SYSK 305: What is a MITM attack?
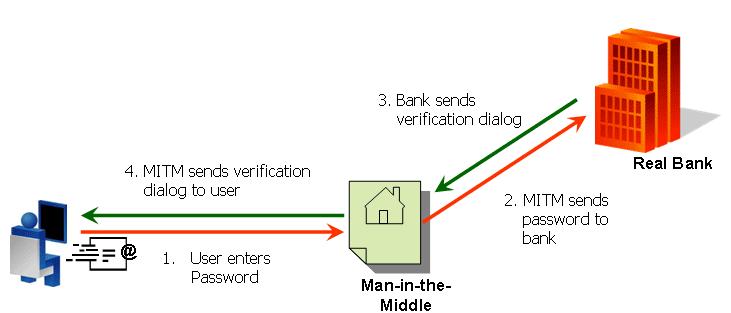
MITM stands for man-in-the-middle… A MITM attack is where an attacker is able to read, insert and modify messages between two parties without either party knowing that the link between them has been compromised.
For following picture from http://www.arcot.com/mitm/index.html demonstrates the concept:
Some may think that using secure HTTP (https) eliminates the possibility of a MITM attack. Unfortunately, there are several ways a malicious person can perform a MITM attack even if SSL is used, including ARP poisoning, DNS hijacking, DNS cache poisoning, DHCP message subversion/take-over, gateway take-over with GARP, HSRP, VRRP, IRDP, STP, EIGRP, ICMP redirects, etc.
So, what can you do to protect against these types of attacks?
For starters, don’t use your wireless connection for transmitting any sensitive information. Next, make sure you’re using a web application firewall, in addition to your traditional firewall/router.
Finally, get educated about IPSec encryption, DNSSEC for DNS, DHCP Snooping, IP/MAC Source-Guard, Dynamic ARP Inspection, and static ARP entries. While, as an individual user some of this is not under your control, understanding security issues and ways to address them should enable you to make smarter decisions about the sites you use, the companies you do business with, etc.
And, as always, keep checking for what’s new in the world of security – hackers are becoming increasingly more sophisticated and it’s a constant tug-a-war between the “good guys” and those who are trying to access data without authorization or just to harm.
Sources:
http://en.wikipedia.org/wiki/Man_in_the_middle