The SQL Swiss Army Knife #1 - Scripting Securables - Updated
EDIT (11-01-2013): Fixed issue with generating all logins even when single database was chosen.
EDIT (17-05-2015): Fixed duplicate permissions scripted with Procedures/Functions/CLR; Extended object coverage.
EDIT (11/18/2016): Fixed issue with permissions being repeated.
Download here: usp_SecurCreation.sql
Hello all,
This is the first in a new series sharing SQL scripts that may help on everyday DBA tasks, something in the likes of a "SQL Swiss Army Knife".
According to BOL, SQL securables "are the resources to which the SQL Server Database Engine authorization system regulates access".
I've been using the following script as a "local machine" bit of a wider DR strategy for years, because you never know when you need to quickly review or restore permissions over scopes when they got "accidently" changed or deleted.
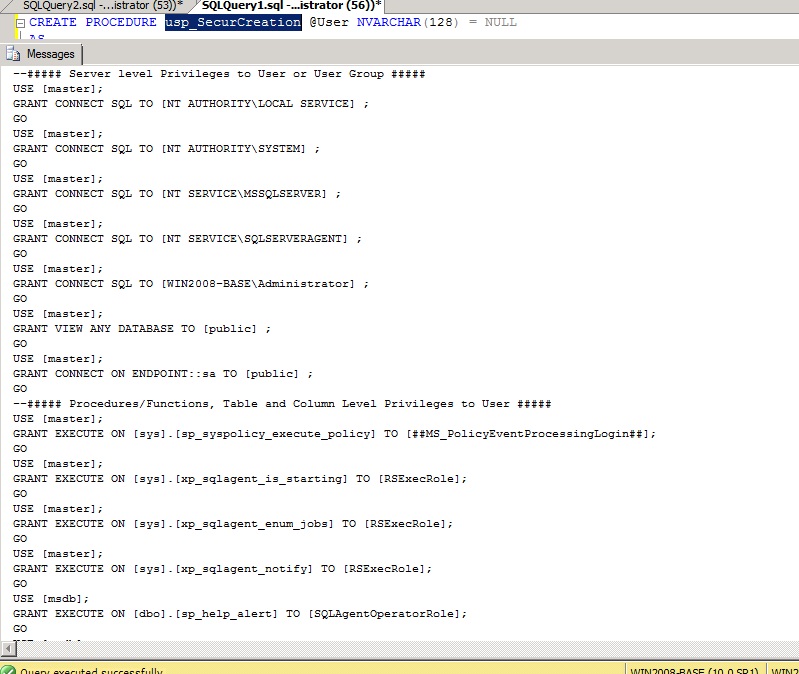
Its output may simply be saved onto a .sql file and will resemble this:
So for my first post, here is the script which I hope some of you will find useful.
These are the options available:
- All users:
EXEC usp_SecurCreation - One user, All DBs:
EXEC usp_SecurCreation '<User>' - One user, One DB:
EXEC usp_SecurCreation '<User>', '<DBName>' - All users, One DB:
EXEC usp_SecurCreation NULL, '<DBName>'
Until next time!
Disclaimer: I hope that the information on these pages is valuable to you. Your use of the information contained in these pages, however, is at your sole risk. All information on these pages is provided "as -is", without any warranty, whether express or implied, of its accuracy, completeness, fitness for a particular purpose, title or non-infringement, and none of the third-party products or information mentioned in the work are authored, recommended, supported or guaranteed by Ezequiel. Further, Ezequiel shall not be liable for any damages you may sustain by using this information, whether direct, indirect, special, incidental or consequential, even if it has been advised of the possibility of such damages.