Warning: the following contains explicit SSL
(or, Messaging: Port Probing Demystified)
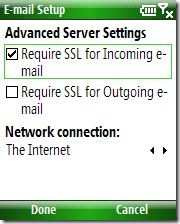
The "Require SSL" checkbox in the account configuration wizard for POP3/IMAP accounts is an often misunderstood feature. It's somewhat ironic, then, that the intent of the checkbox is actually to simplify account configuration.
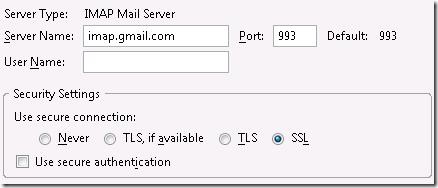
Compare the following two screenshots taken from WM6 Standard and Mozilla Thunderbird.
Notice how much more complexity there is in the Thunderbird dialog. Now this is not intended to be a dig at Thunderbird. In fact, as a power user I prefer and appreciate this level of control. But I realize that my preference doesn't reflect the best user experience for someone who doesn't write email software for a living!
Pop quiz, hotshots:
- List the standard and secure ports for POP3, IMAP, and SMTP.
- What is the difference between TLS and SSL? How do you know which your server supports?
- What is the difference between "Use secure connection" and "Use secure authentication"?
To expect that the average user would be able to answer any of these questions is ridiculous. If they are able to provide the server address and username, that is already a huge win in my book.
So in the name of usability, we distilled all this down to a single, easy-to-ignore checkbox. Users who don't care about security don't need to worry. More informed/vigilant/paranoid users can enable the secure setting.
Probing the issue
Despite all the settings available in Thunderbird, there are really only three common connection profiles:
- Implicit SSL on the secure port (a.k.a. IMAPS/POP3S/SMTPS)
- Explicit SSL on the standard port (a.k.a. STARTTLS/STLS)
- Unencrypted on the standard port
Rather than ask the user to know or guess which profile matches their particular server configuration, we simply try them all until we find one that works. We call this port probing.
Let's run through an example port probing scenario where SSL is not supported:
- User configures an IMAP4 account and initiates a Send/Receive
- Probe attempt 1
- Implicit SSL on IMAPS port 993
- Connection time out
- Probe attempt 2
- Explicit SSL on IMAP port 143
- Connection successful
- Ask server if STARTTLS is supported
- Server says "no"
- Probe attempt 3
- Unencrypted on IMAP port 143
- Connection successful (just use the connection from the previous attempt)
- Ask server if plaintext authentication is supported
- Server says "yes"
- Login!
Now that we know which connection method the server supports, we can continue to use that method during subsequent Send/Receive sessions.
One important aspect of this routine is that the more secure connection profiles are tried first. In the above example, plaintext login was tried only as a last resort.
Questions arise
Q. Isn't port probing slow?
A. Yes, it can be slow since in many cases we are sitting around waiting for the socket connect attempt to time out. But typically the probing is only done during the first Send/Receive so it is a one time cost.
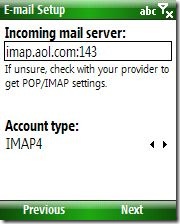
Q. What if my server doesn't listen on the standard ports?
A. Specify the port number in the hostname (e.g. "imap.aol.com:143 " ). This works for both incoming and outgoing mail server.
Protip: Specifying the port number in this manner will influence the port probing logic to favor the specified port number and will generally speed up the connection process!
Q. I'm using WM5 and [scenario] won't work!
A. Unfortunately there were a number of bugs in the port probing implementation in WM5 (see Errata below)
Q. Wait, you never explained what the "Require SSL" checkbox does
A. If the checkbox is checked, the port probing will never try plaintext login over an unencrypted channel.
Errata
The port probing implementation in WM5 was not perfect, though I'd venture to guess that most users never encountered these bugs. That said, woe unto he whose email administrator did use nonstandard ports or did regard STARTTLS above all others.
If you are having email connectivity issues and you suspect port probing may be to blame, try these troubleshooting techniques:
- Add or remove the port number from the hostname
- Toggle the "Require SSL" checkbox on or off
- Toggle the "Outgoing connection requires authentication" checkbox on or off
- (Try different permutations of the above settings)
If you have control over your own mail server, some connectivity issues can be resolved by opening alternative encryption/authentication methods. For example if your server only uses explicit SSL, try enabling implicit SSL on a different port.