Signcryption - Related Work
ElGamal Signcryption
The original signcryption scheme that has been introduced by Youliang Zheng in 1997 is created on a derivation of ElGamal digital signature standard, combined with a public key encryption scheme.
Based on discrete algorithm problem, ElGamal Signcryption cost is:
•58% less in average computation time
•70% less in message expansion
Here is the detailed presentation of the fifth algorithms that make up the ElGamal signcryption scheme.
1)Setup
Signcryption parameters:
p = a large prime number, public to all; q = a large prime factor of p-1, public to all;
g = an integer with order q modulo p, in [1,… , p-1], public to all
hash = a one-way hash function;
KH = a keyed one-way hash function = KHk(m) = hash(k, m)
(E, D) = the algorithms which are used for encryption and decryption of a private key cipher.
Alice sends a message to Bob.
2)KeyGen sender
Alice has the pair of keys (Xa, Ya):
Xa = Alice’s private key, chosen randomly from [1, .., q-1];
Ya=Alice’s public key = mod p
3)KeyGen receiver
Bob has the pair of keys(Xb, Yb):
Xb = Bob’s private key, chosen randomly from [1, .., q-1];
Yb = Bob’s public key = mod p.
4)Signcryption
In order to signcrypt a message m to Bob, Alice has to accomplish the following operations:
Calculate
Split k in k1 and k2 of appropriate length.
Calculate r = KHk2(m) = hash(k2, m)
Calculate s = x/(r+Xa) mod q, if SDSS1 is used
Calculate s = x/(1+Xa ∙ r) mod q, if SDSS2 is used
Calculate c = Ek1(m) = the encryption of the message m with the key k1.
Alice sends to Bob the values (r, s, c).
5)Unsigncryption
In order to unsigncrypt a message from Alice, Bob has to accomplish the following operations:
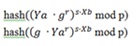
Calculate k using r, s, g, p, Ya and Xb
Split k in k1 and k2 of appropriate length.
Calculate m using the decryption algorithm m = Dk1(c).
Accept m as a valid message only if KHk2(m) = r.
ECC Signcryption
The first signcryption scheme was introduced by Yuliang Zheng in 1997. Zheng also proposed an elliptic curve-based signcryption scheme that saves 58% of computational and 40% of communication costs when it is compared with the traditional elliptic curve-based signature-then-encryption schemes .
The elliptic curve-based schemes are usually based on difficulty of Elliptic Curve Discrete Logarithm Problem (ECDLP) that is computationally infeasible under certain circumstances. The elliptic curve-based systems can attain to a desired security level with significantly smaller keys than those of required by their exponential-based counterparts. This can enhance the speed and leads to efficient use of power, bandwidth, and storage that are the basic limitations of resource-constrained devices
SECURITY MODELS FOR SIGNCRYPTION
1) TWO-USERS SECURITY MODEL
In the symmetric setting, there is only one specific pair of users who
(1) share a single key;
(2) trust each other;
(3) “know who they are”;
(4) only care about being protected from “the rest of the world.”
2) MULTI-USER SECURITY MODEL
A central difference between the multi-user model and the two-user models is the extra power of the adversary. In the multi-user model, the attacker may choose receiver (resp. sender) public keys when accessing the attacked users’ signcryption (resp. unsigncryption) oracles. For signcryption schemes that share some functionality between the signature and the encryption components, such as are the case for Zheng’s Signcryption scheme and Schnorr Signcryption scheme, the extra power of the adversary in the multi-user model may be much more significant, and a careful case-by-case analysis is required to establish security of such schemes in the multi-user model.
As in the two-user setting, the multi-user setting also has two types of models depending on the identity of the attacker: an insider model and an outsider model.
Practical implementation of Signcryption in real life
The shared secret key between the parties makes possible an unlimited number of applications. Among these applications, one can first think of the following three:
•secure and authenticated key establishment,
•secure multicasting, and
•authenticated key recovery.
A number of signcryption-based security protocols have been proposed for aforementioned networks and similar environments. These include:
•secure ATM networks,
•secure routing in mobile ad hoc networks,
•secure voice over IP (VoIP) solutions,
•encrypted email authentication by firewalls,
•secure message transmission by proxy, and
•mobile grid web services.
There are also various applications of signcryption in electronic commerce, where its security properties are very useful. Analyzing this security scheme from an application-oriented point of view, can be observed that a great amount of electronic commerce can take advantage of signcryption to provide efficient security solutions in the following areas:
•electronic payment,
•electronic toll collection system,
•authenticated and secured transactions with smart cards.