Microsoft InTune for the Old-School GPO Admin
Happy New Year, people! Let me welcome you to the first post of 2016 for the Ask PFE Platforms blog.
I have a history of posting on our blog around the holidays/New Year's and 2016 is no different.
Last year, I did a "New Year's" post about Azure AD for the old-school AD admin:
In keeping with that same "old-school" spirit, today I'll discuss InTune for the old-school GPO Admin.
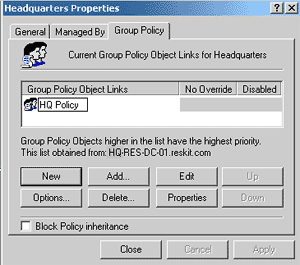
GPO Review
Let's do a quick level-set for GPOs:
- A GPO is a setting (or a collection of settings) we want to apply to a computer (or a certain user of a computer)
- Code runs on the "target" system (client or server OS) at boot/logon/intervals to determine what GPOs are scoped/linked to the OU/user/computer object in AD. Then it retrieves the SYSVOL-based file elements of the associated GPO(s) and applies those settings to the system(s).
- As far as administration goes, we have the GPMC (built in/free down load) or AGPM (for cost), as well as some 3rd party alternatives
This works all well and good in a traditional on-prem environment where a DC is never very far away. Even in a remote/disconnected situation, as long as the system will regularly connect back up to the on-prem network (and DC), GPOs have been providing configuration control for well over a decade.
Since we're talking old-school here, anyone else recall the adventures of GPO editing circa Windows 2000?
In today's mobile-first, cloud-first world, things are evolving. There are more and more situations where there is no "on-prem" or connectivity to on-prem AD/DCs is few and far between (if ever). Another situation that is now common is "Bring Your Own Device" (BYOD) - where the devices that people use may not be Windows-based, aren't corporate owned and likely aren't joined to the corporate AD).
So how do we manage devices and users who are out and about?
Hello Microsoft InTune
"Intune is a cloud-based service that lets you manage mobile devices, PCs, and apps so your users can be productive while you protect your company's information."
InTune does wwwwayyyy more than just device settings management (which you'll see as you read on) but in that regard, at a high level, InTune settings management is the same idea as Group Policy: There is a setting (or a collection of settings) that we want to apply to a given device.
The design and implementation is different, though. Whereas Group Policy was designed for a well-connected, private on-prem environment, InTune was designed more for a public Internet-connected environment.
InTune utilizes open standards for Mobile Device Management (MDM). Settings are defined via properly formatted XML config files that adhere to a set of open standards known as "OMA-DM" (developed by the Open Mobile Alliance - https://openmobilealliance.org). Client-side code retrieves the config file(s) as messages from a secure Internet URL and applies the settings to an "enrolled" system. Other protocols used are WAP or Wireless Application Protocol – often used by the back-end to 'push' a notification to a device to come get a configuration. Outside of the MDM side, InTune has a client for rich end-point management (actually, the Intune client is multiple sub-client pieces based on SCCM, SCOM and SCEP agents).
One point of differentiation between GPOs and InTune is in settings quantity. With InTune, there are far fewer settings than in the GPO world. However, in many ways, 'less is more' - with Intune, the idea is to simplify. Also, in my experiences, there is a fairly narrow list of "common" GPO settings used by most orgs. In fact, I'd wager that there are GPO settings that you and I have never even looked at.
Another difference is for the BYOD scenarios. With GPOs, the device needs to be domain-joined for the GPO to apply but with InTune, that isn't the case. You can manage settings on a non-Domain-joined device; such as a user's personal tablet or smartphone. This way, your users can use their own devices to work with corporate apps/data, yet they aren't fully locked down. InTune "enrollment" can ensure those devices adhere to certain compliance levels/settings for your corporate data/apps - such as requiring a PIN or device encryption - but other aspects of the device remain unaffected. A recent feature-add for InTune is known as "Mobile Application Management" or MAM. The idea with MAM is for IT to manage/control the apps/data on a device without the device even needing to be enrolled in the InTune service. More about this feature can be found here:
One more difference between InTune and Group Policy is support for non-Windows platforms. With GPO, that never really took off (outside of a few exceptions) but with InTune, you can manage non-Windows devices (Android, IOS), as well as Windows Phone and tablet (RT) devices.
The back end:
- The back-end in the GPO world is AD and SYSVOL. On premises, GPOs are filtered based on OU location of the user and/or computer, security filtering or via a WMI filter.
- With InTune, the back-end is your InTune subscription in the Azure cloud and policies are filtered via license and/or user/computer groups.
