Client Certificate Authentication (Part 2)
This is a continuation of my earlier post on Client Certificate Authentication (Part 1) aka TLS Mutual Authentication. Earlier, I had discussed on what Client Certificates are and how they work in SSL/TLS Handshake.
In this post, I will explain how to review SSL/TLS handshake with help of tools like WireShark & Curl .
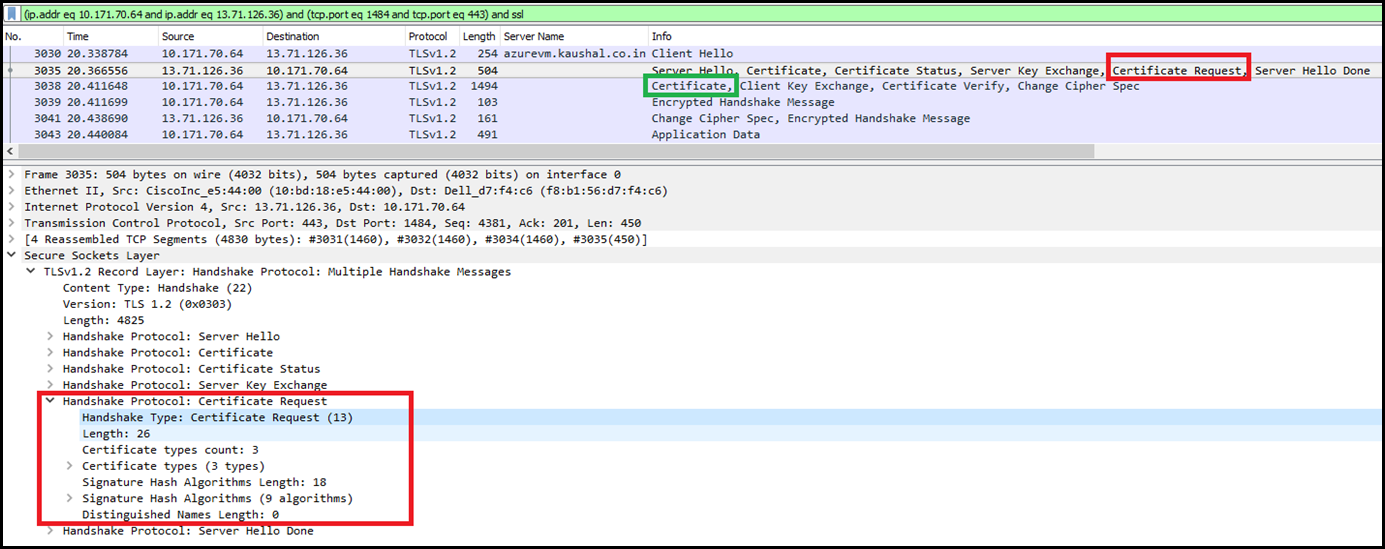
Before proceeding further, lets review the SERVER HELLO definition in RFC 5246. As per the RFC, the server will request the certificate from the client in the Server hello by including certificate_request message, which has the decimal code of 13 (0d in Hex ) . This will help us in determining the Certificate Request in Server Hello.
|
Once the client sees the certificate_request message it will provide the certificate to the server.
Real world example:
Setup: Hosted a site on IIS inside an Azure VM. This requires a client certificate for authentication. Here is the endpoint https://azurevm.kaushal.co.in
I have added the SSL binding via netsh using the following command:
netsh http add sslcert ipport=0.0.0.0:443 certhash=<certificate thumbprint goes here> appid={4dc3e181-e14b-4a21-b022-59fc669b0914} certstorename=My clientcertnegotiation=enable
Analyzing the TLS/SSL handshake in WireShark
As shown below, the server has sent a certificate request message to the client and the client has then responded with the certificate in the next communication.
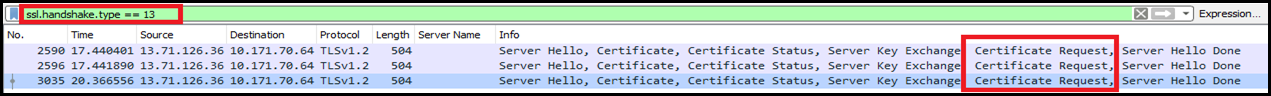
In WireShark you can set the filter to “ssl.handshake.type == 13” to specifically look for certificate_request message in Server Hello.
NOTE: Some SSL/TLS servers support only Secure negotiation. Therefore you may not see the Certificate Request message explicitly in the Server Hello. In this case, the server will send the Certificate Request message as a part of the Encrypted Handshake Message.
Analyzing the TLS/SSL handshake in cURL
By far, cURL has made it easier to determine if the server is sending the Certificate Request in Server Hello. You will have to download the version of curl that includes support SSL Protocol. This works in scenarios where the server supports only Secure Negotiation. I
You can find various builds of cURL available for download here: https://curl.haxx.se/dlwiz/?type=bin&os=Win64&flav=-&ver=*&cpu=x86_64
I am using the following
curl version: 7.54.0 - SSL enabled SSH enabled
URL: https://bintray.com/artifact/download/vszakats/generic/curl-7.54.0-win64-mingw.7z
Execute the following from command prompt
curl –v https://<hostname> –k –cert clientcert.pem:<password> Where, -v, --verbose Make the operation more talkative-k, --insecure Allow connections to SSL sites without certs (H)-E, --cert CERT[:PASSWD] Client certificate file and password (SSL)
Once the request has been issued via cURL. In the verbose output, search for TLS handshake message “Request CERT (13) ” as highlighted in the below example.
|
On Windows, in order to pass the client certificate via cURL, you will have to extract the .pem file out of the .pfx. Use the following command:
|
HTH,
Kaushal