Putting CAPI2 logging to good use...
So there was a problem with a printer which you could connect to via SSL in order to print via IPP.
You go in and configure the printer via a web page like so:
Create New Self-Signed Certificate
Create a new self-signed certificate. Warning: This operation will overwrite the currently installed certificate with a new self-signed certificate.
Create Certificate Request
Create the Certificate Request that you will give to a Certificate Authority. The Certificate Request will be used to generate a certificate for you.
Import Certificate and Private Key
Import a certificate and private key to use as the Jetdirect certificate. (Note: This will overwrite the current Jetdirect certificate and private key.
Export Certificate
Export the Jetdirect certificate and private key.
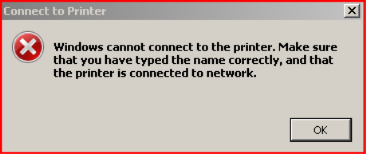
The server was configured for “Create New Self-Signed Certificate “ However, Vista would fail to connect to the server. We would connect to https://10.10.10.34 and Vista fails with an error:
"Windows cannot connect to the printer. Make sure that you have typed the name correctly, and that the printer is connected to network."
BTW - you know you can ctrl+c when those popup boxes are there and capture the info in them right?
So – why did XP work OK but Vista failed..
Let’s start with some CAPI logging… which I discussed back on march 13 , ’07 -- https://blogs.msdn.com/spatdsg/archive/2007/03/13/troubleshooting-pki-problems-on-windows-vista.aspx
The first entry to take note of is this one – spoolsv.exe is the process which is doing a trust verification check
Log Name: Microsoft-Windows-CAPI2/Operational
Source: Microsoft-Windows-CAPI2
Date: 8/6/2007 6:40:34 PM
Event ID: 80
Task Category: Verify Trust
Level: Information
Keywords: Trust Verification
User: CRISCO1\administrator
Computer: VistaCrisco.crisco.com
Description:
<UserData>
<WinVerifyTrustStart>
<EventAuxInfo ProcessName="spoolsv.exe" />
<CorrelationAuxInfo TaskId="{D0BD64A0-244A-46F0-8AA0-E80EF5952D61}" SeqNumber="1" />
</WinVerifyTrustStart>
</UserData>
Then we can clearly see that the certificate is not trusted by the Vista machine we are trying to connect with.
Log Name: Microsoft-Windows-CAPI2/Operational
Source: Microsoft-Windows-CAPI2
Date: 8/6/2007 6:40:35 PM
Event ID: 11
Task Category: Build Chain
Level: Error
Keywords: Path Discovery,Path Validation
User: CRISCO1\administrator
Computer: VistaCrisco.crisco.com
Description:
For more details for this event, please refer to the "Details" section
Event Xml:
<CertGetCertificateChain>
<Certificate fileRef="F5287D67AE6D81E7F7D6C1582BC58DBD7715C870.cer" subjectName="HP Jetdirect 0AF8ACE8" />
<ValidationTime>2007-08-07T01:40:35.389Z</ValidationTime>
<AdditionalStore>
<Certificate fileRef="F5287D67AE6D81E7F7D6C1582BC58DBD7715C870.cer" subjectName="HP Jetdirect 0AF8ACE8" />
</AdditionalStore>
<ExtendedKeyUsage orMatch="true">
<Usage oid="1.3.6.1.5.5.7.3.1" name="Server Authentication" />
<Usage oid="1.3.6.1.4.1.311.10.3.3" />
<Usage oid="2.16.840.1.113730.4.1" />
</ExtendedKeyUsage>
<Flags value="0" />
<ChainEngineInfo context="user" />
<CertificateChain chainRef="{15DE00A4-2C51-42E0-A086-C85E1B51E30A}">
<TrustStatus>
<ErrorStatus value="20" CERT_TRUST_IS_UNTRUSTED_ROOT="true" />
<InfoStatus value="100" CERT_TRUST_HAS_PREFERRED_ISSUER="true" />
</TrustStatus>
<ChainElement>
<Certificate fileRef="F5287D67AE6D81E7F7D6C1582BC58DBD7715C870.cer" subjectName="HP Jetdirect 0AF8ACE8" />
<TrustStatus>
<ErrorStatus value="20" CERT_TRUST_IS_UNTRUSTED_ROOT="true" />
<InfoStatus value="10C" CERT_TRUST_HAS_NAME_MATCH_ISSUER="true" CERT_TRUST_IS_SELF_SIGNED="true" CERT_TRUST_HAS_PREFERRED_ISSUER="true" />
</TrustStatus>
<ApplicationUsage>
<Usage oid="1.3.6.1.5.5.7.3.1" name="Server Authentication" />
<Usage oid="1.3.6.1.5.5.7.3.2" name="Client Authentication" />
</ApplicationUsage>
<IssuanceUsage any="true" />
</ChainElement>
</CertificateChain>
<EventAuxInfo ProcessName="spoolsv.exe" impersonateToken="S-1-5-21-4227054899-3893708993-4289900008-500" />
<CorrelationAuxInfo TaskId="{0FBD18B4-EFAD-4CFE-B4E8-1DE60B22ED57}" SeqNumber="11" />
<Result value="800B0109">A certificate chain processed, but terminated in a root certificate which is not trusted by the trust provider.</Result>
</CertGetCertificateChain>
There was an option to export the cert from the printer so we do that and import it into the Vista machine trusted root store.
