A little more on Microsoft’s Waledac shutdown
Yesterday, I posted that Microsoft had recently obtained a court order to shut down several *.com’s that were known to host command-and-control centers for the waledac botnet. Working together with some folks at Shadowserver, the University of Washington and Symantec, it represented one of the first times that a group of people from private industry, higher education and the legal arena collaborated to take down a botnet. Microsoft Associate Counsel Tim Cranton blogged recently:
At Microsoft, we don’t accept the idea that botnets are a fact of life. We are a founding member of the Botnet Task Force, a public-private partnership to join industry and government in the fight against bots. Given the recent spread of botnets, we are getting even more creative and aggressive in the fight against botnets and all forms of cybercrime. That’s why I’m proud to announce that through legal action and technical cooperation with industry partners, we have executed a major botnet takedown of Waledac, a large and well-known “spambot.”
…
Three days into the effort, Operation b49 has effectively shut down connections to the vast majority of Waledac-infected computers, and our goal is to make that disruption permanent. But the operation hasn’t cleaned the infected computers and is not a silver bullet for undoing all the damage we believe Waledac has caused. Although the zombies are now largely out of the bot-herders’ control, they are still infected with the original malware.
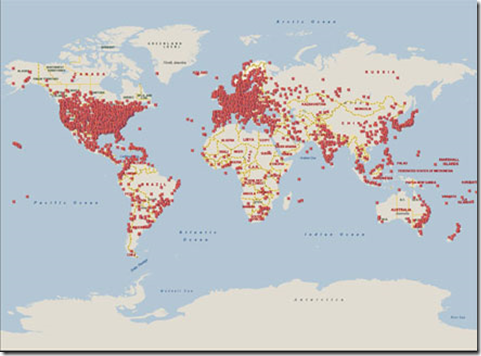
A map of Waledac infections around the world in a recent 24 hour period
Microsoft does acknowledge, as seen from the quote above by Cranton. The malware is still infecting the affected computers, only the communication channels have been disrupted. Still, it is a significant, if temporary blow to another botnet. This follows a pattern that seems to be emerging over the past 1 1/2 years:
- McColo was knocked offline in late 2008
- Pricewert LLC was taken offline in June 2009
- A Latvian ISP was taken offline in August 2009
- Fireeye took down the Mega-D botnet in November 2009
- Neustar took the Lethic botnet offline in January 2010
All of these had temporary impacts on each of these botnets and spam activity, but in each case the botnets rebuilt their infrastructure and returned. So yes, perhaps we can be a little jaded about this but we can gain short-lived victories. Here’s The Register’s take:
Criminals running botnets have faced a number of takedown operations over the last year or so, dating back to the McColo shutdown. All normally result in a temporary slowdown in spam volumes. But cybercrooks are getting better at building more resilient networks. Even if that doesn't work, there are always more miscreants in the shadows ready to step in and sell bulk mail services to unethical, unscrupulous or outright criminal marketeers.
Microsoft's enforcement action is welcome, but it treats only the symptoms - and not the root cause - of the botnet epidemic. [TZ - emphasis mine]
We all acknowledge that Microsoft’s actions do not address the root cause of the botnet epidemic. It is only one part of the solution, but it does follow a pattern of shutting down the bot’s command-and-control center. Sometimes you don’t have to completely win the battle, you only have to make it too expensive for the bot controller and spammer to shift the cost/benefit ratio into an unfavorable direction. In other words, disruption of their model is a viable tactic (in my opinion).
And as I said in my previous post, Microsoft has got a multipronged strategy for dealing with the root cause of the botnet epidemic in addition to the action taken above:
The free distribution of the Malicious Software Removal Tool to registered and unregistered users of Windows cleans up the malware that distributes it in the first place.
The free distribution of Microsoft Security Essentials that proactively keeps your machine clean (MSRT is not real time).
In 2002, Microsoft launched its Trustworthy Computinginitiative to improve public trust in its own commercial software. In addition, the company participates in a number of industry collaborative groups such as the Antiphishing Working Group (APWG), the Messaging Anti-Abuse Working Group (MAAWG), and the National Cyber Security Alliance (NCSA).
Microsoft’s Software Development Lifecycle requires that all of its products go through the Secure Windows Initiative, a process where potential security risks are identified and mitigated. Indeed, if you read through the Microsoft Security and Intelligence Report, Microsoft’s newer OS’es are much more resilient to malware than older versions (ie, Windows XP).
Action against bad against requires a multi-faceted approach, and this latest action by Microsoft (and others) is another arrow in the quiver to use in the battle against Internet abuse.