Seven things to know about Safety Tips
As I posted on this blog a couple of months ago, and as we posted on the Office blog last month, Office 365 is going to be releasing Safety Tips over the next few weeks. In this blog post, I go into more about how they work.
1. Outlook on the web has more Safety Tips than regular Outlook
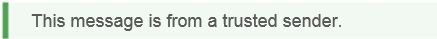
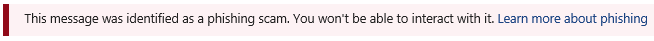
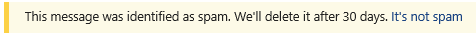
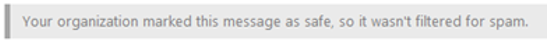
When you check your email using Outlook on the web (formerly known as Outlook Web Access, or OWA), there are four tips:
However, when checking your email in Outlook, you'll only see the red (Suspicious) Safety Tip:
We have plans to also roll out the yellow Safety Tip a few weeks from now.
2. It doesn't matter which version of Outlook you're using, you'll get Safety Tips automatically
Safety Tips in Outlook doesn't depend on what version of Outlook you're using because we crack open and insert the Safety Tip directly into the message body. That means that whatever email client you're using will show the Safety Tip. It's done at the email filter level and not rendered at the mail client level.
And that means that not only does it show up in any version of Outlook, it shows up in any email client. But for the purposes of this blog post, I will call them as checking safety tips in Outlook.
3. Think of Safety Tips in Outlook as "Safety Tattoos"
We think of safety tips, when checking them in Outlook, as safety "tattoos" because they stick with your message forever (almost). If you drag them from the Junk folder to the Inbox, or vice versa, the color of the tip doesn't change.
The only way to delete the tip is to open up the message, highlight it, and delete it.
In this blog post, Safety Tattoos means only the version that we insert inline into the message. Safety Tips refers to both Safety Tattoos and Safety Tips in Outlook on the web, I use it as a general name for the entire feature.
4. The tattoo doesn't show up in Outlook on the web
You may be thinking "If you're inserting the safety tip directly into the message, and you're rendering it in Outlook on the web, does this mean that if I check it in Outlook on the web that I'll see it twice?"
No.
Outlook on the web is smart enough to suppress the safety tattoo and instead show a rendered version of it that you can interact with. For example, the Outlook on the web one may say "Click here to enable blocked content." The safety tattoo does not because it does not have access to that part of the email client's rendering capabilities.
5. As an administrator, you can disable Safety Tattoos
The Exchange Admin Center lets you turn on or off Safety Tattoos, they will be on by default for both new and existing customers. We don't recommend it, but you can disable them by logging in and changing that setting.
You can't disable them in Outlook on the web, however. They also show up.
6. Safety Tips work best if your MX record points to Exchange Online Protection (EOP)
Not all customers point their MX records at EOP. Many point at a 3rd party service and then relay the email onto us. If you do that, Safety Tips won't work as well; they may be suppressed entirely. This robs your users of the additional safety experience of visual clues that something is wrong with the message.
7. The red (Suspicious) Safety Tip's criteria is continually expanding
The red safety tip has lots of different criteria that we are rolling out. Some of it is the same as in outlook.com, but much of it is unique to EOP. As we find more criteria that we think is suspicious -- phishing -- we'll add it to the tip. We don't plan to document every scenario for which we assign a red tip.
Those are the items I can currently think of. As we get more, I'll add them. Not sure about what to do with the title of the blog post when that happens, though.