Setting up a Passive FTP Server in Windows Azure VM
This post is authored by Lalitesh Kumar, Pradeep M G and reviewed by Avinash Venkat Reddy. Also special thanks to Adam Conkle and Craig Landis for providing the "points to consider from Azure SLB perspective".
FTP may run in active or passive mode. Passive mode is extensively used to solve the issue of the client firewall blocking the FTP server data connection. Detailed information on FTP server modes here.
Setting up a Passive FTP server in Windows Azure VM involves the following steps:
- Deploying a Windows Azure VM
- Installing FTP service on Windows Azure VM
- Adding the FTP site to IIS Manager on Windows Azure VM
- Specify the data channel port for passive FTP connection on Windows Azure VM
- Adding ports specified in the previous step as endpoint to the VM
- Adding Firewall rules to allow traffic on the added endpoint
- Verifying that FTP server is using the port previously specified under data channel port
- Points to consider from Azure SLB perspective
Deploying a Windows Azure VM
- Log in to the Windows Azure management portal.
- Create a Windows Azure VM with Windows Server 2012 or Windows Server 2008 image.
- Fill in the appropriate details under the Create a Virtual Machine dialog tabs.
- Once the VM is provisioned, RDP into the VM.
Note: If you are new to using Windows Azure then here are the detailed steps to provision a Windows Server VM and RDP to it.
Installing FTP service on a Windows Azure VM
- Open Server Manger and click Add roles and features.
2. From Installation Type tab select Role based or feature-based installation and click Next.
3. From Server Selection tab select the server on which you want to enable FTP and click Next.
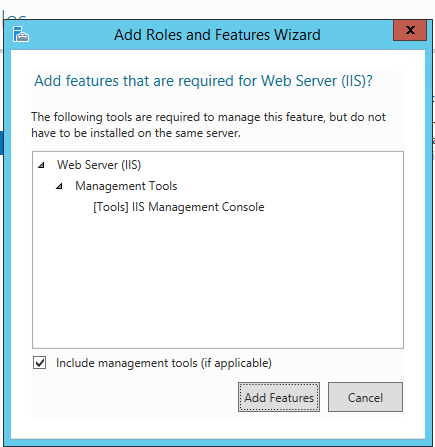
4. From Server Roles tabselect Web Server (IIS), you will be presented with the Add Roles and Features Wizard. Click Web Server (IIS) andthen click Add Features.
5. Click Next on the Features and Web Server Role (IIS) tabs.
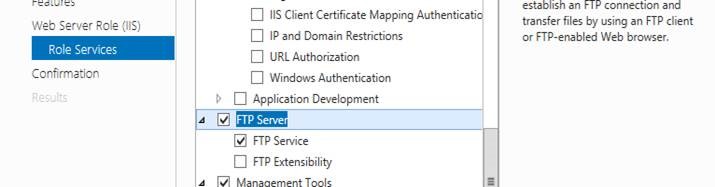
6. From Role Services tab select FTP Server and FTP Service and click Next.
7. From Confirmation tab click Install and wait for the installation to complete.
Adding the FTP site to IIS Manager
- From the Control Panel> Administrative Tools open the IIS Manager.
- From IIS Manager, in the Connections pane, expand the Sites node in the tree, then right click the Default Web Site.
- Now click Add FTP Publishing.