- Another excellent aspect of InTune (out of scope here) is the integration capability of InTune and on-prem SCCM. You can integrate your InTune subscription with your on-prem SCCM infrastructure, giving you a single tool to view and manage your on-prem and on-line devices
The front end:
- GPOs are processed by an element of the WinLogon service or the Group Policy Client service (depending on the OS version)
- With InTune, there is built-in code for MDM processing in many of the supported devices – and/or a client - to process the settings
- More MDM details - https://technet.microsoft.com/en-us/library/dn600287.aspx
The Intune Client
The InTune Client can be installed on Windows PCs that don't have built-in support - such as Windows 7
- https://technet.microsoft.com/en-us/library/dn646975.aspx
- In this regard, InTune is a lot like a cloud-hosted System Center solution (SCCM, SCEP and SCOM)
!! ALERT !! – the agent will not install if there is already an SCCM agent installed on the client
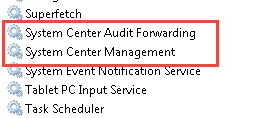
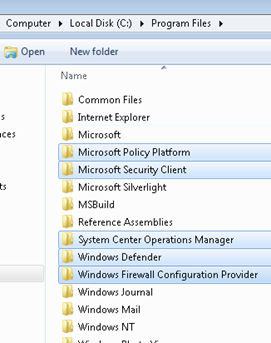
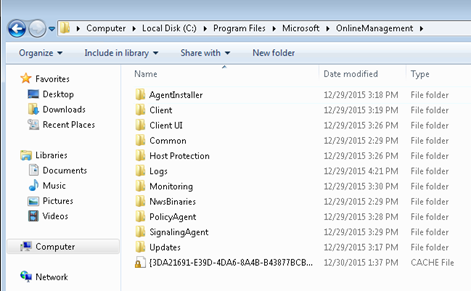
Similar to the on-prem SCCM client, there are multiple services/files/components added by the "Agent" that provide functionality for inventory, updating Windows, updating and configuring Endpoint Protection, remote assistance and health monitoring/alerting, etc.
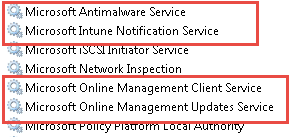
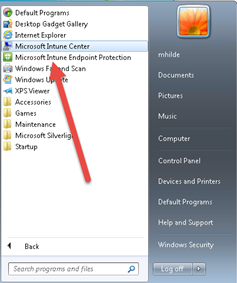
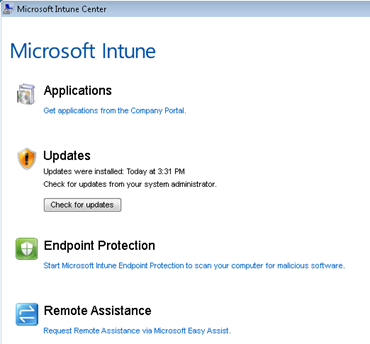
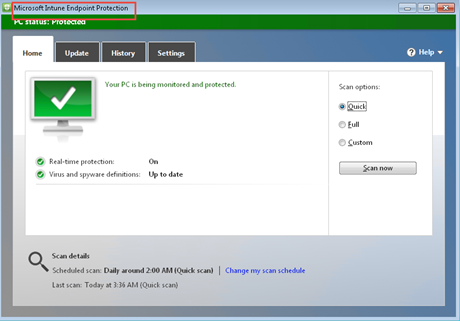
The agent adds the Microsoft Intune Center and End Point Protection UIs that let end-users to perform several 'self-service' functions:

Windows 8.1 Start screen Tiles:

Microsoft InTune Center UI
Endpoint Protection client delivered/configured and managed via InTune…
Files/folders related to the client install…
More files/folders from enrollment in InTune…
Some of the registry entries/information added during the client install:
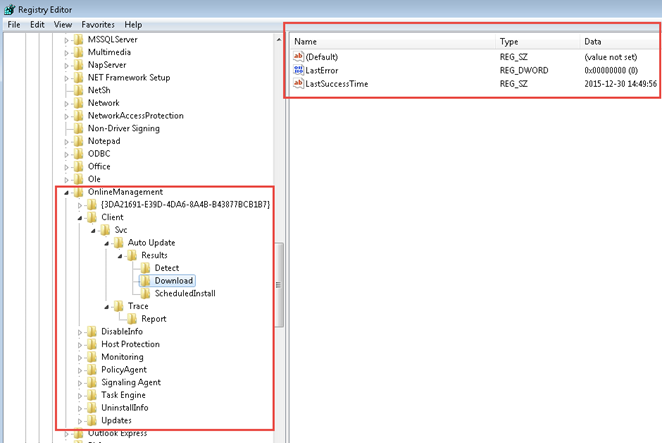
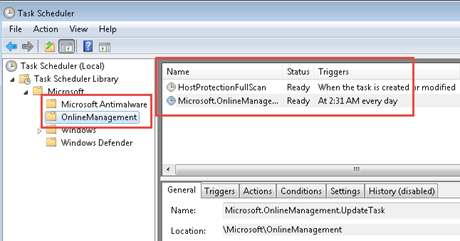
Scheduled Tasks are added to a managed system via the InTune client install …
Admin Portal Demos
I can't really demo much for you on a 'static' blog post but I can provide some screen shots here so you get a feel for the UI/workflow.
