Sidebar Security
Brian Teutsch, Windows Sidebar Program Manager
The Windows Sidebar is a new Windows Vista component that provides a runtime for "gadgets." Gadgets are mini-applications designed to present the user with information or utilities. The Windows Vista Sidebar treats gadgets very similar to the way Windows Vista treats all executable code. The Sidebar team is completely committed to making Vista the most secure version of Windows ever, and that includes the security and trustworthiness of gadgets.
Sidebar Gadget development
In the version of the Sidebar included with Windows Vista, gadgets are developed using the capabilities of the Microsoft HTML engine, including HTML markup, script, images and many other capabilities. The Sidebar also provides a rich set of APIs available to the HTML script code as well as the ability to interact with previously installed ActiveX objects.
Gadget download
Gadgets are written using HTML and script, but this HTML is not located on an arbitrary remote server as web pages are. HTML content in the Sidebar is downloaded first as part of a package of resources and configuration files and then executed from the local computer. This download process is similar to applications (.exe files) downloaded from the Internet.
The files can be packaged using ZIP compression or as a Windows Cabinet File (CAB file). If the file is packaged as a CAB file it is possible to use a code signing certificate to provide information about the origin of the gadget. The user is presented with information about the gadget package before the gadget files are extracted. Signing a gadget can be accomplished with the application “signtool.exe” included with Visual Studio 2005.
Only after the user has viewed information about the gadget are the files extracted from the gadget package and loaded into the MSHTML control to render the content and run scripts.
Note: The following images are from pre-release software and may be subject to future changes.
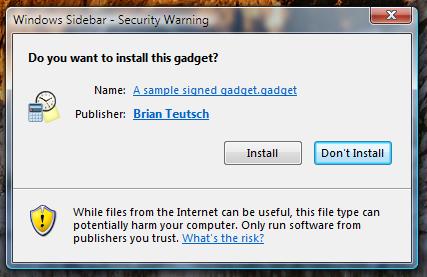
Figure 1 - Installation dialog with code signing information
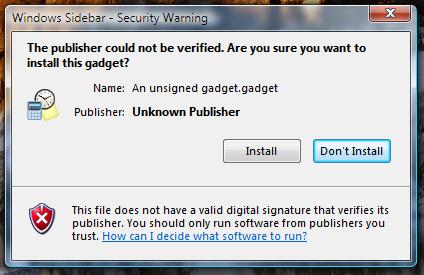
Figure 2 Gadget installation warning for an unsigned gadget.
Because code signing certificates are costly and not common among casual developers likely to create HTML gadgets, we have chosen not to place any requirements that gadgets must be digitally signed.
HTML runtime
HTML gadgets lead themselves to many comparisons with the security models found in Internet Explorer and associated with domain sandboxing security models. However, HTML gadgets have more in common with HTML Applications (HTA) than they do with HTML content in Internet Explorer. Because gadgets have a similar download and installation experience as other executable code, it is appropriate to provide them with a similar set of capabilities when run. The MSHTML runtime is configured similarly to the set of permissions given to HTML Applications or the Local Machine Zone security configuration.
For instance, gadgets are configured in several ways that web pages are not. Because gadgets are treated as executable code, they are allowed to create any installed ActiveX objects because the option “Initialized and script ActiveX controls not marked safe for scripting” is configured as such. Another option configured differently than web pages is “Access data sources across domains,” because gadgets can be more useful when they aggregate data from various locations. A final option specific to Sidebar gadgets is that the HTML pages are not allowed to download and install new ActiveX controls because the options to download signed and unsigned ActiveX controls are both disabled.
User Account Control interaction
User Account Control (UAC) is a new feature of Windows Vista that makes it easier to use Windows as a standard user. If the user is running as a standard user, the Sidebar Gadgets will run with standard user privileges as well and will be restricted from making dangerous system changes to the user’s PC. In the Administrator Approval Mode of UAC, even if the user is a member of the administrators group, by default Sidebar Gadgets will run with standard user privileges. This helps prevent code running in the Sidebar from modifying protected resources.