Try again…. Ahh a new error – Ill just paste the relevant section from the CAPI2 logs.
<UserData>
<WinVerifyTrust>
<ActionID>{573E31F8-AABA-11D0-8CCB-00C04FC295EE}</ActionID>
<UIChoice value="2">WTD_UI_NONE</UIChoice>
<RevocationCheck value="0" />
<StateAction value="0">WTD_STATEACTION_IGNORE</StateAction>
<Flags value="80000000" CPD_USE_NT5_CHAIN_FLAG="true" />
<CertificateInfo displayName="10.10.10.34" />
<RegPolicySetting value="23C00" WTPF_OFFLINEOK_IND="true" WTPF_OFFLINEOK_COM="true" WTPF_OFFLINEOKNBU_IND="true" WTPF_OFFLINEOKNBU_COM="true" WTPF_IGNOREREVOCATIONONTS="true" />
<CertificateChain chainRef="{963B980F-686F-4510-B7BA-4E400027465B}" />
<EventAuxInfo ProcessName="spoolsv.exe" impersonateToken="S-1-5-21-4227054899-3893708993-4289900008-500" />
<CorrelationAuxInfo TaskId="{4A74C3A9-C2A6-4C10-A05C-5452578D2010}" SeqNumber="6" />
<Result value="800B010F">The certificate's CN name does not match the passed value.</Result>
</WinVerifyTrust>
</UserData>
</Event>
Hrmm this one is a little more difficult.
The printer automatically creates a name like:
Subject:
OU=J7961G
OU=00110AF8ACE8
O=Hewlett-Packard Co.
CN=HP Jetdirect 0AF8ACE8
And we don’t like the name? The error is : The certificate's CN name does not match the passed value.
What does that mean?
It means that the passed value https://10.10.10.34 did not match the CN….
It does a check in crypt32.dll for the “server name” ( 10.10.10.34 ) against the CN (HP Jetdirect 0AF8ACE8 ) and fails if they are not the same.
We cannot simply connect to https://HP Jetdirect 0AF8ACE8 as it is not a proper FQDN.
So now we know we can’t get around this and change these check. How to configure this then?
The easiest way to workaround it is to generate a self signed cert which does have the proper names we can connect to.
Per the printer config page we could submit a request to a CA – but if we don’t have one then the procedure outlined below is the next best option..
Get a copy of makecert.exe ( its in the free download Platform SDK )
· Run it like so in order to create a self signed cert which has an exportable key and the proper subject.
makecert.exe -r -pe -n "CN=10.10.10.34" -b 07/01/2007 -e 07/01/2010 -eku 1.3.6.1.5.5.7.3.1 -ss My printer.cer
· The switches to make this work are the:
· –pe switch ( allow the keys to be exportable )
· -r self signed
· -eku – specify Server Auth OID
· You will see a new file called printer.cer
C:\Program Files\Microsoft SDKs\Windows\v6.0\Bin>dir prin*
Volume in drive C has no label.
Volume Serial Number is 108D-3591
Directory of C:\Program Files\Microsoft SDKs\Windows\v6.0\Bin
07/31/2007 10:16 AM 542 printer.cer
1 File(s) 542 bytes
0 Dir(s) 3,574,562,816 bytes free
· Now looking in your personal store via certmgr.msc you should see a cert in there with the Issued by field as “CN = 10.10.10.34”
· Right click on this cert, and export this and include the private keys.
· Now, go to the printer management web page and import the .PFX file you just exported.
· Also take the file called printer.cer – and import it to the trusted root store on the Vista machine.
You should now be able to connect OK.
Takeaways:
CAPI2 logging is very very helpful – check it out before you jump to conclusions – it may be more helpful than you realize.
Spatdsg