SharePoint 2013 Ports, Proxies and Protocols - An Overview of Farm Communications
In locked down environments, understanding communications paths of a server product is essential. Some time ago, Martin Kearn and Pete Reid published a great post describing farm communications in Microsoft Office SharePoint Server 2007 (MOSS). SharePoint 2013 isn’t that much different from MOSS 2007 with regard to network communication and protocols. It is still a web-based application based on the .NET Framework with dependencies on SQL Server, Active Directory and DNS. Most of the information in that article are therefore valid in SharePoint 2013 as well. I would recommend you to get familiar with those core concepts.
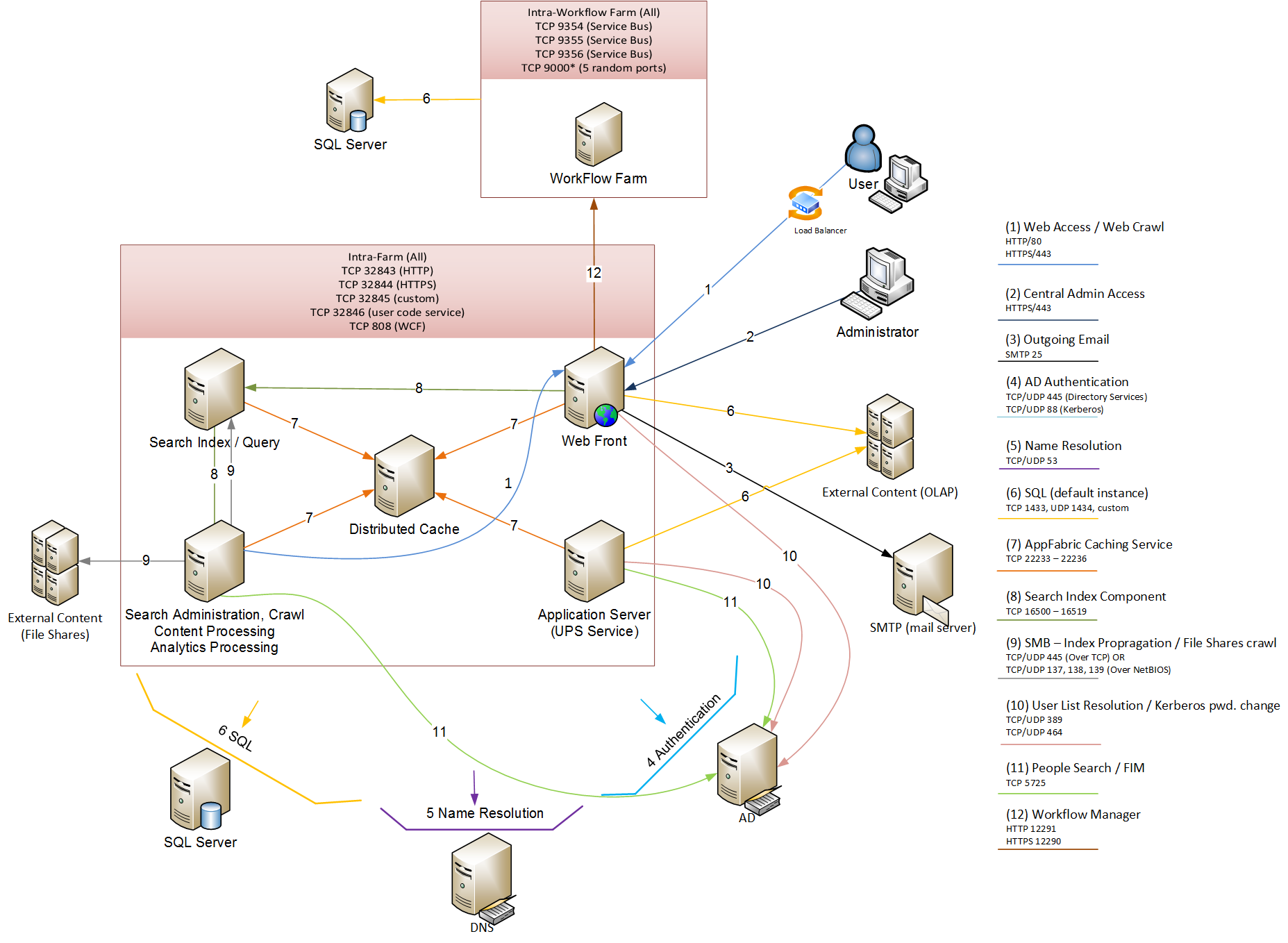
Whilst the fundamentals remain the same, there were changes in the product over time that have affected the inter and extra-server communications paths. SharePoint 2010 introduced the Service Application model with Windows Communication Foundation proxies and endpoints. SharePoint 2013 brings additional core-building blocks to the product such as Distributed Cache or optional components such as Office Web Apps Server and Workflow Manager with an underlying Service Bus. These components publish some sort of endpoint to communicate with SharePoint 2013 on different ports. You should not forget to secure communication with these external endpoints with a SSL certificate. SharePoint 2013 uses oAuth for Server to Server (S2S) communication and you absolutely don't want oAuth bearer tokens flying over your network in clear text. They contain sensitive information and any party in possession of a bearer token can use it to get access to the associated resource. You can find more information in The OAuth 2.0 Authorization Framework: Bearer Token Usage RFC 6750 document. Yes, this means you should have SSL certificates deployed on your SharePoint sites as well.
Below is an updated communication diagram for SharePoint 2013. I have combined both inter and extra server communications into a single diagram. I hope you will find it easy to navigate. A large version of this image can be found here.
References
Plan security hardening for SharePoint 2013
Using Windows Internet Explorer Developer Tools Network Capture
Marek Samaj
Senior Consultant
Microsoft Consulting Services UK
marek.samaj@microsoft.com
Click here to see my bio page