As an additional precaution, gadgets for the Sidebar Gadgets will not display the UAC elevation prompts that are used to allow programs to run with full administrator privileges. If a Sidebar gadget launches an application installed on the computer, however, that application may display UAC elevation prompts.
For example, if a gadget attempted to delete a file in the System32 directory, the delete operation would not succeed and no elevation prompt would be shown to the user. This failure happens because most critical files cannot be modified by standard users and the Sidebar does not display an elevation prompt.
Parental Controls interaction
Windows Vista includes a new feature named parental controls to help enforce various safe browsing and execution policies on a computer. For example, a parent in the home may only allow a child to run games that are rated G only and browse to only three specified Web sites. The policy for Web browsing also applies to Gadgets in the sidebar. For example, if the parental control policy only allows a child to browser to Web sites “A” and ”B,” and a gadget attempts to communicate with site ”C,” it will fail.
Windows Defender interaction
The download of gadgets is made more secure by the presence of Windows Defender in Windows Vista. When enabled, Windows Defender checks downloads initiated from within Internet Explorer. Thus, for example, Windows Defender will scan gadget packages that are being downloaded to examine for malicious code that may be present in the download. This scan protects users by taking place before a gadget is run or even installed.
Internet Explorer Protected Mode
Internet Explorer 7 in Windows Vista has a new security feature called Protected Mode. Protected Mode is an enhancement designed to protect users from malicious software running in the context of an untrusted remote web page while browsing the internet. Protected Mode is not applicable to gadgets as they are code present on the local computer and interact with files and APIs on the local computer.
Full trust only
Gadgets are mini-applications. Although an individual gadget may only have a single need – such as reading files and information from the computer, accessing information from one or more domains, or only displaying buttons and information for a utility – the full set of gadgets mix and match needs in a huge variety of ways. In aggregate, gadgets have the same set of needs as other code.
The choice to run a gadget is presented to the user in the same way that the choice to run any application downloaded from the internet is presented to the user. Information about the author is presented in a dialog that indicates there is risk associated with this file. After the first user acceptance, the gadget can be run without further prompting by using the Windows Sidebar’s “Add Gadget” dialog.
Additional security for corporations
If your users are in an environment controlled by group policy, it is possible to limit the use of gadgets beyond what is described above. The Sidebar supports a shared gadgets directory under Program Files that can only be modified by the administrator group on that computer. Gadgets can be placed in that directory for all users on the machine to use. Further, there is a policy option to disable the ability for users to install new gadgets into their user directories. This policy option also prevents the use of any gadget that is not present in the Shared Gadgets folder – which can only be modified by an administrator.
The Windows Sidebar has the following group policy options available:
- Turn off Windows Sidebar
This policy allows administrators to completely disable the Windows Sidebar. The user will not be able to start the Windows Sidebar if this policy is enabled. - Disable unpacking and installation of gadgets that are not digitally signed.
This policy allows an administrator to require that all gadgets installed by a user are digitally signed. This policy only affects gadgets that are downloaded and then run, such as double-clicking on a gadget package. All previously or manually installed gadgets will still function. - Turn Off User Installed Windows Sidebar Gadgets
This policy provides administrators with the ability to block all gadgets not placed into the Shared Gadgets or Gadgets folders (in the Sidebar’s Program Files folder), both of which can only be modified by a user in the administrator group. Gadgets in the user’s directory will not display in the Gadget Gallery dialog or otherwise be allowed to run. - Override the More Gadgets Link
The Gadget Gallery dialog provides a link where users can discover more gadgets. By default this link points to an online Microsoft website, however administrators can specify that this link open another website. Administrators can then more easily distribute gadgets that are approved for use within their organization.
These policies are described in more detail in other documentation regarding Windows and group policy options.