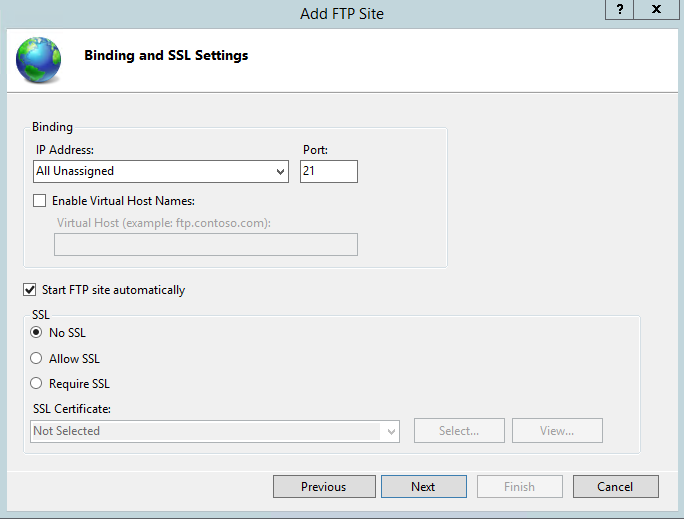
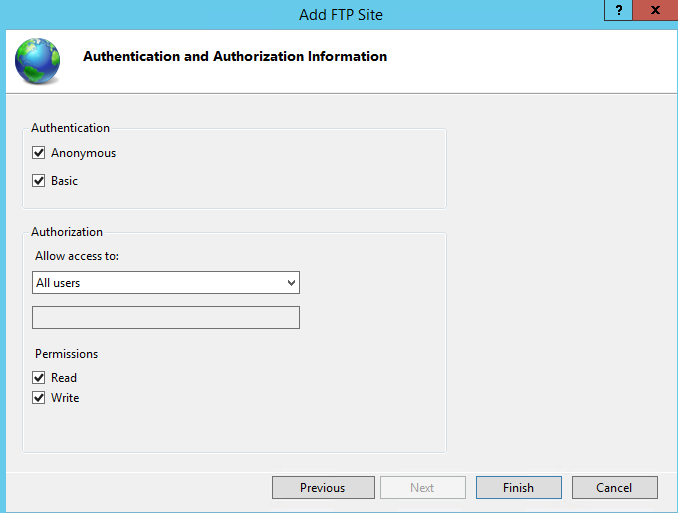
- Fill the Add FTP Site dialog box as shown in the below figures and click Finish.
Specify the data channel port for passive FTP connection on Windows Azure VM
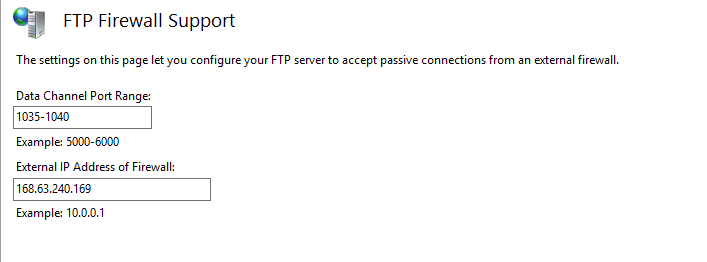
- From the Control Panel open the IIS Manager.
- In IIS Manager, in the Connections pane, click local host.
- In the Home pane, double-click the FTP Firewall Support feature.
- In the Data Channel Port Range box specify a Port Range. In this case we have used 1035-1040. The External IP Address of Firewall is the VIP of your VM.
5. Click Apply. You will be prompted to configure the firewall to allow FTP access.
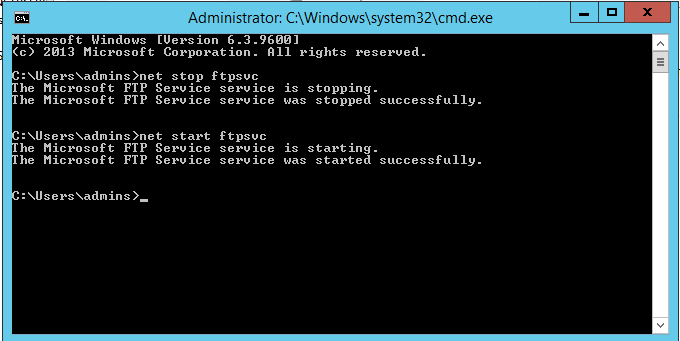
6. To make sure that FTP server has taken all the setting we added, let's stop and start the FTP service.
Note: iisreset does not restart the FTP service as it is outside the IIS.
Adding ports specified in the previous step as endpoint to the VM
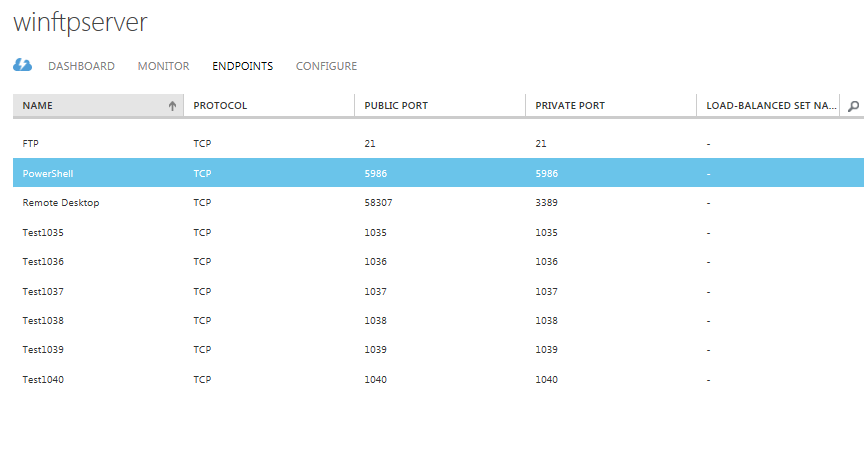
Ports 1035 to 1040 should also be added as endpoint to the Azure VM. You can add multiple ports as endpoint to the VM using Windows Azure PowerShell. Detailed procedure here.
