Disabling TLS 1.0 in Azure Web App using Application Gateway - PowerShell Automation
PLEASE NOTE: There are new features available for switching off TLS 1.0. I recommend using those instead. Azure Web Apps are a great way to deploy modern web applications in a Platform as a Service (PaaS) environment. One of the main advantages is that you do not need to manage your own server. There are, however, some situations where you need more control over the environment than a Web App will allow. As an example, it has been recommended by NIST that TLS 1.0 be disabled. Currently, it is not possible for users to disable this protocol on Azure Web Apps, which may prevent an application from meeting security guidelines.
It is possible to put an Azure Application Gateway in front of your application and you can use that gateway to control the SSL policy. More specifics on combining Azure Application Gateway and Azure Web Apps can also be found here
The process of modifying an existing Web App deployment to include an Application Gateway involves quite a few steps. It is not really feasible to implement the transformation using the Azure portal alone, so I have written a PowerShell function performs all the steps required to put the Gateway in place and apply appropriate settings. All the routines discussed here can be found in this GitHub repository.
The Problem
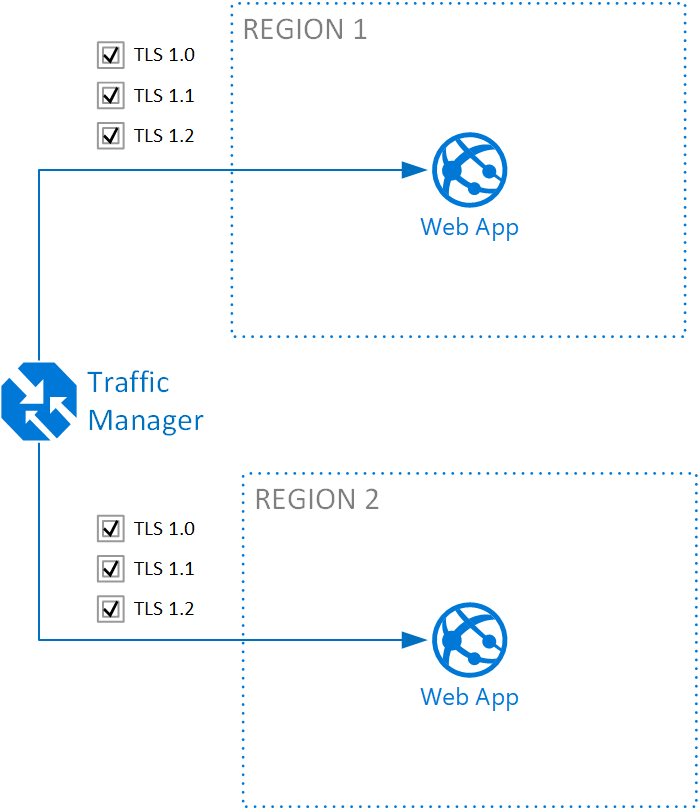
The starting point of the transformation is a commonly deployed architecture of a web application deployed in multiple regions with a Traffic Manager deployed to do DNS based load balancing. This topology is seen below:
The code repository contains a script that will establish this basic topology for testing purposes. This script can be executed with something like:
[ps]
.\SetUpTlsTestEnvironment.ps1 -ResourceGroupName <GRP NAME> -Fqdn <DOMAIN NAME> `
-CertificatePath <PATH TO CERT> -Locations usgovvirginia,usgovtexas `
-Environment AzureUsGovernment
[/ps]
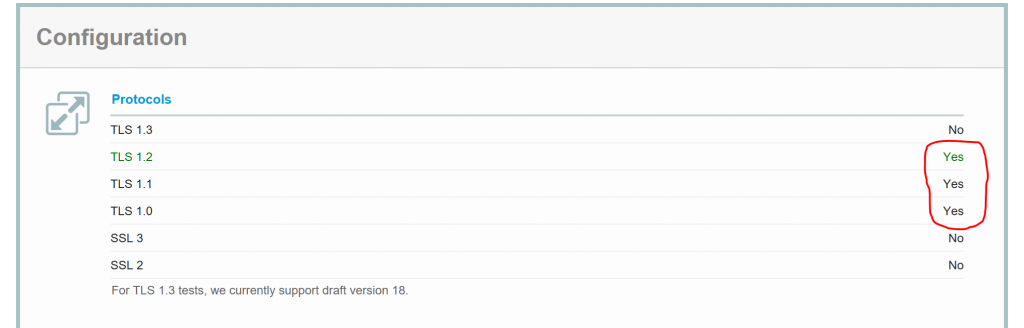
In the process of running this, you will be asked to make a CNAME entry for your domain name. Make sure it is working before proceeding, otherwise custom domain name and cert will not be deployed. After deploying the test environment, the SSL settings can be tested with the SSL test tool from SSL Labs: https://www.ssllabs.com/ssltest/. You should get a result indicating that TLS 1.0 is enabled:
The Fix
The repository contains another script, which will perform the task of putting Application Gateways in front of all web apps and setting the SSL policy accordingly. The script can be called like this:
[ps]
.\DeployAppGatewayTlsFix.ps1 -ResourceGroupName <RESOURCE GROUP> -TrafficManagerProfileName <TM NAME> `
-CertificatePath <PATH TO PFX> -Environment AzureUsGovernment
[/ps]
The script uses the Traffic Manager profile in a specific resource group as a starting point and then looks for all Traffic Manager endpoints that are Web Apps and puts a Gateway in front of each one. Specifically for every Web App:
- Create a Virtual Network to host the Application Gateway.
