Fallout from the Anonymous/Stratfor hack
As I wrote in my post on Christmas Day, Stratfor was hacked by Anonymous. Since that time, here are a couple of updates:
I signed up for Identity Theft protection from CSID. I got an alert the other day indicating that according to all of the monitoring they do, the email address I use for Stratfor was compromised. Oh, that’s just swell.
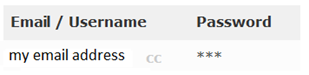
That very evening (Christmas Day, not the day I signed up at CSID), I cancelled my credit card and got a new one. As it turns out, that was a good idea. For you see, according to this website here, hacked Stratfor users can check to see if their information was leaked.
The ‘cc’ next to my name means that my credit card information was also leaked. Thanks, Anonymous. I appreciate you giving the world my financial data.
While I changed my credit card, I’m not sure what to do about my email address. I use it to login to a lot of sites. Luckily, the password I use is unique to Stratfor (I think). I have reused those two combinations in the past, but not in any websites that I currently care about. The fact that I don’t use it anymore is really a stroke of luck.
I suspect that the alert CSID sent me from point (1) has to do with the leaked email address from Anonymous. When I first got the alert, I was like “Shoot, what do I do?” Now that I think I know where it came from, I’m breathing a little easier since if that password is compromised, it doesn’t matter because I don’t use it with any website that is particularly important to me.
Stratfor released an update today about the status of what’s going on:
In monitoring fallout from the breach of security in Stratfor’s data systems, we have been made aware of false and misleading communications that could attempt to prey on the privacy concerns of our customers and friends. While Stratfor works to re-establish its data systems and web presence, we ask everyone to please consult the Stratfor Facebook page and Twitter feed for company-approved communications.
I haven’t seen any of this, but my bet is that spammers have been monitoring the story and have sent spoofed messages from Stratfor and Stratfor founder George Friedman. I’d further guess that the message contains links to malware, and that the spammers harvested the leaked emails that Anonymous posted and sent these targeted messages to Stratfor subscribers.<1 minute later>
M’kay, I checked my spam folder just now and there are five messages from (spoofing) Stratfor, all sent yesterday. It is a scam asking the user to rate Stratfor’s Incident Response (which, btw, I think has been pretty good):
From: george.friedman@<redacted>
Subject: Rate Stratfor’s Incident Response
Date: Thursday, Jan 5, 2012For the video announcement, please see https://www.youtube.com/<redacted> Read full press release: https://bolt.thexfil.es/<redacted> Rate Stratfor's incident response: https://<redacted>.imageshack.us/<redacted> Hello loyal Stratfor clients, We are still working to get our website secure and back up and running again as soon as possible. To show our appreciation for your continued support, we will be making available all of our premium content *as a free service* from now on. We would like to hear from our loyal client base as to our handling of the recent intrusion by those deranged, sexually deviant criminal hacker terrorist masterminds. Please fill out the following form and return it to me My mobile: 512-xxx-xxxx My home phone: 512-xxx-xxxx
All of the messages come from an IP address in Germany. But it’s pretty clear that this is a targeted
- attack (or rather, an opportunistic one). The spammers didn’t even have to do anything, just scrape together the list of email addresses and craft together a credible looking (ahem) spam campaign.
That’s the latest. I must say, this whole thing kind of ticks me off.