Access Denied while trying to Start/Stop a service using Release Management Deployment Agents.
We have seen a few cases where the Releases involving starting/stopping services were failing with an access denied error. (Refer the Deployment Logs)
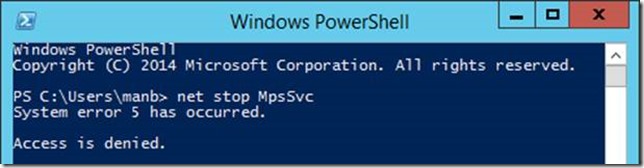
System error 5 has occurred.
Access is denied.
Environment:
RM 2013/2015
Windows Server 2012 R2
This applies to any services (Windows services as well as custom created services) that requires “Elevation” to administrative mode.
It is imperative that the account running the Deployment Agent must be a local admin to perform these administrative tasks.
Even if this is the case, we would get access denied because of the User Access Control in Windows Servers 2012 R2.
As an example, try stopping the Windows Firewall service using a local admin account using Powershell.
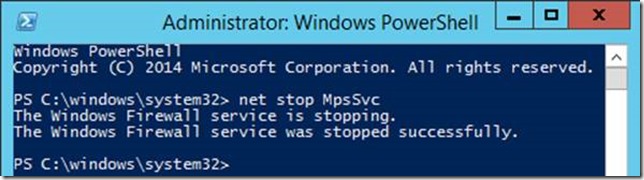
Now, let’s try the same command by opening Powershell as Administrator (right click, Run as Administrator),
This is due to the UAC restrictions.
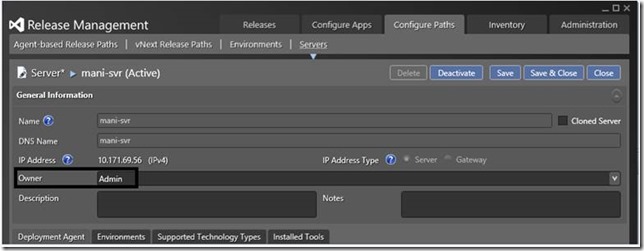
In Release Management, if the owner of the server is not initiating the release, we have seen this access denied issue,
Note: In my case, I am the Admin and Owner of the server I am trying to stop services on.
Nevertheless, to resolve this issue, either run the Deployment Agent as Local System, 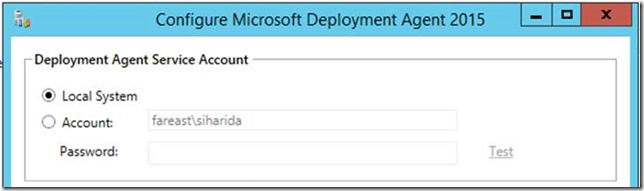 Or, use an account that’s a local admin on the server and ensure UAC is disabled.
Or, use an account that’s a local admin on the server and ensure UAC is disabled.
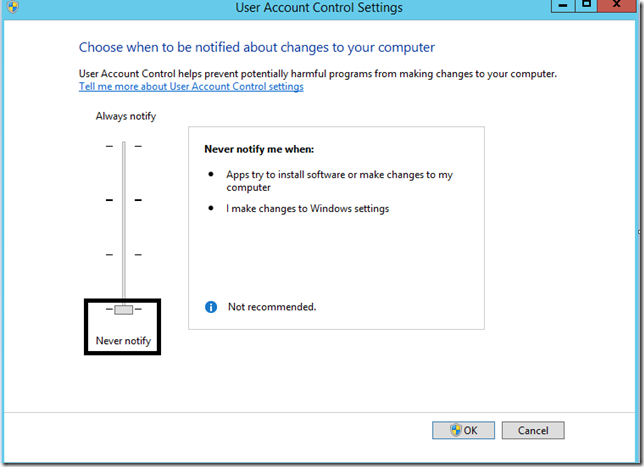
To disable UAC (User Access Control), Start by typing “Change User Account Control Settings” from the start menu,
Please note that the UAC is an added level of security to ensure that Administrative tasks are performed in administrative mode.
This will ensure the Release path is able to Start/Stop services, provided the account has admin permissions.
Content Created By : Manigandan Balachandran
Content Reviewed By : Romit Gulati