Windows Identity Foundation in the .NET Framework 4.5 Beta: Tools, Samples, Claims Everywhere
The first version of Windows Identity Foundation was released in November 2009, in form of out of band package. There were many advantages in shipping out of band, the main one being that we made WIF available to both .NET 3.5 and 4.0, to SharePoint, and so on. The other side of the coin was that it complicated redistribution (when you use WIF in Windows Azure you need to remember to deploy WIF’s runtime with your app) and that it imposed a limit to how deep claims could be wedged in the platform. Well, things have changed. Read on for some announcements that will rock your world!
No More Moon in the Water
With .NET 4.5, WIF ceases to exist as a standalone deliverable. Its classes, formerly housed in the Microsoft.IdentityModel assembly & namespace, are now spread across the framework as appropriate. The trust channel classes and all the WCF-related entities moved to System.ServiceModel.Security; almost everything else moved under some sub-namespace of System.IdentityModel. Few things disappeared, some new class showed up; but in the end this is largely the WIF you got to know in the last few years, just wedged deeper in the guts of the .NET framework. How deep?
Very deep indeed.
To get a feeling of it, consider this: in .NET 4.5 GenericPrincipal, WindowsPrincipal and RolePrincipal all derive from ClaimsPrincipal. That means that now you’ll always be able to use claims, regardless of how you authenticated the user!
In the future we are going to talk more at length about the differences between WIF1.0 and 4.5. Why did we start talking about this only now? Well, because unless your name is Dominic or Raf chances are that you will not brave the elements and wrestle with WS-Federation without some kind of tool to shield you from the raw complexity beneath. Which brings me to the first real announcement of the day.
Brand New Tools for Visual Studio 11
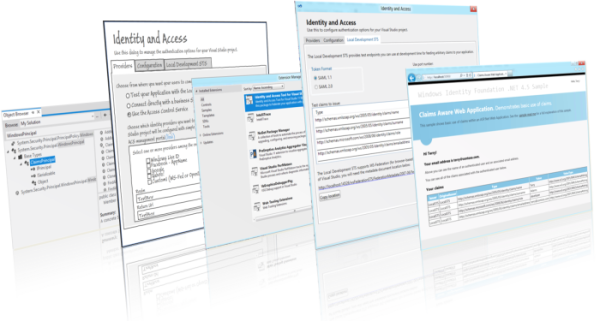
I am very proud to announce that today we are releasing the beta version of the WIF tooling for Visual Studio 11: you can get it from here, or directly from within Visual Studio 11 by searching for “identity” directly in the Extensions Manager.
The new tool is a complete rewrite, which delivers a dramatically simplified development-time experience. If you are interested in a more detailed brain dump on the thinking that went in this new version, come back in few days and you’ll find a more detailed “behind the scenes” post. To give you an idea of the new capabilities, here there are few highlights:
- The tool comes with a test STS which runs on your local machine when you launch a debug session. No more need to create custom STS projects and tweaking them in order to get the claims you need to test your apps! The claim types and values are fully customizable. Walkthrough here
- Modifying common settings directly from the tooling UI, without the need to edit the web.config. Walkthrough here
- Establish federation relationships with ADFS2 (or other WS-Federation providers) in a single screen. Walkthrough here
- My personal favorite. The tool leverages ACS capabilities to offer you a simple list of checkboxes for all the identity providers you want to use: Facebook, Google, Live ID, Yahoo!, any OpenID provider and any WS-Federation provider… just check the ones you want and hit OK, then F5; both your app and ACS will be automatically configured and your test application will just work. Walkthrough here
- No more preferential treatment for web sites. Now you can develop using web applications project types and target IIS express, the tools will gracefully follow.
- No more blanket protection-only authentication, now you can specify your local home realm discovery page/controller (or any other endpoint handling the auth experience within your app) and WIF will take care of configuring all unauthenticated requests to go there, instead of slamming you straight to the STS.
Lots of new capabilities, all the while trying to do everything with less steps and simply things! Did we succeed? You guys let us know!
In V1 the tools lived in the SDK, which combined the tool itself and the samples. When venturing in Dev11land, we decided there was a better way to deliver things to you: read on!
New WIF Samples: The Great Unbundling
If you had the chance to read the recent work of Nicholas Carr, you’ll know he is especially interested on the idea of unbundling: in a (tiny) nutshell, traditional magazines and newspapers were sold as a single product containing a collection of different content pieces whereas the ‘net (as in the ‘verse) can offer individual articles, with important consequences on business models, filter bubble, epistemic closure and the like (good excerpt here).
You’ll be happy to know that this preamble is largely useless, I just wanted to tell you that instead of packing all the samples in a single ZIP you can now access each and every one of them as individual downloads, again both via browser (code gallery) or from Visual Studio 11’s extensions manager. The idea is that all samples should be easily discoverable, instead of being hidden inside an archive; also, the browse code feature is extremely useful when you just want to look up something without necessarily download the whole sample .