- Create a public IP address for the gateway.
- Creates a backend pool containing the Web App.
- Creates health probes to monitor the web app.
- Creates listener for HTTPS
- Creates a redirect listener for HTTP to HTTPS
- Adds the SSL cert to the gateway.
- Sets the SSL policy (this is where TLS 1.0 gets turned off).
- Creates the Gateway.
- Updates the Traffic Manager endpoint to hit the Application Gateway
- Sets IP Security Restrictions on the Web App to only allow connections from the gateway.
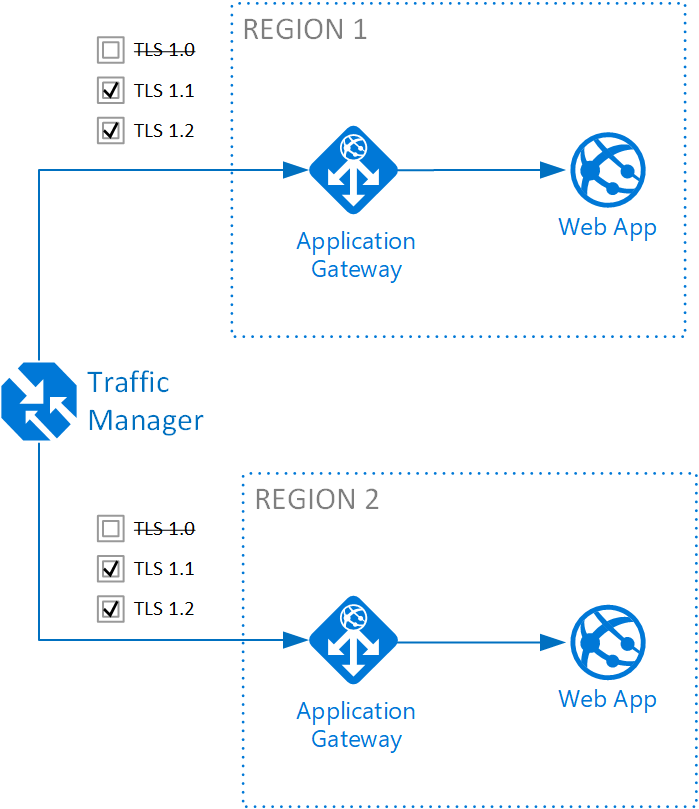
This performs the transition "in-flight" while the site remains operational. The end state looks something like the topology below:
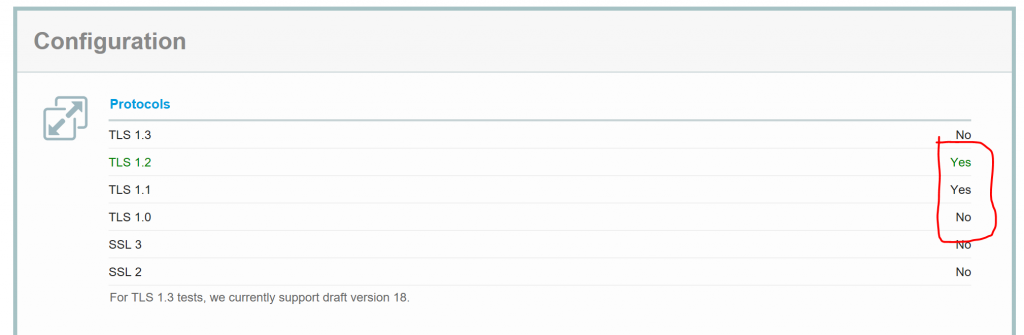
A quick test using SSL Labs should indicate that TLS 1.0 is now disabled:
Conclusions
The TLS fix script illustrates the steps involved in protecting an Azure Web App with an Application Gateway in order to disable TLS 1.0. It performs the transformation on any Web App registered as an endpoint on the Traffic Manager. The scripts are intended as a demonstration of the needed steps and you should be careful if you use the examples or parts of them on a production system. You will almost certainly need to make changes to make it work for your specific scenario. Also keep in mind that there are costs associated with deploying Application Gateways.