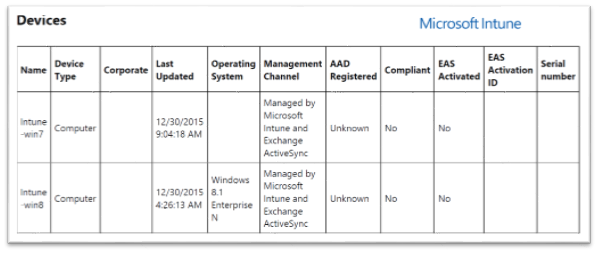
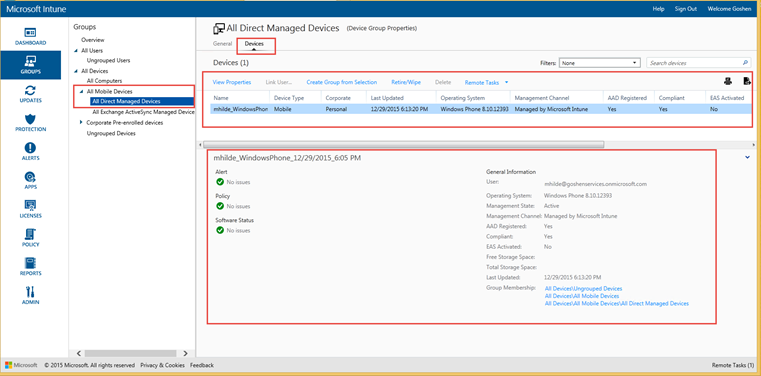
The following is based on an InTune subscription with a Windows 7 and Windows 8.1 PC enrolled, as well as a Windows Phone 8.1 device.
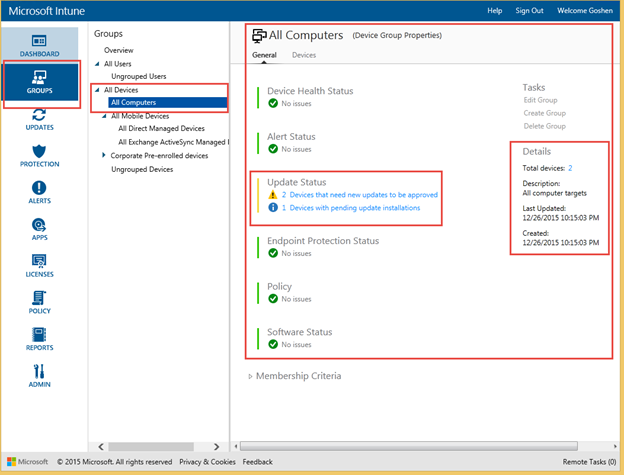
The InTune Portal showing the 'General' page for All Computers Group:
Portal showing the 'Devices' page for All Computers Group with "Intune-Win8" PC highlighted and subsequent details/available actions shown:
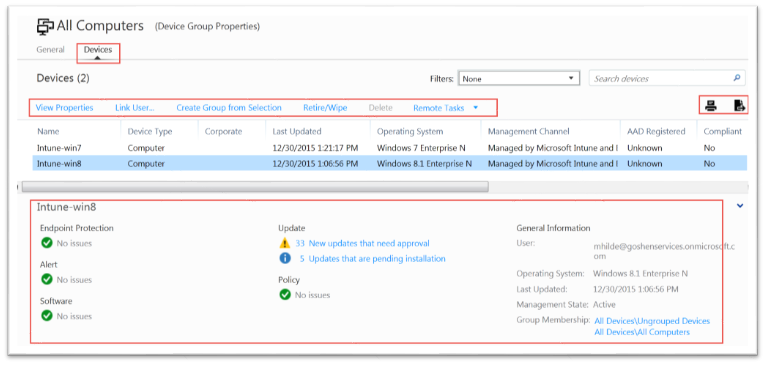
- If you highlight a selection and then click the printer button (upper-right red box above), you can get a nice print out (or a PDF if you print to a file):
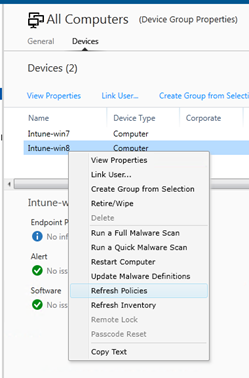
Right-clicking the highlighted object offers a context menu/actions such as refresh policies, initiate a scan, etc:
- The "Copy Text" function is handy to quickly copy some information out of the portal
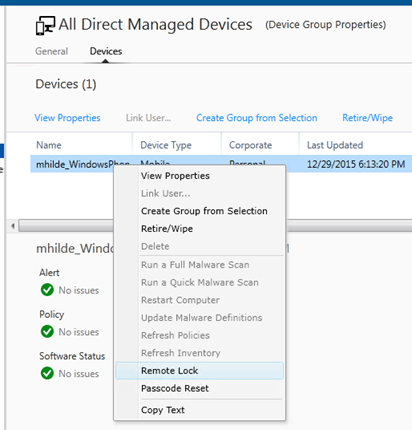
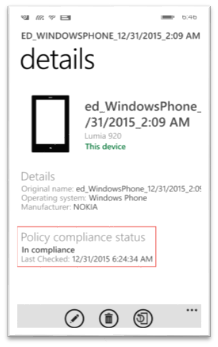
Windows Phone device details listed in the Mobile Device group:
Right-click context menu for the Windows Phone – remote lock could be helpful if someone reports a lost device:
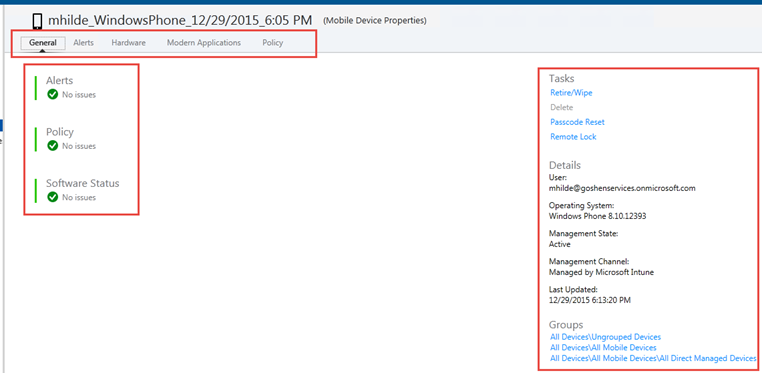
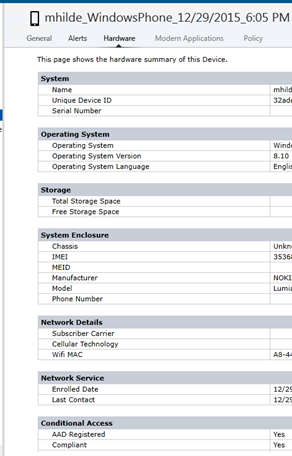
You can also double-click the device and bring up its details page and several tabs of information and actions, including last update time, hardware inventory, etc:
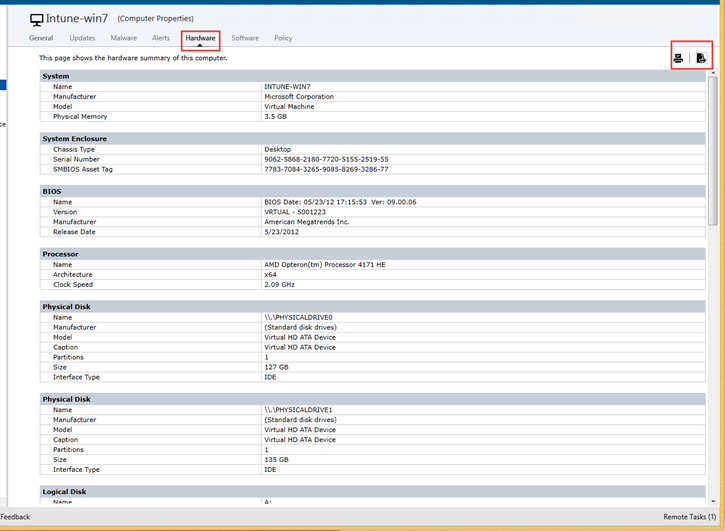
The Windows 7 PC (Intune-Win7) has a similar page with details, tabs and actions…
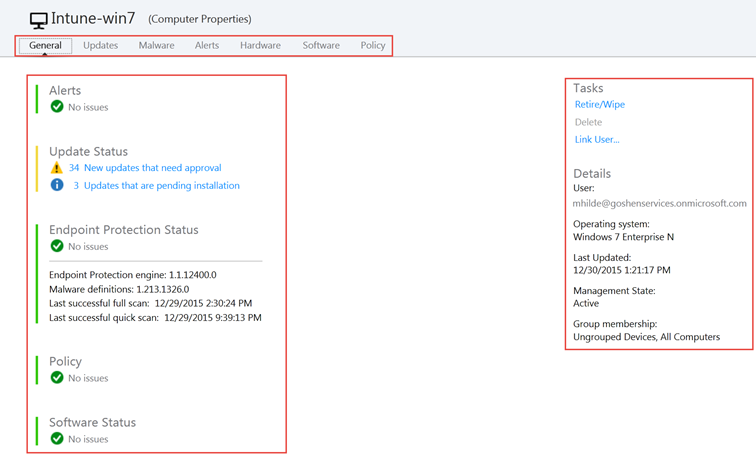
…including detailed hardware inventory (which can flow through to your SCCM inventory if you've enabled SCCM integration).
