Block Windows 10 Public Store using Microsoft Intune (but still allow the business store)
Hi Windows 10 experts and lovers :)
Today I want to talk to you about a very exciting feature which has been released in Windows 10 managed by Microsoft Intune. Now it's possible to disable the Windows 10 public store while keeping access to the business store (Windows Store for Business) .
Side note: We also have released in Microsoft Intune the integration with Windows Store for Business, which let you finally deploy silently modern apps from the store to users without having them to manually install the app. A coworker made a great article about how to implement this integration.
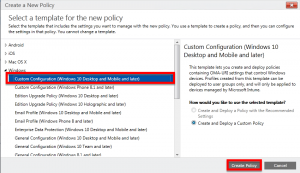
To block the public store, you need to create a new custom Windows 10 policy in Microsoft Intune (we create a new one because this one will target users and not devices).
- Connect to Microsoft Intune management portal
- From "Policy", create a new "Custom Configuration" policy for Windows 10.
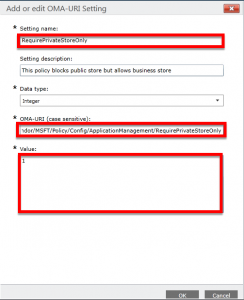
- Create a new OMA-URI setting. You will find details on the CSP policy reference page.
- OMA-URI: ./User/Vendor/MSFT/Policy/Config/ApplicationManagement/RequirePrivateStoreOnly
- Value: 1
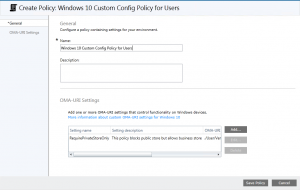
- Then validate the policy.
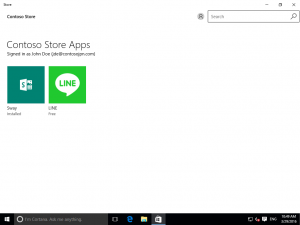
- And deploy that policy to a user collection. Here is the end result after you refresh MDM policy on a Windows 10 computer: public store's tabs has disappear but business store is still there :)
Everyday we're working hard to make Windows 10 more manageable using MDM. Hope you will enjoy this new feature :)
See you next time!