Announcing new project – patterns & practices - Claims based Authentication & Authorization Guide
For the next couple of months I’ll be working on a new project here at patterns & practices, developing a new guide for claims based authentication and authorization.
I’m personally very happy to be working on this project, for many reasons. I believe frameworks like “Geneva” (previously known as “Zermatt”, now Windows Identity Foundation), products like “Geneva Server” (now ADFS) are great platform additions to enable a new set of scenarios.
I realize that SSO, Federated Identity and Claims are not new. It’s just that we have much better tools and higher abstractions to implement these scenarios much more easily than ever.
I also feel privileged to work with such a great team. I’ll be sitting on giants shoulders: Dominick Baier, Vittorio Bertocci, Keith Brown, David Hill and Matias Woloski. Many others are joining as advisors and reviewers.
As it is customary now in the patterns & practices team, we will be publishing our content often and very early. I’ll post details here soon.
We also want to try a few new things in this project. In this guide we want to be very focused on the practices rather than on the “theory”, the “principles” or “philosophy” of claims based security.
We want to have very concrete scenarios, with a high fidelity of what happens out there in the real world. Almost a “case study” approach in which we weave a story across the book that takes the reader into more ambitious requirements as he proceeds.
With each chapter, we will introduce more complex solutions to address increasingly more ambitious requirements.
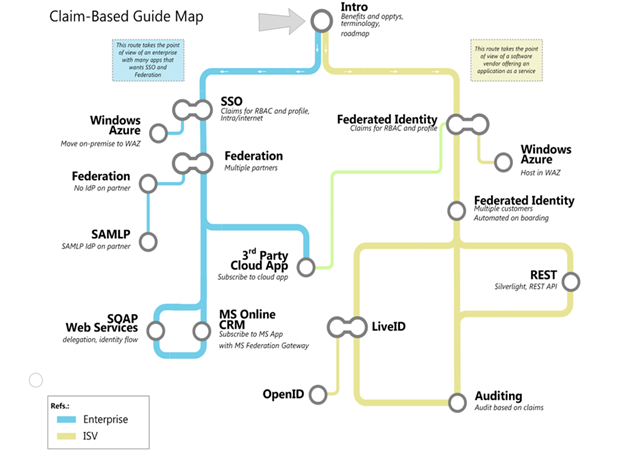
The current backlog for the scenarios we want to cover is illustrated below. Each “station” is a core scenario. Some will have small variations (like Azure hosting in the first one).
The two lines (yellow and light blue) refer to the two perspectives we plan to include: that of someone consuming software (the blue), and that of some building software (the yellow).
Stay tuned!
Eugenio
Update: fixed image size.