Truth and deception - phishing
Of all the types of spam that make use of deception (ie, all of them), the most damaging of all of them are phishing messages. Phishing messages are when a spammer impersonates a legitimate entity -- a form of reputation hijacking -- in an attempt to trick the user into giving up personal information like banking information. The phisher then uses the information in order to steal money from the victim.
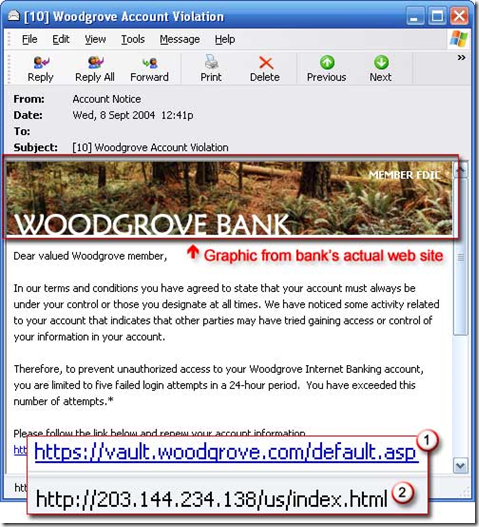
So how do you recognize a phish? Microsoft has a good description on this. Below is a screen shot of a sample message:
A good phish (and even a bad one) takes the form:
- A bank or financial institution. Phishes come from banks or online financial institutions like Paypal or eBay where money can change hands.
- Your account has been compromised or is about to expire. In the sample above, the bank claims to have noticed that your account has had some suspicious activity. This plays on your fear that maybe someone did break into your account. After all, haven't we heard stories that banks have been losing people's personal information?
- A threat. If you don't fix this problem within a certain period of time, your account will disabled and then you'll really be in trouble.
- Don't worry, click here to fix it. To remedy the problem -- that your account will expire, or to lock down your account or change your password -- follow the link in the message which will take you a web page to fix it.
- A fake link. You'll see a link in the message that appears to be from the bank (in the example, it's supposedly a secure site going to woodgrove) but if you hover your mouse over it, the link actually points somewhere else. This is simply a trick using HTML coding.
- Poor grammar. I've italicized this because it does not occur in every phishing message. However, if you get a message from a bank that contains lots of spelling mistakes and poor verb tenses (you know, the complete opposite of my blog), then you can be certain it didn't come from the purported source.
So does phishing work? Research (that I am sure I have seen somewhere) shows that these types of scams cost consumers millions of dollars each year. So yes, it does work. But why does it work?
I don't know for certain, but I have theories. Research shows that we, as people, can detect real smiles from fake smiles, but most of us choose not to because we like to think that smiles are genuine and that people really are happy in their interactions with us. I don't think that phishing has that same problem.
My guess is that if a phisher sends several thousand messages to people, perhaps 5% of them will go to people who actually have an account at that bank. Thus, for 95% of us, it's a waste of time. But to the 5% of us who it actually hits, it preys on people's fears. Fear is an innate human emotion (see Ekman, Unmasking the Face, 2003). When emotions get involved, people don't always act rationally (for an example, see the Incredible Hulk). So, by invoking the fear response of the threat of their account being shut down, people can be tricked into doing something that wouldn't otherwise do. While we can all say "Oh, I wouldn't have been fooled by that" the fact is that under other circumstances where you are put under psychological pressure, you might do something that wouldn't otherwise do.
Of course, the more people get wise to these tactics, the less they actually will work in real life. In the meantime, it's up to the anti-spam crusaders to keep this stuff out of people's inboxes.