A Guide for Enabling Federated Authentication on Windows Azure WebRoles… using Windows identity Foundation
UPDATE: the guide here has long been superceded by hands-on labs (specifically this one) and whitepapers on the topic. Please use those instead.
==========================================
Federating with customer and partners, SSO using existing company identities, authentication externalization, multiple auth factors, claims-based identity… those are all things that the good architects, developers & sysadmins want to be able to do on-premises, in the cloud and in whatever lies between.
Our products are still in prerelease status, however we know that many of you are experimenting with the new possibilities offered by the cloud… and not being able to include federated identity in your scenario can be a big limiting factor.
In order to help you with that Hervey, architect on the Federated Identity team, took a good look at the current bits at your disposal (Windows Azure July 2009 CTP, Geneva Framework Beta 2) and developed some code extending Windows Identity Foundation can help you to overcome some of the incompatibilities so that you can experiment with claims based identity in Windows Azure. Then I took that code and made it into a step-by-step guide, that can be used by *anybody* for enabling passive federation in a Windows Azure WebRole for experimental purposes and can be used by identity experts for gaining insights on what are the attention points that require workarounds in the currently available bits.
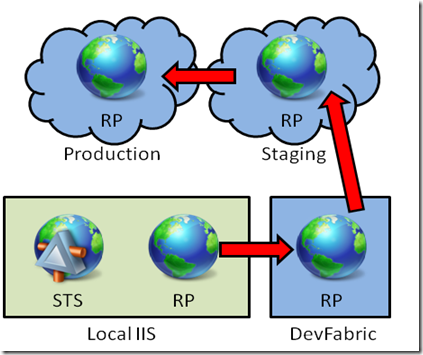
Here there’s a summary of the steps followed by the guide. You start by creating an ASP.NET website (RP) in the local IIS and auto-generate an STS for it, all by using the usual Windows Identity Foundation tools. Once verified that it works as expected in the local IIS, you create a Cloud Service project and transfer the RP settings to a new WebRole: then you test it in the DevFabric. Upon successful testing you publish & test the WebRole in staging and finally in production.
Note that the guide aims at describing the most basic of the scenarios and requiring minimal system requirements, but you can easily use it as starting point for building something more realistic, for example by using your own AD FS 2.0 as the identity provider instead of the development STS we leverage.
The guide package is available for download on Code Gallery, direct link here.
We will keep updating this guide and its supporting code (Microsoft.IdentityModelPlus) as new releases of the products involved become available; we also plan to release other guides for addressing different scenarios, such as the active case (claims-based identity with WCF services in WAz), perhaps even an STS in the cloud! We look forward to your feedback: please remember that this code is NOT production ready, and it is released to you for the sole purpose of allowing you to experiment with identity and cloud based scenarios.
That’s all: time to jump in action! Download the guide package and have fun with identity and the cloud :-) Happy coding!