- Again, notice the Print and "export to CSV" buttons.
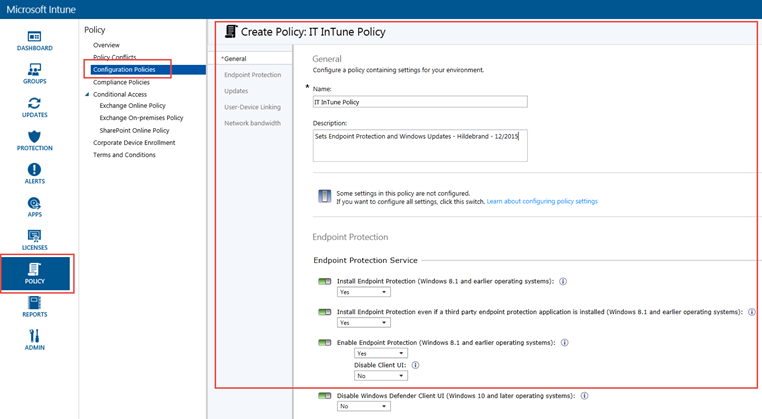
Using the admin portal, there are common Configuration Policies and Compliance Policies that can be defined for various flavors of devices (i.e. Windows, Android, IOS):
- https://technet.microsoft.com/en-us/library/mt147409.aspx
- https://technet.microsoft.com/en-us/library/dn913730.aspx
Custom settings can be defined with an element of the OMA standard known as OMA-URI ("Uniform Resource Identifier"). Custom settings support rapidly expanded in Win 8.1 and again with Win 10 but like I said before, it isn't to the same level of Group Policy (or the almost infinite possibilities of GPP):
The OMA-URI idea is similar in concept to how you'd create custom ADM templates in GPO-land; create files that specify a registry path/settings or other configurations and then InTune distributes the settings to the target devices so they can process/apply the settings:
Here are some screenshots of setting up a "Configuration Policy" (Endpoint Protection and Windows Update settings)
- Note the Description field entry I put in there – What? Who? When? – STANDARDS! STANDARDS! STANDARDS!