You can also add endpoints using the management portal. Detailed procedure here.
To confirm that the said ports are added to the VM, please check the endpoint list on portal for the said VM.
Note: You also would need add port 21 to the endpoint list which is command port for FTP connection.
Adding Firewall rules to allow traffic on the added endpoint
For ports added as endpoints in the above procedure, no configuration is done automatically to the firewall in the guest operating system. When you create an endpoint, you'll need to configure the appropriate ports in the firewall to allow the traffic you intend to route through the endpoint.
In this case I have disabled the Windows firewall for simplicity. You can refer here to modify the firewall rules to allow traffic on the ports added as end points.
We are now done setting up the passive FTP Server on a Windows Azure VM.
Verifying that FTP server is using the port previously specified under data channel port
Client connects on the command port, which is usually TCP port 21.
When the connection on command port is successful, the server sends a port to the client to connect to.
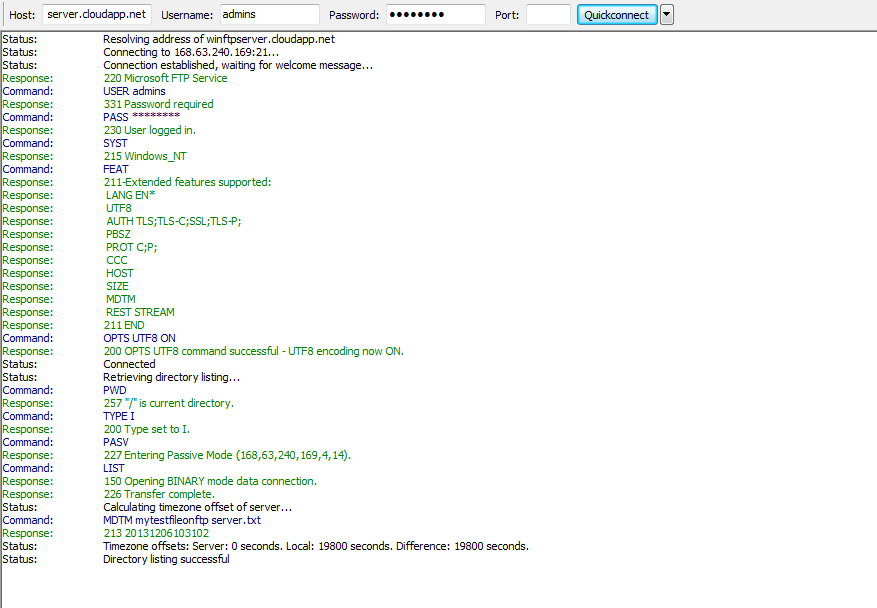
If you are using FileZilla, you will see something like this :
Command: PASV
Response: 227 Entering Passive Mode (168,63,240,169,4,14).Where 168,63,240,169 is the IP address of the VM and 4,14 is the port on which the data traffic is routed (256*4+14=1038).
This is how you determine that a port added in previous steps are actually being used to establish a passive FTP connection.
Points to consider from Azure SLB perspective
When FTP is transferring large files, the elapsed time for transfer may exceed 4 minutes, especially if the VM size is A0. Any time the file transfer exceeds 4 minutes, the Azure SLB will time out the idle TCP/21 connection, which causes issues with cleanly finishing up the FTP transfer once all the data has been transferred.
Basically, FTP uses TCP/21 to set everything up and begin the transfer of data. The transfer of data happens on another port. The TCP/21 connection goes idle for the duration of the transfer on the other port. When the transfer is complete, FTP tries to send data on the TCP/21 connection to finish up the transfer, but the SLB sends a TCP reset instead.
