A Security Prompt that makes you go “Huh?”…
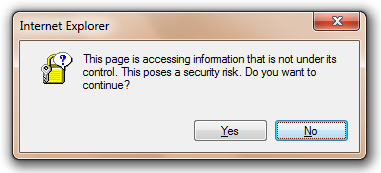
Every few months, a Microsoft employee will send me an email complaining that Internet Explorer showed them the following dialog:
This page is accessing information that is not under its control. This poses a security risk. Do you want to continue?
…and they don’t understand the question or how to answer.
This prompt is called the “Cross-domain data access” dialog, and it’s shown when a page makes a call that would violate same-origin-policy . The most common case where this occurs is when a site attempts to use the XmlHTTPRequest object to download data from a different origin, although there are a few other possibilities:
- When loading and XML-document cross-origin using MSXML
- When an OBJECT tag is pointed at an cross-domain HTML file (in legacy document modes)
- When some other control is using an InternetSecurityManager to permit selective violation of same-origin-policy
This dialog is shown when a same-origin-policy violating request is made and URLACTION_CROSS_DOMAIN_DATA is set to URL_POLICY_QUERY. When a ProcessURLAction call returns Query, it means “Ask the user to decide.”
By default, this URLAction is set to URLPOLICY_ALLOW in the Local Computer Zone (Security Template: Low), to URLPOLICY_QUERY in the Intranet Zone (Security Template: Medium-Low) and to URLPOLICY_DISALLOW in the Internet, Trusted, and Restricted Zones (Security Template: Medium or higher). Therefore, in a default configuration, this dialog is only seen on sites in the Intranet Zone; in all other zones, access to cross-domain data is either allowed or blocked with no notice to the user.
As the clunky icon and ambiguously-phrased text suggest, this is a very old security prompt and it only still exists for legacy compatibility. If we had no legacy compatibility burden, we simply would set the URLACTION_CROSS_DOMAIN_DATA policy to URLPOLICY_DISALLOW for all zones and never ask the user to make such a decision. Of course, Group Policy can always be used to change the default setting to either Allow (strongly discouraged) or Deny (recommended) cross-domain data use in the Intranet Zone. It’s strongly discouraged to set this to Allow by default because if you do so, any webpage on your Intranet can make any request to any other server on your Intranet using the user’s credentials and without their knowledge.
If your Intranet applications rely upon cross-domain data, then it’s strongly recommended that you redesign them to utilize a better pattern and not subject users to this prompt. Alternatives include:
- Have the web server itself make a back end webservice call (aka server-side proxy)
- Download cross-origin data using the XDomainRequest object
- If you trust the partner site, use the JSONP pattern
- If you trust the partner site, embed an IFRAME, and use postMessage if needed
-Eric