And a "Compliance Policy" (security settings and such for a mobile device)
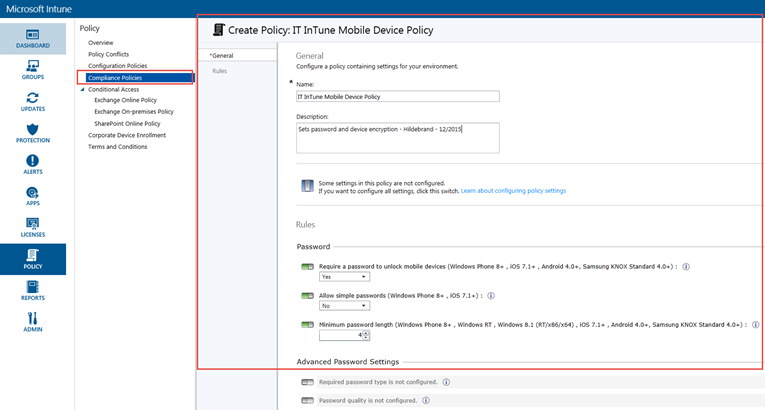
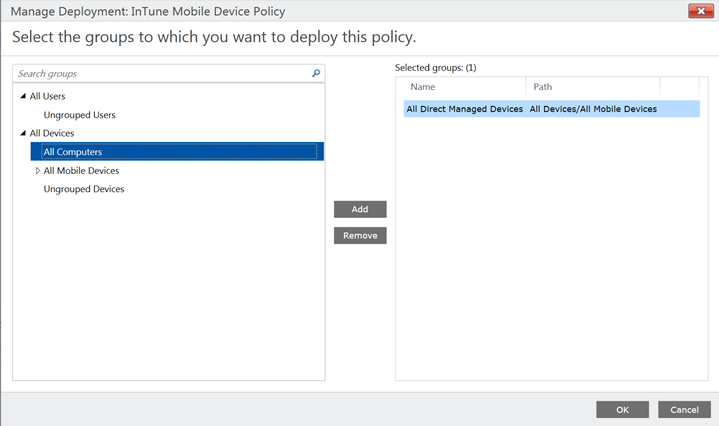
Once a Policy is created, you are prompted to 'Deploy' the Policy:
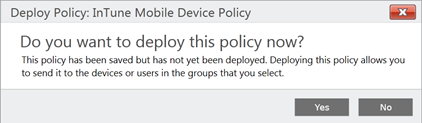
I clicked Yes and I was prompted to select a group to deploy the policy to:
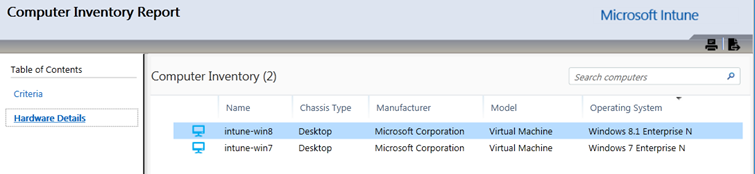
Here, we have Reporting:
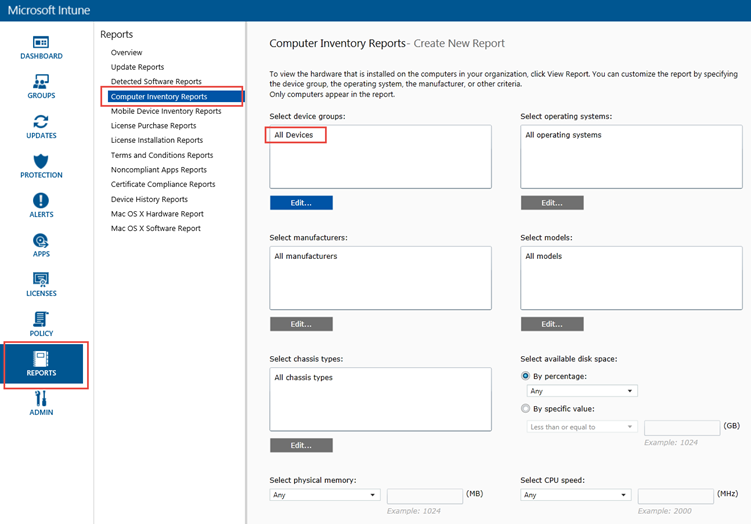
A sample of a Computer Inventory Report
In the Admin section of the Portal, you'll find some great features of InTune - including role based administration (under Administrator Management) and one of my favorites – "Alerts and Notifications."
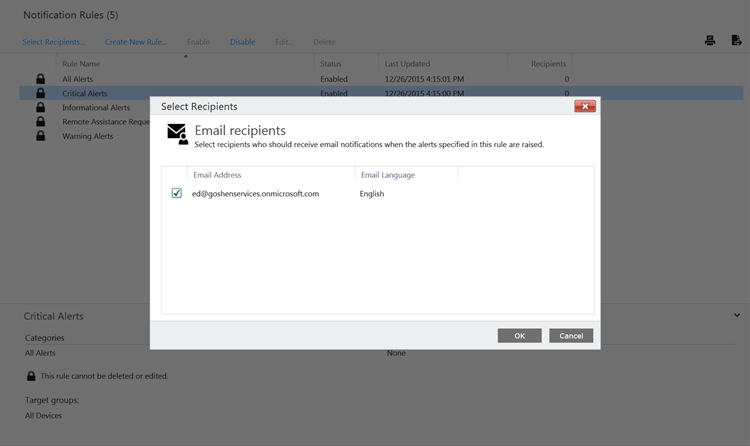
This is where you can setup/customize Alerts for certain conditions across your managed devices, then setup Notification Rules and Recipients to send emails to:
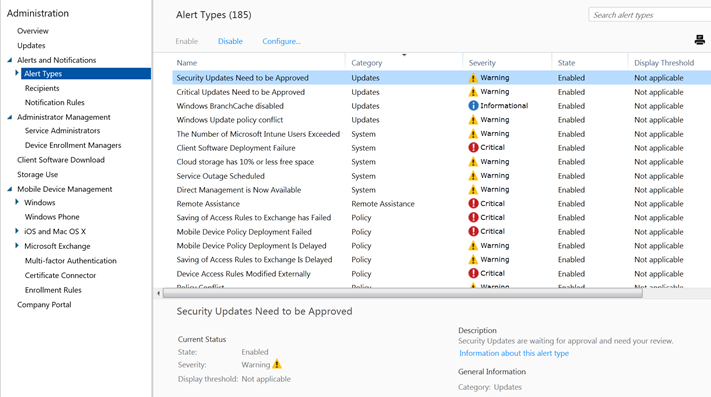
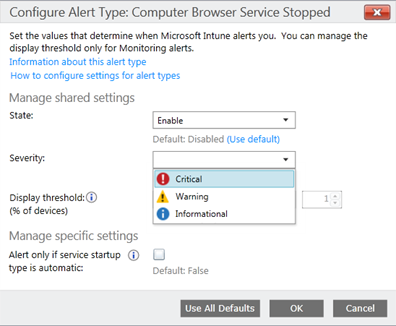
Double-click the desired Alert and configure the details:
Add a recipient(s) for the Notification:
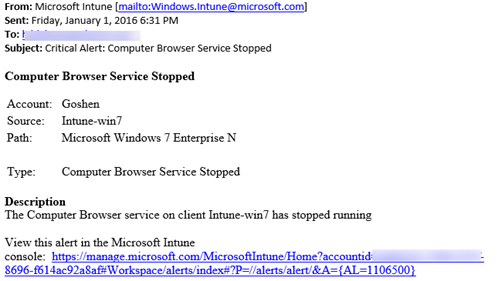
A sample email from the above Alert/Notification:
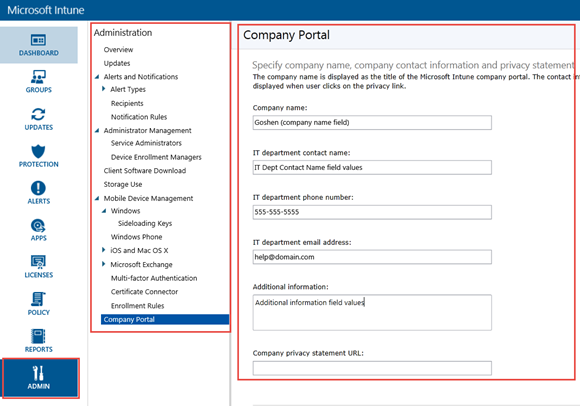
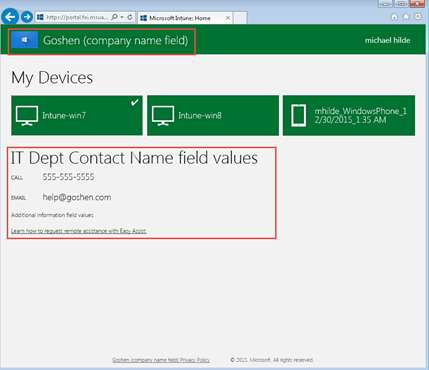
Company Portal branding and customizations can be also be added/edited from the Admin section. This is simple stuff, but sooooo helpful to end users and it can really make a big difference for your users when they see your corporate logo, company name and a predictable spot to get the helpdesk phone number and/or email address.
A screenshot of the Company Portal webpage (from the Intune-win7 PC) – the URL is https://portal.manage.microsoft.com
- Notice some of the custom branding/logos/details and the devices I've registered to my ID:
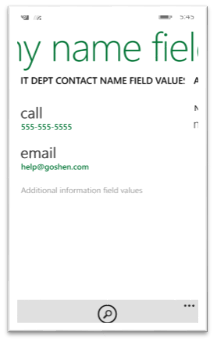
A few screenshots of the Company Portal App (from an enrolled Windows Phone 8.1 device)


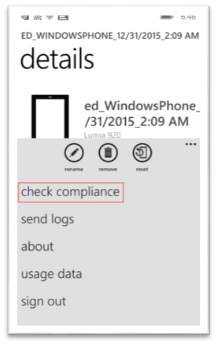
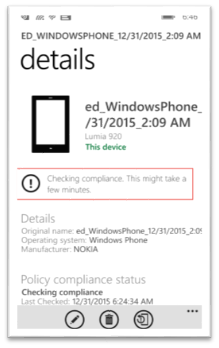
A user-initiated device compliance check from an enrolled Windows Phone 8.1 device
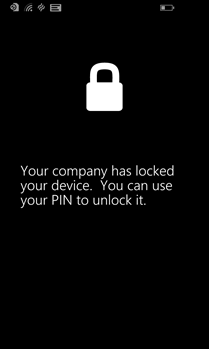
Here's the device after I sent a "Lock" to it via the Portal
A Few FAQs
Here are some common questions/tasks and how we do them with InTune:
"With GPOs, we can force a client-side refresh with GPUPDATE /FORCE – how do we do it in InTune?"
