Identity @ Tech.Ed Australia & New Zealand


Ah nice. Sunday night, 1:00am and I am still perfectly awake… the usual jet lag after vacation (3 hours for actual time zone difference, + 3 hours because in vacation I like to “recuperate” the lost sleep during the year ;-)).
I am not brave enough to open the email yet, who knows what’s awaiting for me there, so I’ll just write down few lines about my next trip. I am really happy to report that I’ve been summoned again to present at TechEd Australia and TechEd New Zealand on my favourite topic! Last year it was a blast, awesome audiences and great, great places, and I really look forward to get there and blabber about identity, claims & company. I’ll meet customers in Melbourne & Sydney, then I’ll head to Gold Coast and from there to Auckland. I’ll have exactly 0 (zero) time to take a look around, in fact I’ll have to head back ASAP, but that’s more the rule than the exception… that’s how we roll ;-)
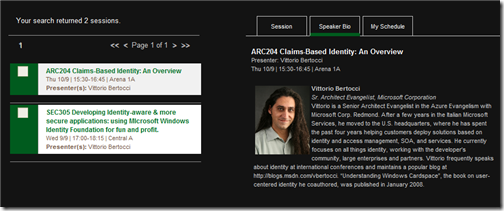
I am scheduled to deliver the same 2 sessions in both events: one (ARC204) will be a classic intro to claims-based identity, the other (SEC305) will be a drilldown in WIF. Here there are titles, days, locations & abstracts:
ARC204 Claims-Based Identity: An Overview
Australia: Thu 10/9 | 15:30-16:45 | Arena 1A
New Zealand: Wed 9/16 | 10:45-12:00 | Marlborough Room
For people who create software today, working with identity isn't much fun. There are too many technologies and too much complexity. The industry-wide shift toward claims-based identity improves this, offering a better, simpler approach. Yet making this approach real requires infrastructure, which is why Microsoft is enhancing its platform with AD FS 2.0, Windows Identity Foundation and Windows CardSpace 2.0. This session provides an overview of these forthcoming identity technologies, showing the problems each one addresses and how they relate to one another. The goal is to provide a big-picture understanding of Microsoft's approach to claims-based identity.
It’s been really long since I didn’t give a 200… preparing it will be fun! Nigel, I am not sure I won’t slip to 300 here and there… I’ll try to minimize those moments, I promise!
SEC305 Developing Identity-aware & more secure applications: using Microsoft Windows Identity Foundation for fun and profit.
Australia: Wed 9/9 | 17:00-18:15 | Central A
New Zealand: Tue 9/15 | 14:20-15:35 | New Zealand Room 3
Application developers, meet Mr. 'separation of concerns'. Thanks to its support of claims-based identity, the Windows Identity Foundation (formerly Geneva) APIs allow you to eliminate from your application all authentication- and authorization- specific code, by delegating its function to external entities. The application developer retains access to all the user attributes that are needed for driving the experience or feeding the business logic, without the burden of knowing anything about the underlying security plumbing. The security architect can secure an application simply by manipulating its config file at deployment time, or decide to take full control of the process and easily develop custom authentication and authorization logic. This session provides an overview of how to use Windows Identity Foundation for comfortably achieving the above in interoperable, location-independent fashion.
I am very grateful to Rocky for having allowed me the lighthearted title & abstract :-) you know, that may even be the first session that uses WIF instead of Geneva Framework.
Aaall right. I’m really looking forward to be there, as usual feel free to grab me at any time if you see me around and you want to talk identity!