Windows Update for Business explained
* UPDATE * For more details, please visit the official Technet page about Windows Update for Business.
Hi Windows lovers and IT pros!
Today I want to make a quick jump of what a lot of us was waiting for: Windows Update for Business (WUfB).
To be clear, WUfB is not a WSUS in the cloud. And some of you were maybe expecting something like a SaaS version of WSUS but WUfB is still a cloud service which leverages the power of Windows Update services.
What WUfB brings is, is a way to control how to deliver security updates and features upgrades within your infrastructure while connecting directly to Windows Update. WUfB helps you create rings (see computer groups) by delaying delivery of updates/upgrades. Last but not least, you have an option to pause the deployment of updates and upgrades!
And for the bandwidth management (since you're connecting to a cloud service and not your local WSUS server), you have the peer to peer update feature introduced in RTM version of Windows 10 to limit Internet access for downloading updates and upgrades.
So if WUfB is not a WSUS in the cloud, how can we do what I explained above? The response is: it’s all done on the client side and controlled by 2 ways: GPO or MDM.
The GPO way
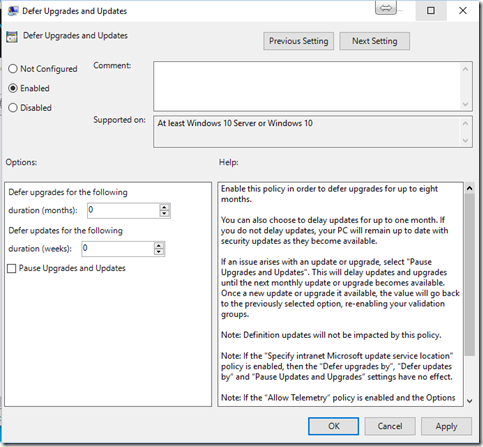
Windows 10 November Update has been recently released on November 12 and with that recent update, we have introduced a new GPO settings call “Defer Upgrades and Updates”.
To see what that setting looks like, open “Local Group Policy Editor” (Run –>gpedit.msc) and browse to “Computer Configuration” –> “Administrative Templates” –> “Windows Components” –> “Windows Update” and you will find the below screen.
The new “Defer Upgrades and Updates” introduces 3 new options:
- Defer upgrades up to 8 months (1 month increment)
- Defer updates up to 4 weeks (1 week increment)
- Pause Upgrades and Updates until the next update/upgrade release (around 30 days)
Important note: You can’t use those settings in conjunction with WSUS. if you specify an internal update service location, above settings will be ignored.
Additional note: By just enabling this GPO setting and not delaying anything (leaving both durations to 0), it will turn the target computers to CBB (Like the old GPO setting “Defer Upgrade” was doing in the Windows 10 RTM build).
The MDM way
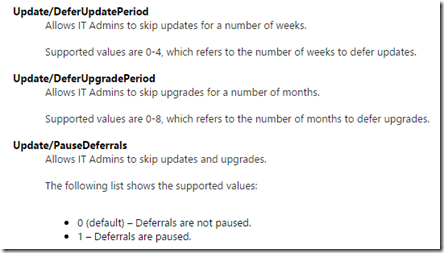
What we could configure through GPO above, we can do it as well with MDM style (Mobile Device Management). As you might know, MDM solutions (in my example, I used Microsoft Intune) will modify values of Windows CSP. Windows CSP are some kind of a management interface for Windows.
You can find a complete list of Windows 10 CSP on the following site.
Here’s the detail about the new 3 settings introduced by WUfB:
In Intune, I created a new Windows 10 Custom Configuration Policy and add the below OMA-URI settings to defer upgrades by 2 months:
The same goes for the other 2 settings.
Don’t use those new settings with WSUS/SCCM
The last important thing I want to remind is that, if you’re already using an on-prem solution to manage Windows updates/upgrades, do not use the new WUfB settings. To manage updates, you have 2 solutions then:
- Use WSUS (or SCCM) and manage how and when you want to deploy updates and upgrades to Windows 10 computers in your environment (in your intranet).
- Use the new WUfB settings to manage how and when you want to deploy updates and upgrades to Windows 10 computers in your environment directly connecting to Windows Update.