Microsoft Dynamics GP Web Client and Silverlight Security Requirements

In this article, I want to talk about our Silverlight application and the security components the GP Web Client has adopted. Being such that the Microsoft Dynamics GP client is now hosted within the web browser, new challenges arise when it comes to things like printing and exporting data out of your web browser. In addition, understanding that we need to be able to provide the same user experience in the Web Client as we have in the Rich client is a requirement that will be demanded by all end users. Taking that challenge on directly, our Silverlight application does contain the ability to:
- Print to your local printer
- Print to screen
- Print to a Word Template
- Export Smartlist data to Excel
- Perform a lookup on the folder structure to save files locally
But this capability does not exist out the box and it shouldn't for security reasons. Starting in Silverlight 5, system administrators can enable trusted applications to run inside the browser in order to simplify enterprise deployments and updates. Additional information on this topic can be found here. With most trusted applications, they typically run outside of the web browser which requires some level of admin access to the local machine in order to install it. But when trusting a Silverlight application within the browser, delivery and administration of updates can become automatic. So while there are some cool options that are enabled with this Silverlight feature, our main purpose for trusting our Silverlight application is to accomplish the task listed above.
In order to provide the required trust level to the Silverlight application, there are two changes that need to take place on the end users computer. These changes do not occur on the Web Server or Session Host. The two changes are:
- Enable the AllowElevatedTrustAppsInBrowser registry key to a value of 1
- Install the certificate that was used to sign our Silverlight XAP file.
So how do these changes work with our Silverlight application? In order to gain access to the local machine file system through the Silverlight application, we make Command Shell calls to invoke the required actions that we need to call an application or invoke a printing call. But before our Silverlight application can do that, the above items must be in place first. Changing the registry key is fairly straight forward, but gaining access to the certificate is a little more difficult. You can't use any old certificate to enable this functionality. The certificate you need is the certificate that Microsoft used to officially SIGN our Silverlight XAP file. Microsoft owns this certificate...and you need it. The cool thing however is that you already have the certificate and don't even know you do. Below are the steps you can take get make the registry change and extract/install the Microsoft certificate.
Step 1;
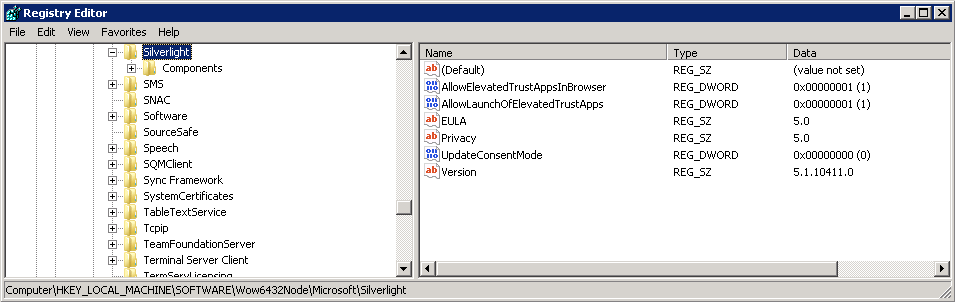
The first step DOES involve someone going into the local registry on the end user machine, finding the appropriate key and changing one value. While this step is not very difficult, anytime you open the registry editor, you need to take caution on what you change. To make the change, follow these steps:
- Start -> Run -> and type regedit then select OK.
- In the left hand pane navigate to: Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Silverlight.
- In the right hand pane, find the KEY named: AllowElevatedTrustAppsInBrowser.
- Double click on the KEY to open it.
- Ensure the value is set to a 1.
- Close the registry editor.
Note: The AllowElevatedTrustAppsInBrowser.reg file attached to the bottom of the post can simplify the registry change for you.
Step 2:
The second step involves extracting the certificate and then installing it to the correct certificate store. This step will require admin level access to the local machine because the certificate that you will be adding to the certificate store needs to go into a location that requires a higher level of permissions. The first thing we will be stepping through is to extract the certificate from our Silverlight XAP file. This might seem strange that you can do this, but in all reality, this method is WAY more secure than posting the actual certificate on this public blog for everyone to download and potentially use for the wrong purposes. With the RTM release of GP Web Client, we will be delivering an actual MSI installer that can be used to make these changes and install the certificate.
Note: Please do not post or share this certificate and make it available for public download. If you want to share anything, share these steps on how to extract the certificate. Being able to extract the certificate would mean that you at least have access to the GP Web Client software and have deployed it.
Follow these steps to extract/install the certificate:
- Navigate to the Web Client installation folder on your web server. The default path for this will be: C:\Program Files\Microsoft Dynamics\GP Web Client\GPWeb\ClientBin.
- Once at the above location, there should be a single file called: Microsoft.Dynamics.GP.Web.Silverlight.xap.
- Right click on the file and choose: Properties.
- Once the window opens, click on the Digital Certificate tab as shown below.