Also in this case we did our best to act on the feedback you gave us. The samples are fully redesigned, accompanied by exhaustive readmes and their code is thoroughly documented. Ah, and the look&feel does not induce that “FrontPage called from ‘96, it wants his theme back” feeling ![]() . While still very simple, as SDK samples should be, they attempt to capture tasks and mini-scenarios that relate to the real-life problems we have seen you using WIF for in the last couple of years.
. While still very simple, as SDK samples should be, they attempt to capture tasks and mini-scenarios that relate to the real-life problems we have seen you using WIF for in the last couple of years.
- ClaimsAwareWebApp
This is the classic ASP.NET application (as opposed to web site), demonstrating basic use of authentication externalization (to the local test STS from the tools). - ClaimsAwareWebService
Same as above, but with a classic WCF service. - ClaimsAwareMvcApplication
This sample demonstrates how to integrate WIF with MVC, including some juicy bits like non-blanket protection and code which honors the forms authentication redirects out of the LogOn controller. - ClaimsAwareWebFarm
This sample is an answer to the feedback we got from many of you guys: you wanted a sample showing a farm ready session cache (as opposed to a tokenreplycache) so that you can use sessions by reference instead of exchanging big cookies; and you asked for an easier way of securing cookies in a farm.
For the session cache we included a WCF-based one: we would have preferred something based on Windows Azure blob storage, but we are .NET 4.5 only hence for the time being we went the WCF service route.
For the session securing part: in WIF 4.5 we have a new cookie transform based on MachineKey, which you can activate by simply pasting the appropriate snippet in the config. The sample demonstrates this new capability. I think I can see Shawn in the audience smiling from ear to ear, or at least that’s what I hope
Note: the sample itself is not “farmed”, but it demonstrates what you need for making your app farm-ready. - ClaimsAwareFormsAuthentication
This very simple sample demonstrates that in .NET 4.5 you get claims in your principals regardless of how you authenticate your users. It is a simple sample, no alliteration intended, but it makes an important point. You can of course generalize the same concept for other authentication methods as well (extra points… ehhm.. claims, if you are in a Windows8 domain and you do Kerberos authentication) - ClaimsBasedAuthorization
In this sample we show how to use your CLaimsAuthorizationManager class and the CLaimsAuthorizationModule for applying your own authorization policies. We decided to keep it simple and use basic conditions, but we are open to feedback! - FederationMetadata
In this sample we demonstrate both dynamic generation (on a custom STS) and dynamic consumption (on a very trusty RP: apply this with care!) of metadata documents. As simple as that. - CustomToken
Finally, we have one sample showing how to build a custom token type. Not that we anticipate many of you will need this all that often, but just in case…
We factored the sample in a way that shows you how you would likely consume an assembly with a custom token (and satellite types, like resolvers) from a claims issuer (custom STS) and consumer (in this case a classic ASP.NET app). Ah, and since we were at it, we picked a token type that might occasionally come in useful: it’s the Simple Web Token, or SWT.
Icing on the case: if you download a sample from Visual Studio 11, you’ll automatically get the WIF tools ![]() . Many of the samples have a dependency on the new WIF tools, as every time we need a standard STS (e.g. we don’t need to show features that can be exercised only by creating a custom STS) we simply rely on the local STS.
. Many of the samples have a dependency on the new WIF tools, as every time we need a standard STS (e.g. we don’t need to show features that can be exercised only by creating a custom STS) we simply rely on the local STS.
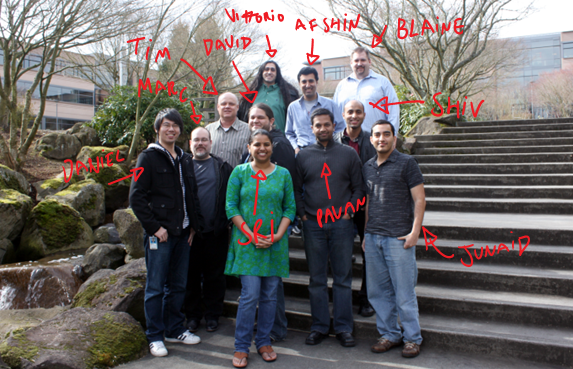
The Crew!!!
Normally at this point I would encourage you to go out and play with the new toys we just released, but while I have your attention I would like to introduce you to the remarkable team that brought you all this, as captured at our scenic Redwest location:
…and of course there’s always somebody that does not show up at picture day, but I later chased them down and immortalized their effigies for posterity:
Thank you guys for an awesome, wild half year! Looking forward to fight again at your side ![]()