Controlling the XSS Filter
Internet Explorer 8 included a novel new feature to help prevent reflected cross-site scripting attacks, known as the XSS Filter. This filter runs by default in the Internet, Trusted, and Restricted security zones. Local Intranet zone pages may opt-in to the protection using the same header:
X-XSS-Protection: 1
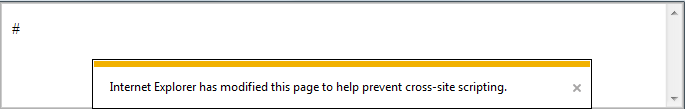
If a cross-site scripting attack is detected, Internet Explorer 8 and 9 will attempt to make the smallest possible modification to the returned web page in order to block the attack. Here’s an example. In most cases, the modification is to change one or more characters in the returned page into the hash character (“#”) breaking any script that may have been reflected from the outbound HTTP request.
Pages that have been secured against XSS via server-side logic may opt-out of this protection using a HTTP response header:
X-XSS-Protection: 0
In March of 2010, we added to IE8 support for a new token in the X-XSS-Protection header, mode=block.
X-XSS-Protection: 1; mode=block
When this token is present, if a potential XSS Reflection attack is detected, Internet Explorer will prevent rendering of the page. Instead of attempting to sanitize the page to surgically remove the XSS attack, IE will render only “#”. You can test the XSS Filter’s block mode here.
-Eric Lawrence