Block Ciphers: Simple attack on ECB mode
This is nothing new, but I just wanted to document it on my blog. Block ciphers encrypt data in blocks of bits. These blocks are generally 64 or 128 bits long. In the ECB (or Electronic Code Book) mode, each block is encrypted independently of the other blocks. As a result if two blocks are same, the same cipher text results. This enables the attacker to figure out all instances of a plaintext if that plaintext-cipher text pair is known and the cipher text is repeating. An attack based on the frequency analysis of the blocks is also possible. Frequently repeating cipher text blocks mean frequently repeating plain text blocks.
I will show the effects of another simple attack. In this case consider that the plain text is "Give Jo one two one two dollars". Note that I have purposely divided the message into blocks of 8 characters (or 64 bits in ASCII). "Give Jo " is the first block, "one two " is the next and so on.
Now I will use the DESCryptoServiceProvider class to encrypt this plaintext using ECB mode. The code used to encrypt is available here. The only difference is that I have changed the mode to ECB, and the block size to 64 bits for this demo to work.
After encrypting the plain text, the cipher text received is:-
First of all note the repeated block because of ECB. "one two one two" (from the plain text) consists of two blocks of 64 bits each. These blocks give identical cipher text blocks because of ECB.
Now consider if an attacker removes one of these blocks. This is the cipher text after removing one of the repeating blocks.
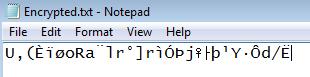
If I decrypt this cipher text, using the same code (and key) I get:-
Notice that the decryption was possible and successful, but the plain text is now different from the original plain text. Jo now gets lot less dollars ;)
Ofcourse these are the reasons why ECB mode is not preferred.