SoCalDevGal looks at BitLocker for USB drives in Windows 7

I’ve wanted to play around with this feature (also called ‘BitLocker-To-Go’), but hadn’t had time until today. I’ll recap what I’ve found. First, and probably most important, is that BitLocker is only available as part of Windows 7 Ultimate (or Enterprise) editions. That is, the ability to ENCRYPT is available only in these editions of Windows 7. Of course, you can DECRYPT with any version of Windows 7. For testing I used one laptop with Windows 7 Ultimate to encrypt and another one with Windows 7 Home Basic to decrypt.
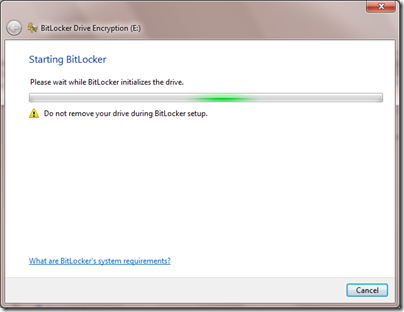
To access, or start using this feature, simply insert your USB drive and then right click on the drive. (Alternatively, you can choose to ‘turn on BitLocker’ via an applet in the Control Panel). You’ll then see the option to ‘Turn on BitLocker…’ on the context-sensitive menu. You’ll then see the dialog box shown below, as your USB drive is being prepared to be encrypted.
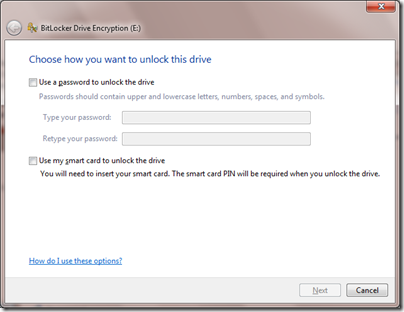
Because the machine I am using to encrypt includes a SmartCard reader, I have option to encrypt by using either a password or a SmartCard. These options are shown in the dialog box below. Note that if you use a smart card, you’ll also have to enter your smart card PIN when you want to decrypt (read) the information on the USB drive.
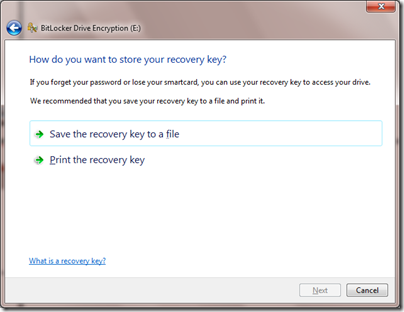
For simplicity I’ll just use a password. Note that the passwords should be complex (i.e. upper/lower, numbers, etc…) to be effective, however the only validation on the password value is a length requirement. That is, users can choose to enter overly simply passwords, for example in my case I entered the digits 1-8 only. The next screen of the wizard asks you to select where you’d like to store the recovery key. Your options are either to store the key to a file or to print the key. Appropriate key storage is, of course, vital to successful security via encryption. Also, from a practical point, if you forget the USB password, the only other way to access the data stored on an encrypted USB drive is by entering the recovery key information.
Note: There is also a local (security) policy setting (Control Panel>Administrative Tools>Local Security Policy>Security Settings>Public Key Policies>BitLocker Drive Encryption) which allows you to define Data Recovery Agents. GPO discussion is beyond the scope of this blog post. For more info – go here.
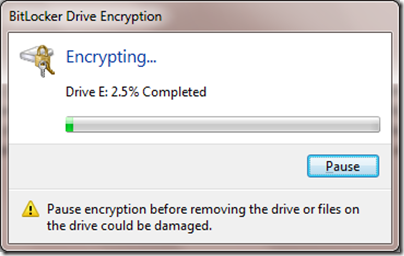
I’ll select ‘Save the recovery key to a file’ for our test. After selecting the folder location for the file save, you will be presented with final dialog box which will ask you to confirm the encryption by clicking on the ‘start encrypting’ button. After you do that, you will see a dialog with an encryption progress bar on it. The process of encrypting will take a couple of minutes, during this time you have the option to ‘pause’ encryption if desired by clicking on that button on the dialog box as shown below.
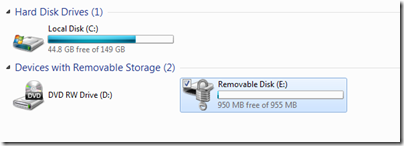
When complete, a dialog will confirm the encryption. You can also easily see that a USB drive has been encrypted by viewing it in Explorer. In this case, my USB is E:\
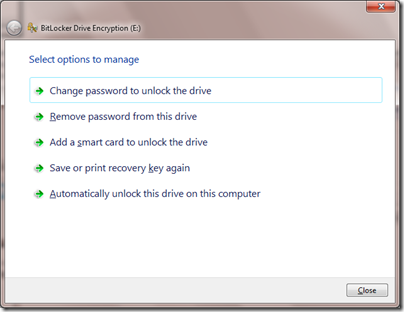
If you wish to change BitLocker settings, you can simply right click on the encrypted drive in Explorer and then click on the ‘Manage BitLocker…’ menu option.
The options you can change are shown in the screenshot below. They include changing the password, removing the password (if you do this, you must add a smartcard, as the drive is STILL encrypted), adding a smart card, saving/printing recovery key, or auto unlocking this drive on this (the encrypting) computer. You’ll note that there is NO option to remove BitLocker encryption from the USB drive. The only way to do this is to FORMAT the USB, which, of course, also removes any data on that device.
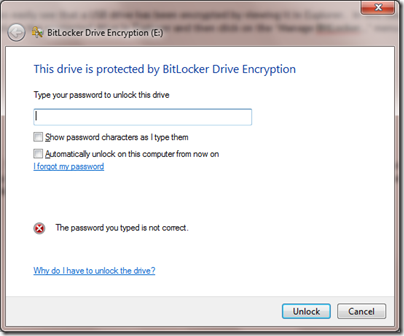
The experience for using an encrypted USB drive is very simple. A dialog box, similar to the one shown below pops up shortly after a USB drive is inserted into the USB slot. Note that if you are using the encrypted USB drive on the encrypting computer, then you can select the option to ‘automatically unlock on this computer from now on’.
Of course BitLocker is certainly NOT just for USB drives. There is wealth of information about BitLocker as an enterprise data protection tool (enforced via Group Policies on end user’s local hard drives, etc… on TechNet), I just felt like writing this post for those of us ‘home geeks’ who are using Windows 7 Ultimate at home, and are playing around with all of the advanced features because, well, we want to.