuff sounds interesting, but you actually need to federate with a “real” identity provider, say your local ADFS2 instance.
) and you went through at least the first walkthrough. All this testing stuff sounds interesting, but you actually need to federate with a “real” identity provider, say your local ADFS2 instance.
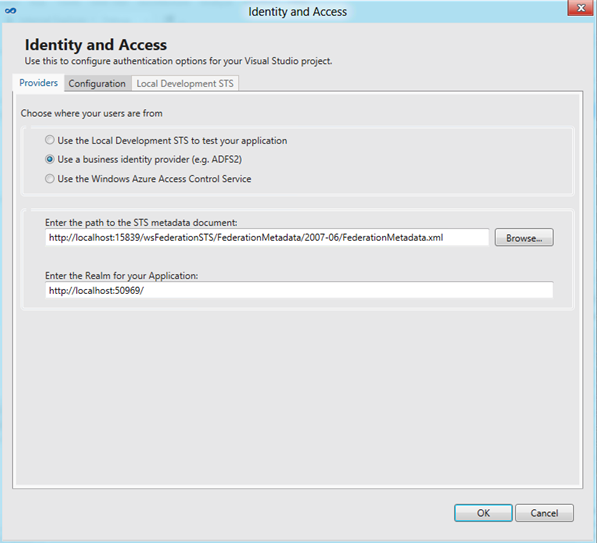
That’s the basic functionality that was offered by the tools in v1, and of course we still have it: if you pick “Use a business identity provider (e.g. ADFS2)” in the Providers tab you’ll get right to in.
Below you can see the UI already populated with the values of the Local STS, from the first walkthrough: WSFed-wise, for WIF an IP is an IP regardless of if it is an actual one or a test endpoint.
Here we retain the “dev environment” approach, in which we don’t nag you too much for the lack of HTTPS and we relax security conditions for you (remember, this is NOT for production environments: you got to harden things before deploying).This is why we are able to collapse the 4 or 5 screens you had to traverse with the v1 of the tools in a single experience as shown below. However ADFS2 itself is not that forgiving, hence in order to establish a relying party trust you’ll likely have to get down to business and install valid certificates, use naming that can be addressed from different machines, and so on. There’s not much that the tools can do there to help, this is the one case where you still need to be proficient with identity matters in order to get things to work even in a dev environment.
What do you think? Did we simplify too much? Too little? Let us know!
Don’t forget to check out the other walkthroughs: the complete series include Using the Local Development STS, manipulating common config settings, connecting with a business STS, get an F5 experience with ACS2.