ACS integration with Windows Live ID & Facebook Connect
I’ve received several requests regarding ACS and Windows Live ID integration for websites. This post describes what you can do with ACS and Windows Live ID today (with the new release of ACS). It takes a bit of code, but the integration is pretty straightforward.
Note that this code isn’t hardened and it relies heavily on server side code. I’m showing it as an architectural sample, and I’m showing it now based on the number of requests I’ve received for the sample. In the future, I’ll work on a better sample that’s easier to setup (and possibly one that uses javascript & cross domain iFrames).
I’ll be discussing WLID Web Authentication as an integration point. The same basic model can apply to other WLID capabilities and other web identity providers. The code sample also has Facebook connect integration, but I won’t go into any detail about how it works in this post (in the future I will).
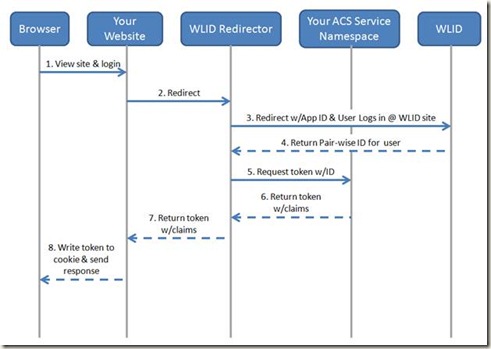
The basic model is fairly simple. The swim lane and description is shown below.
1. A user browses to your website and clicks a login button.
2. This button redirects the user to the WLID Redirector. The code for this redirector is in this post. For now, you’ll need to write and host this code yourself.
3. The redirector redirects the browser to the WLID login page with correct WLID AppID. From there, the user logs into WLID using their credentials.
4. Upon a successful login, WLID returns the browser to the redirector. The response contains a unique pair-wise ID for that user.
5. Once the redirector receives the user ID, it packages that ID into an ACS token request (OAuth WRAP request for an Access Token)
6. ACS will issue a token for that user and return it to the redirector (the token is a SWT).
7. From there, the redirector will return the ACS token to the website
8. The website will validate the token. If validation passes, the website will write the token to a cookie.
9. (Not shown on the diagram) On subsequent requests to the website, the website will use the cookie to authenticate and authorize the user.
10. (Not shown on the diagram) If the user logs out, the website will clear the cookie and send the browser to the redirector. From there, the redirector will send the browser to WLID for logout. This will remove the WLID cookie for that website.
Setup Steps IdpRedirector project
1. First, you’ll need to have a domain name for the redirector. You can host the redirector in Azure, or your own server. The site needs to have a public address.
2. After you have the address, go to the Live ID developer portal at https://go.microsoft.com/fwlink/?LinkID=144070
3. Setup your WLID developer account. The steps are at https://msdn.microsoft.com/en-us/library/bb676626.aspx.
The only trick here is to be very careful about the return URL. For this sample, you’ll want to enter https://<yourdomainname>/wlidfederation-handler.aspx, where <yourdomainname> is the hostname + any subdomains for your redirector.
4. Copy the Application ID and Secret shown below
5. Open the VS solution in the zip at the bottom of this post.
6. In the WebRedirector project, open the web.config and edit the values below with your Application ID and secret.
<add key="wll_appid" value="yourappid"/>
<add key="wll_secret" value="yoursecret"/>
7. Change the rploginpage and rplogoutpage to the URL for the RelyingPartyWebsite project. I used Cassini in this project, so your port number will likely change.
<add key="rploginpage" value="https://localhost:32210/RelyingPartyWebsite/login.aspx"/>
<add key="rplogoutpage" value="https://localhost:32210/RelyingPartyWebsite/logout.aspx"/>
8. Update the ACS specific settings.
<add key="serviceNamespace" value="updateToYourServiceNamespace"/>
<add key="clientIssuerKey" value="updateToYourIssuerKey"/>
<add key="clientIssuerName" value="updateToYourIssuerName"/>
<add key="tokenPolicyKey" value="updateToYourTokenPolicyKey"/>
<add key="acsHostName" value="accesscontrol.windows.net"/>
<add key="applies_to" value="updateToYourAppliesTo"/>
9. Upload the project to the domain specified in (3)
Setup Steps RelyingPartyWebsite project
10. Open the web.config of the RelyingPartyWebsite in VS. Update the appSettings below to the settings for your ACS Service Namespace & the domain of your IdPRedirector.
<add key="idpRedirectHost" value="updateToYourRedirectorHost"/>
<add key="serviceNamespace" value="updateToYourServiceNamespace"/>
<add key="tokenPolicyKey" value="updateToYourTokenPolicyKey"/>
<add key="acsHostName" value="accesscontrol.windows.net"/>
<add key="applies_to" value="updateToYourScopeAppliesTo"/>
Running The Sample
11. Start the RelyingPartyWebsite and browse to the Default.aspx page. You should see something like the following:
12. If you click on the WLID icon, you’ll be redirected to the IdPRedirector, then to WLID. Enter your creds at WLID & you should be redirected back to the IdPRedirector, then to the login.aspx page in RelyingPartyWebsite. If all is well, you’ll see something like:
Here’s the code sample: