Kerberos or NTLM Authentication? How can I easily check which one am I using in my CRM Deployment?
Several customer face issues with Delegation when installing CRM server in multiple tiers. One of the first questions that arise regarding this subject is: how do I know which authentication type my users is currently facing?
Well, as a first blog post of other future detailed ones, this one explains how you can easily check which Authentication type you're experiencing. And the good this is that this can be done on the client machine without the need to use complex networking tools.
In order to identify how your Authentication is done, proceed as follows:
- Download the Fiddler tool to your client machine and install it. https://www.fiddler2.com/fiddler2/version.asp
- Close all Internet Explorer Windows
- Run the Fiddler Tool and check that the "Capture Traffic" option is enabled, under the "File" menu
- Fiddler will work as a pass-through proxy between the client machine and the server, listening to all traffic.
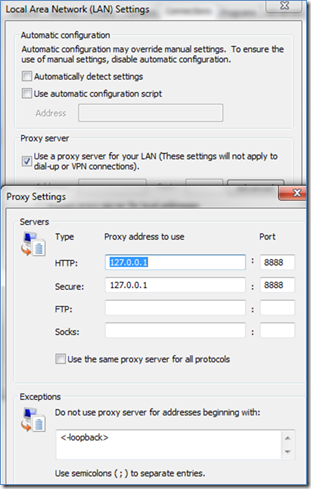
This will temporarily set your Internet Explorer Settings like this:
- Open internet Explorer and browse into your CRM Server URL, do some clicks here and there to generate traffic.
- Refer back to Fiddler main window and choose one of the Frames where the Result is "200" (success)
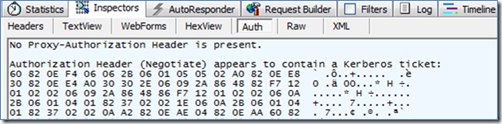
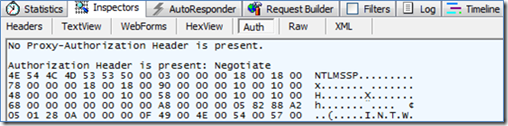
- Click on Inspector > Auth tabs
If Kerberos authentication is enabled and working, then the frame will contain information like "Authentication Header appears to contain a Kerberos ticket" and a set of special characters in the beginning of the frame.
If the Authentication type is NTLM, then you'll have "Negotiate - NTLMSSP" in the beginning of the frame, as shown below.
Glossary
NTLM Authentication
Challenge- Response mechanism.
In the NTLM protocol, the client sends the user name to the server; the server generates and sends a challenge to the client; the client encrypts that challenge using the user’s password; and the client sends a response to the server. If it is a local user account, server validate user's response by looking into the Security Account Manager; if domain user account, server forward the response to domain controller for validating and retrieve group policy of the user account, then construct an access token and establish a session for the use.
Kerberos authentication
Trust-Third-Party Scheme.
Kerberos authentication provides a mechanism for mutual authentication between a client and a server on an open network. The three heads of Kerberos comprise the Key Distribution Center (KDC), the client user and the server with the desired service to access. The KDC is installed as part of the domain controller and performs two service functions: the Authentication Service (AS) and the Ticket-Granting Service (TGS). When the client user log on to the network, it request a Ticket Grant Ticket (TGT) from the AS in the user's domain; then when client want to access the network resources, it presents the TGT, an authenticator and Server Principal Name (SPN) of the target server, contact the TGS in the service account domain to retrieve a session ticket for future communication with the network service, once the target server validate the authenticator, it create an access token for the client user.
Regards
Gonçalo Antunes