Unable to connect to multinic Linux VM
When creating an Azure VM with multiple NICs and subnets, the guest's default gateway is not automatically set. This may cause loss of SSH connectivity as the default gateway is not assigned to the NIC that is listening for incoming traffic.
Troubleshooting
To access the VM, create a second VM in the same cloud service. Connect to the second VM, and from the second VM, connect to the internal IP address of the problem VM. Once connected to the problem VM you can view the dmesg, kern.log, messages or boot.log file to verify the default gateway configuration.
Ubuntu
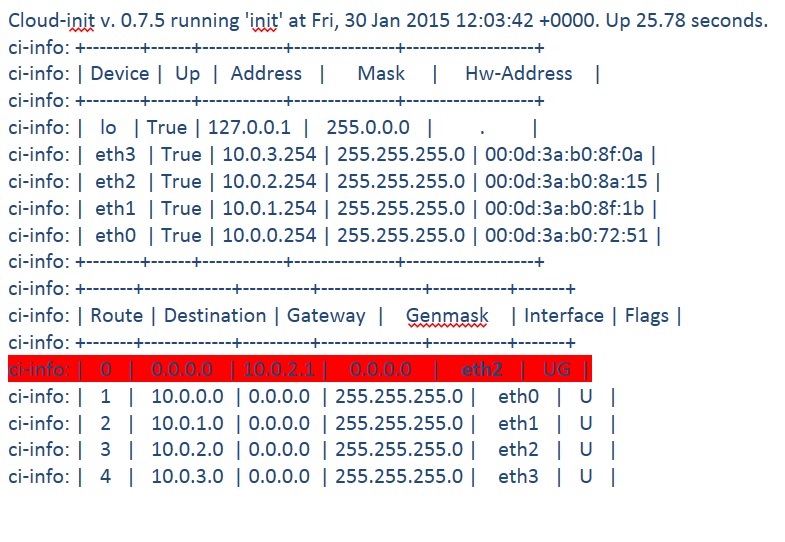
The example below shows an Ubuntu VM with four NICs. The default gateway is denoted by UG and is assigned to eth2 and not eth0.
Restarting the VM may only temporarily resolve this issue if the default gateways gets assigned to the correct interface.
To resolve the issue on Ubuntu 14.x, create a script on the VM to configure the default gateway correctly. The script will be executed at next restart and assign the default gateway to the correct network. In this example, eth0 is used as the default gateway which maps to the network 10.0.0.1.
vi /etc/network/if-up.d/defaultgw
#!/bin/sh
route delete default gw 10.0.1.1
route delete default gw 10.0.2.1
route delete default gw 10.0.3.1
route add default gw 10.0.0.1
To set the correct privileges on the file, run the following command:
chmod 755 /etc/network/if-up.d/defaultgw
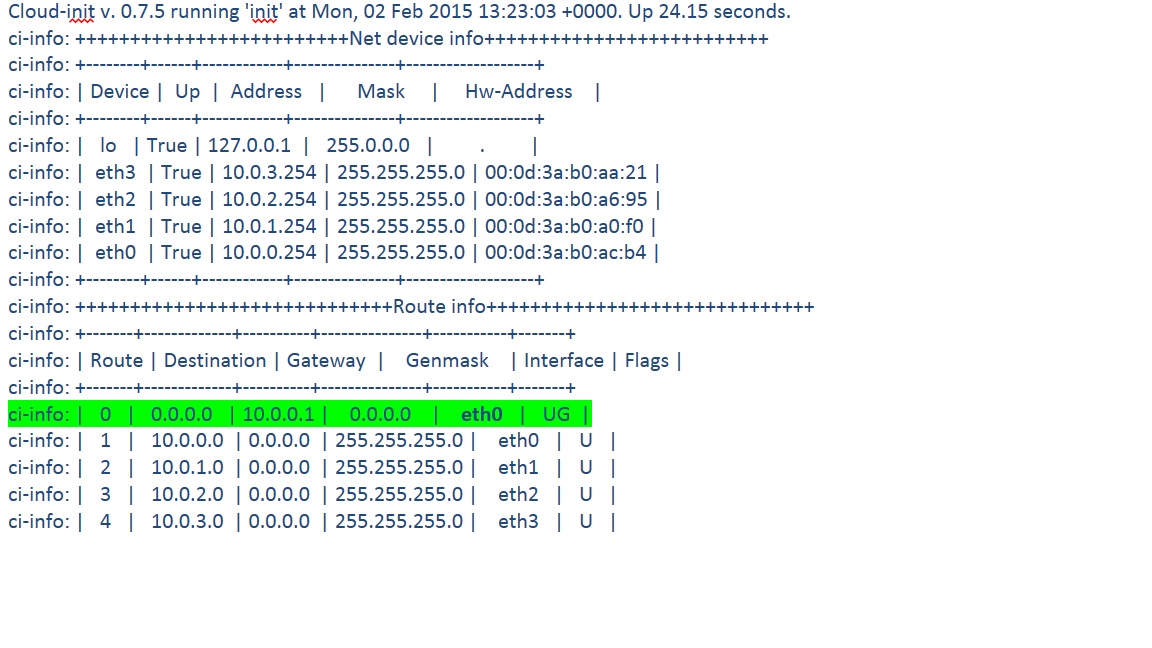
After restarting the VM the default gateway is assigned to the correct interface and SSH connections should succeed when connecting through the external (VIP) endpoint.
You can verify the default gateway configuration with netstat -rn or route -n.
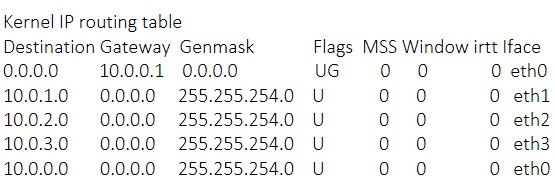
CentOS 6.5
On a CentOS 6.5 VM, append the directive of GATEWAY in the /etc/sysconfig/network file.
For example:
HOSTNAME=myvmnameNETWORKING=yesGATEWAY=10.0.0.1
See the following articles for more information on the multinic feature:
Multiple VM NICs and Network Virtual Appliances in Azure
https://azure.microsoft.com/blog/2014/10/30/multiple-vm-nics-and-network-virtual-appliances-in-azure/
Create a VM with Multiple NICs
https://msdn.microsoft.com/en-us/library/azure/dn848315.aspx
For additional resources for Linux on Azure topics please read here