Add an assembly to the Global Assembly Cache on Windows Server 2008 R2
While doing an install of SharePoint Server 2007 on Windows Server 2008 R2, my customer and I bumped into a problem: we couldn’t manually add some assemblies to the Global Assembly Cache (GAC). Obviously, UAC (User Account Control) was blocking us… but all of the standard tricks for jumping through UAC were failing. We tried:
- Start a cmd prompt with “Run as administrator” and then typing “explorer” (which in theory launches explorer as the UAC’d admin) to launch two windows. FAIL. My guess is that the Explorer process doesn’t receive the credentials of the UAC’d administrator when it launches.
- run GACUTIL through a UAC’d command prompt… FAIL.(GACUTIL isn’t officially supported for production installs anyway).
- “Disable” UAC. FAIL. Funny thing about 2008 R2… you never ACTUALLY disable UAC. You can tell it not to prompt you… but it will still roadblock you if something absolutely requires local administrator rights to accomplish.
Then chat with a colleague brought up an idea…is there some policy getting in the way?
I doubted that there was any specific group policy being pushed around UAC… that’s somewhat atypical. But what about a local policy?
There’s an entire list of local policies related to UAC…
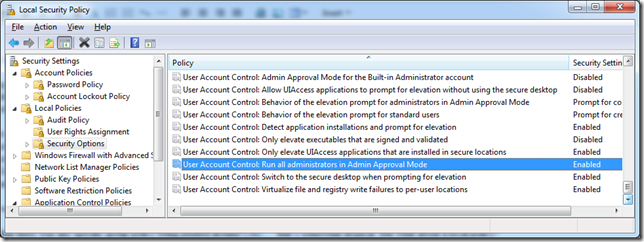
After doing some looking around, I resolved to focus on the policy highlighted above: User Account Control: run all administrators in Admin Approval Mode. It was Enabled on their server.
First, About “Admin Approval Mode”. Taken literally, Admin Approval Mode means that any action that should only be achievable by an administrator must go through UAC’s “Admin Approval” (the secure screen that presents the approval). By default (as listed above), actions that require Administrator rights must go through the “Admin Approval Mode” process… even if the person doing the action is part of the Administrators group. Setting this to “Disabled” effectively means that Admin Approval Mode is no longer required for members of the local Administrators group… effectively disabling UAC entirely for those users.
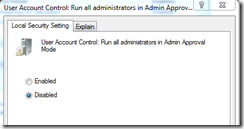
So, we disabled it and rebooted (required for changes to the local security policy).
Our drag-and-drop to add assemblies to the GAC now works. Happiness ensued.
IMPORTANT: Disabling this can make it easier for malware to compromise your system. I encourage this to be disabled only temporarily so that the specific actions required may be taken, then re-enabled (along with the associated reboot) immediately at completion.
If you cannot change this policy, you may need to chat with your Active Directory Group Policy administrators, as it is possible to force this and/or override the local security policy with domain group policies.