Azure ARM: VM Domain Join to Active Directory Domain with "JoinDomain" Extension
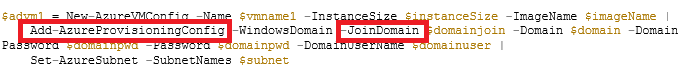
It is a pretty common scenario to provision a Virtual Machine (VM) in Azure and join it to an existing Active Directory (AD) Domain, either extended from on-premises via hybrid connections, or natively deployed in the cloud installing Domain Controllers (DCs) into Azure VMs. Using legacy Azure Service Management API (ASM), a nice PowerShell cmdlet called “Add-AzureProvisioningConfig” is available, with “ -JoinDomain” switch to automatically join the VM to an AD domain as in example below:
Add-AzureProvisioningConfig
https://msdn.microsoft.com/en-us/library/azure/dn495299.aspx
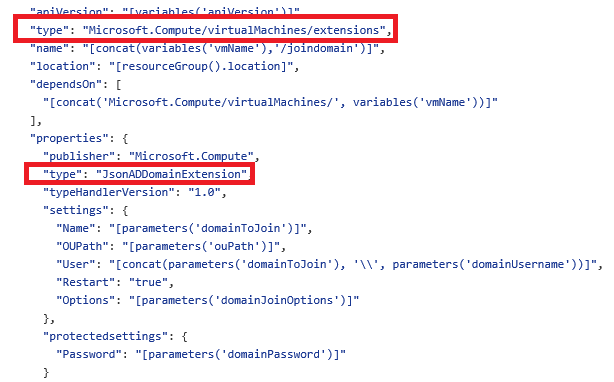
Unfortunately, there is no more evidence of domain join functionality in the newest Azure Resource Manager (ARM) API, then how to gain back that nice feature previously available in Azure ASM? There are essentially two ways, both based on a new type of ARM “Extension” called “JsonADDomainExtension”:
- Using Azure ARM Templates (“declarative mode”).
- Using Azure ARM PowerShell Cmdlet (“imperative mode”).
The first approach is very simple; you can find a template sample for automatic VM joining to an AD domain at the link below in GitHub:
201-vm-domain-join
https://github.com/Azure/azure-quickstart-templates/blob/master/201-vm-domain-join/azuredeploy.json
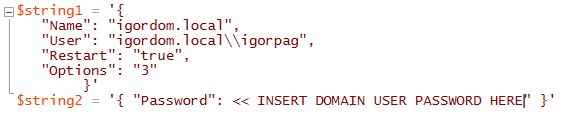
As you can see, this new extension type can take all the necessary parameters to join a VM to an existing AD domain, and then finally reboot the VM once the join operation is complete. If you try to search using Bing about this extension, you will not find (at least at the time of writing this post) any public reference nor documentation. Now, what happen if you don’t or want to use an ARM template and instead you have/want to use “imperative” PowerShell? What I have done below is reverse-engineering the template mentioned above and test a very simple script. First of all, you need to prepare two JSON strings as in the example below:
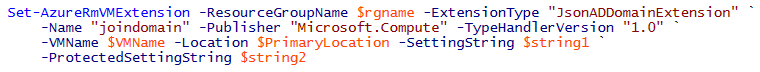
The first one contains all the necessary parameters/options for the domain join operation, please note that there is no documentation on the possible values for “Options”, value (3) is recommended in the GitHub template mentioned above. The second one contains protected info that the extension mechanism will encrypt transparently to guarantee security of passwords. After that, simply execute the PowerShell cmdlet below:
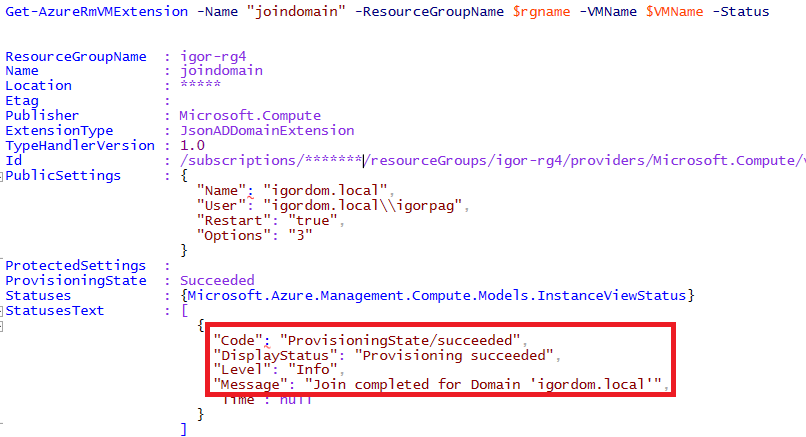
Execution of “Set-AzureRmVMExtension” cmdlet will require some time; you can check the status using the “Get-AzureRmVMExtension” cmdlet as in the example below (output sample included):
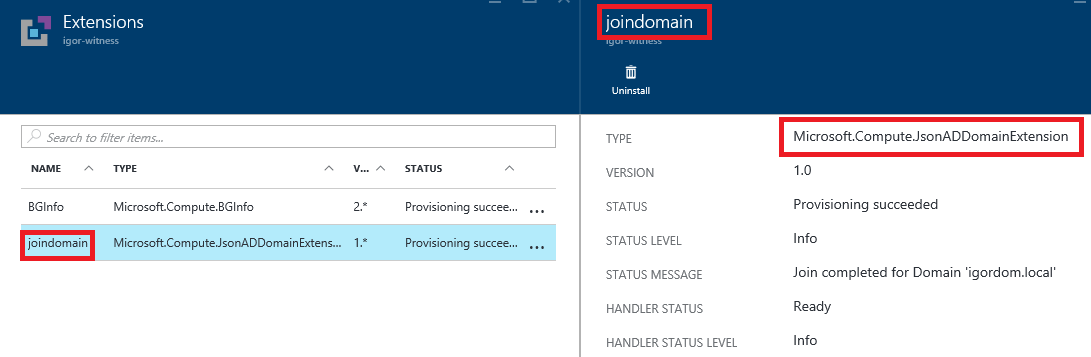
From the Azure Portal, you can see almost the same level of details going into the “Extension” tab of your Virtual Machine:
That’s all I wanted to share with you, hope you will find this content useful and interesting, feel free to post your comments and feedbacks here. Remember that you can also follow me on Twitter ( @igorpag). Best Regards.