Announcing Transparent Data Encryption for Azure SQL Database
Available today, SQL Database Transparent Data Encryption (preview) protects your data and helps you meet compliance requirements by encrypting your database, associated backups, and transaction log files at rest without requiring changes to your application.
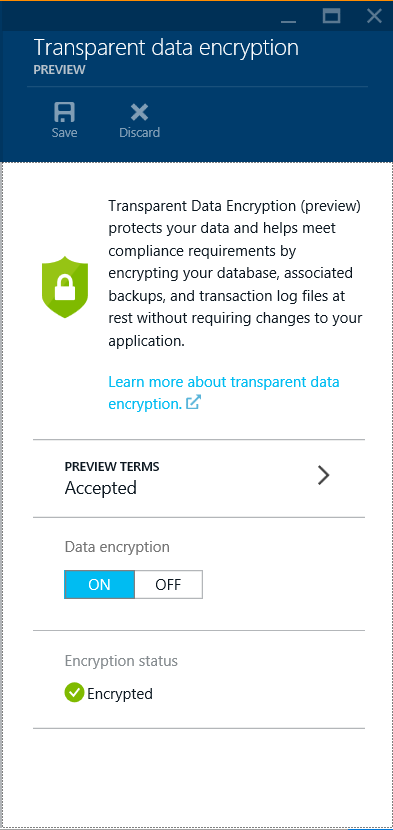
SQL Database TDE is based on SQL Server’s TDE technology which encrypts the storage of an entire database by using an industry standard AES-256 symmetric key called the database encryption key. SQL Database protects this database encryption key with a service managed certificate. All key management for database copying, Geo-Replication, and database restores anywhere in SQL Database is handled by the service – just enable it on your database with 2 clicks on the Azure Preview Portal: click ON, click Save, done.
Transparent Data Encryption for Azure SQL Database is built on top of the same Transparent Data Feature that has been running reliably on SQL Server since 2008. We have made updates to this core technology that will be available cloud first on Azure SQL Database, including support for Intel AES-NI hardware acceleration of encryption. This will reduce the CPU/DTU overhead of turning on Transparent Data Encryption.
Additionally, Transparent Data Encryption is built on top of the secret management service we use to isolate Azure SQL Database Tenants. Azure SQL Database has for years securely managed the hardware and virtual machines that Azure SQL Database runs on top of, as evidenced by the many certifications and audits we have passed - see the Microsoft Azure Trust Center for more details. We use this infrastructure to manage unique certificates per Azure SQL Database Server to protect your database encryption keys. We also use it to distribute these certificates as needed when you restore your database to a new server or setup a Geo-Replication - and update these when the certificate is rotated every 90 days for you. This enables a seamless experience where you just turn on Transparent Data Encryption and use the service without having to think about certificates or keys.
We hope this meets many of your needs for Encryption at Rest in a manner that lets you focus on the work that is important to you. For more information, see MSDN.
UPDATE: I've added a post with known issues.