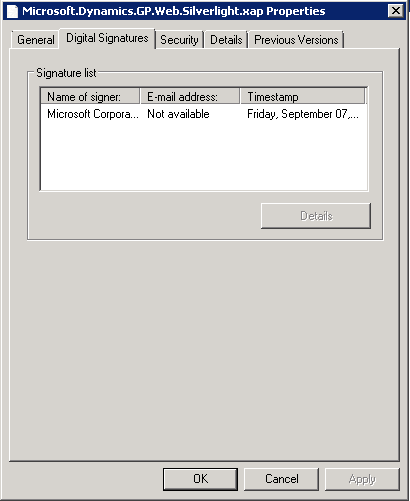
- Within the window, select the item in the Signature List box and then click the Details button.
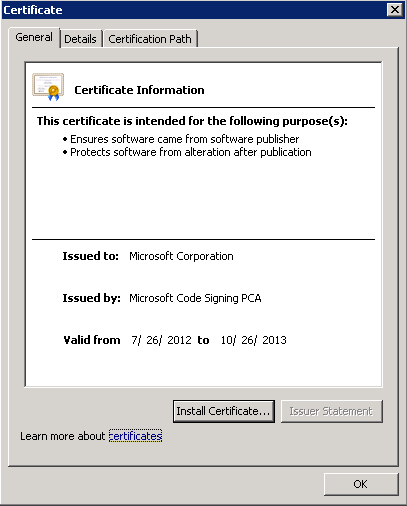
- The Digital Signature Details window will then open. The next step is to click on the View Certificate button.
- The Certificate window will open. The next step is to install the certificate. To do so, just click the button.
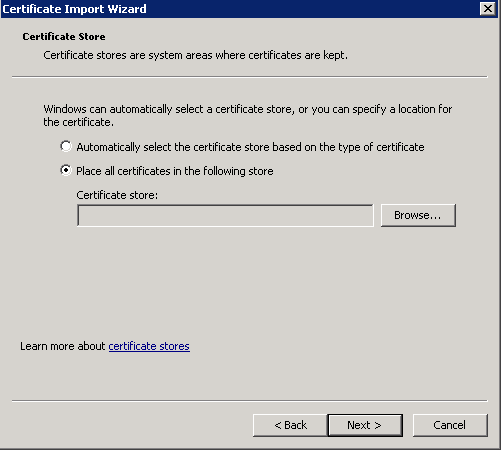
- Next you will begin the Certificate Import Wizard that will import the certificate into the store you choose. Click Next.
- Select the second radio button: Place all certificates in the follow store and click the Browse button.
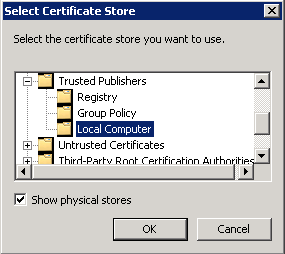
- At this point, you need to be very clear on what Certificate Store you are selecting. We need to make sure that you are installing into the Trusted Publishers folder for the Local Computer. To do that, be sure to mark the Show Physical Stores.
- After making sure the correct store is selected, click OK and then Finish to complete the process.
At this point, to validate that you have successfully load the certificate into the correct stored, follow these steps to find the certificate:
- Start -> Run -> and type MMC. A blank MMC console with then open.
- Go to File -> Add/Remove Snap-in. Select Certificates in the left hand pane and choose the Add button.
- A second window will then open asking for the Snap-in type. Choose Computer Account and then choose Finish. Choose OK.
- Now expand the Certificates node in the left hand pane and then expand the Trusted Publishers folder.
- Select the Certificate folder and what should be displayed are Microsoft Corporation certificates. The certificate that we are interested in has an expiration date of 10/26/2013.
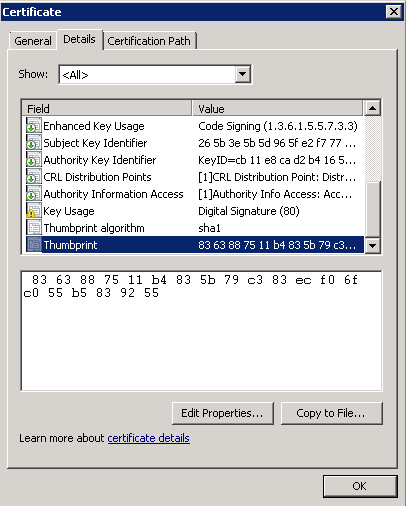
- Double click on the certificate and navigate the Details tab. Then scroll down to the Thumbprint value and click on it. The ID should match the one shown below.
If the ID matches, then you have successfully loaded the correct certificate needed to enable our Silverlight application as a Trusted Application. Your next step is to then log into GP Web Client to check and see if the Silverlight application has the required level of security access to the file system. When you don't have the correct level of access, the Silverlight application displays an icon in the lower right hand corner indicating just that. Below is a screen shot of that icon. The picture represents that the file system is still LOCKED OUT and displays a padlock type icon. This functionality will remain with the RTM release so when troubleshooting printing issues, this should be one of the first things you should look for because if the icon IS PRESENT, no printing or anything with the file system will occur through the Silverlight Application.
As I mentioned above, the RTM release will have a installer that will facilitate these steps above for you. But if you are using the BETA release, you are going to need this information. Enjoy the guidance and Happy Printing!!
Aaron
PS: While the printing options are enabled with these steps, the printing functionality IS NOT done and is continuing to evolve. What that really means, is that some stuff works and other stuff doesn't. Please be patient as we are working hard on getting this functionality right.