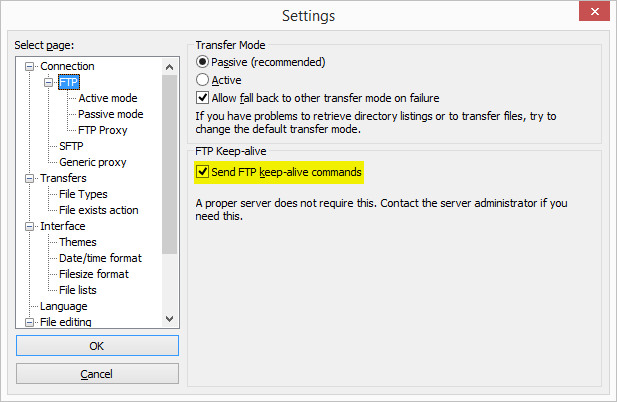
The way around this is to make the client to keep the TCP/21 connection from going idle. If using a 3rd party FTP client, there may be configuration knobs the user can turn in order to cause the FTP client to send a keepAlive. As an example of how you can set this in FTP client software, in FileZilla, you go to Edit, Settings, Connection, FTP, and check Send FTP keep-alive commands.
If the FTP client is being written in .NET, customers will need to account for this client-side keepAlive in their code. Here is a sample (the keepAlive is highlighted):
private void button1_Click(object sender, EventArgs e)
{
System.Net.ServicePointManager.SetTcpKeepAlive(true, 30000, 20000);
try
{
System.Net.WebClient oFTPDownloadWebClient = new System.Net.WebClient();
oFTPDownloadWebClient.Proxy = null;
oFTPDownloadWebClient.Credentials = new System.Net.NetworkCredential("username", "password");
oFTPDownloadWebClient.DownloadFile(new System.Uri("ftp://contosoFTP.cloudapp.net/LargeFile.Dat"), "C:\\Temp\\Big.dat");
return;
}
catch (System.Exception ex)
{
MessageBox.Show(ex.Message);
}
}
Load balanced endpoints are not supported in Azure Passive FTP server
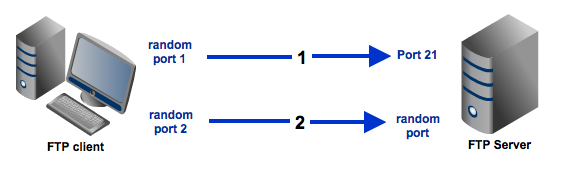
You will be unable to load balance your endpoints when using a Passive FTP server in Azure since there is no session stickiness between the server’s Command Port (21) and the random data ports that get selected when there is data being transferred btw the client and the ftp server.
The client will contact the FTP server (Azure VM) through Port 21 (Server’s Command port), and establish an FTP session. Then as soon as the client tries to download or upload data, the FTP server (Azure) will send a hashed port number to the client (from the list of data ports you select when setting up your FTP service).
It will look like:
ReplyCode: 227, Entering Passive Mode <h1,h2,h3,h4,p1,p2>
Entering Passive Mode (<ftp_svr_ip>, a, b)
The port can be calculated as:
Random Ephemeral Port = (a*256) + b
The server will select a random ephemeral port for every data session that is opened (within the port range specified when setting up the FTP service).
Let’s say you have Azure FTP Servers FTP1 and FTP2 behind the load balancer.
You place FTP1 and FTP2 in the same cloud service;
You load balance Port 21 and all the data ports across these two VM’s;
The client tries to establish an FTP session (through Port 21), and the LB first selects FTP1 .
The client then chooses to download a file from FTP1.
FTP1 will respond back to the client and provide a random data port that the client will need to use to access its data channel;
The client then has to set up a new TCP session with that target data port on FTP1, and this request goes through the Load Balancer;
The LB, which is not configured with sticky sessions, and is just a Layer 3 round robin LB, will not keep track of the session previously established with FTP1 and may pick FTP2 instead.
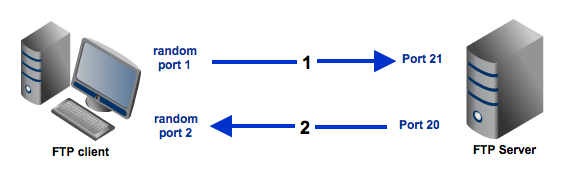
While this can work with Active FTP (since no endpoint is required for outbound traffic, and since active FTP just uses Src Port 20 to initiate the data channel with the client).
ACTIVE FTP
PASSIVE FTP
Running concurrent traces on the client and the 2 Azure FTP servers will show this.
Conclusion
The first four steps and the fifth step are general steps which you should complete to setup a passive FTP on a Windows server however the 4th step is specific to Windows Azure. Another point to note is that currently Windows Azure only support 150 endpoint. Keep this in mind when adding endpoints. The last step is just a verification step where we trying to conclude that the FTP server is actually using the ports that we specified.
Hope this post was helpful!