- Depending on the device, the user can open the Company Portal app and force a compliance check from their device (shown above for a Windows Phone).
- For the life of me, I couldn't figure out how to get a client to initiate an 'ad-hoc' policy refresh. If I find out (or anyone knows), I'll update the post.
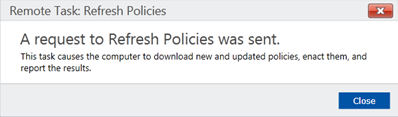
- The admin can sign in to the InTune admin portal and push a policy refresh:
- Click Groups and then select a device group
- Select the devices you want to refresh policies and then click Remote Tasks > Refresh Policies.
- Click Remote Tasks in the bottom-right corner of the Microsoft Intune administrator console window to check the task status.
- Depending on the device, the user can open the Company Portal app and force a compliance check from their device (shown above for a Windows Phone).
"With GPOs, they refresh at regular intervals – what are the InTune device refresh timing intervals?"
"When a policy or app is deployed, Intune immediately begins attempting to notify the device that it should check-in with the Intune service. This typically takes less than 5 minutes."
"If a device doesn't check in to get policy after the first notification is sent, 3 more attempts are made. If the device is offline (for example, it is turned off, or not connected to a network) then it might not receive the notifications."
- In this case, the device will get policy on its next scheduled check-in with the Intune service as follows:
Platform |
Check-in frequency after initial notification |
iOS |
Every 6 hours |
Android |
Every 8 hours |
Windows Phone |
Every 8 hours |
Windows PCs enrolled as devices |
Every 24 hours |
- If the device has just enrolled, the check-in frequency will be more frequent as follows:
Platform |
Frequency |
iOS |
Every 15 minutes for 6 hours and then every 6 hours |
Android |
Every 3 minutes for 15 minutes then every 15 minutes for 2 hours, and then every 8 hours |
Windows Phone |
Every 5 minutes for 15 minutes then every 15 minutes for 2 hours, and then every 8 hours |
Windows PCs enrolled as devices |
Every 3 minutes for 30 minutes, and then every 24 hours |
"Can I see the last time a device(s) refreshed?"
- Yes – on the device (Intune Center UI, Company Portal app), several places in the InTune management portal including Reports.
"What if GPO and InTune settings conflict?"
- https://technet.microsoft.com/library/dn646986.aspx
- "When conflicts happen, domain-level Group Policy takes precedence over Intune policy, unless the computer can't logon to the domain. In this case, Intune policy is applied to the client computer."
- https://technet.microsoft.com/en-us/library/dn913730.aspx
A Portal among portals
I don't normally like web portals much but I have to say, the InTune portal is excellent.
With the clean, uncluttered UI, the right-click context menus, obvious clickable links/actions (in blue), information/details, copy text, printing, exporting, etc, I honestly forgot I was using a web portal.
Additional Resources
A few more resource – the first is a is a long but very informative whitepaper about much of the MDM details (this is required reading for a background in MDM protocols and such)
- Whitepaper - https://technet.microsoft.com/en-us/library/dn499787.aspx
- What to know before setting up InTune - https://technet.microsoft.com/en-us/library/dn646966.aspx
- Documentation for InTune - https://technet.microsoft.com/en-us/library/jj676587.aspx
- Manage Mac OS via InTune - https://blogs.technet.com/b/microsoftintune/archive/2015/11/23/introducing-intune-support-for-mac-os-x-management.aspx
Well folks, there you have it…some discussion, thoughts and screenshot-mania around InTune from the viewpoint of an old-school GPO Admin.
As you can see, InTune is a feature-rich solution that addresses many requirements, including device settings management but also well beyond. There are some aspects of Intune that I didn't touch on - such as SCCM integration, app deployment and licensing,
Even in leaving out those elements, this post is one of those projects that just kept growing. The more I worked on it, the more I learned and the longer the post became.
Hopefully, you found it helpful and Microsoft Intune is a little less mysterious for you.
This is my last post for the Ask PFE Platforms blog as I'm departing the PFE ranks and taking on a new role at Microsoft. Thanks for your readership and comments over the last several years - this blog has been one of my most enjoyable endeavors.
Soon, I hope to find another TechNet blog where I'll be able to make some more Internet noise but the other Plat PFEs here will keep you informed and entertained.
Cheers - and here's to getting/being more "Cloud Ready" in 2016!
Hilde