Microsoft Intune Exchange On-Premises Connector connectivity issue with a proxy
This article is very similar to the previous article I wrote concerning a proxy issue with the Azure AD Application Proxy connector.
This time, it concerns the Microsoft Intune Exchange On=Premises Connector used to activate Conditional Access for Exchange On-Premises. Again my customer who is using an Enterprise proxy was facing issue to make that connector work.
Looking at the Application logs on the server where the Exchange On-Prem Connector was installed provided the information about connectivity issues of the connector. (Unfortunately, since I can’t reproduce the issue in my lab, I don’t have the screenshot, nor the exact error that the connector should log).
Anyway, the issue was clear: the Intune Exchange On-Prem Connector wasn’t using the proxy settings from IE, nor Winhttp.
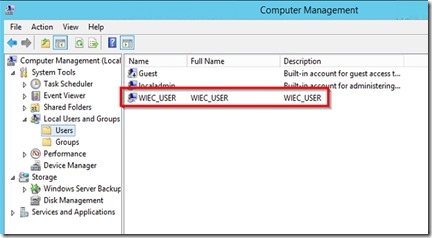
What was also differing from the Azure AD Application Proxy connector issue is that the Exchange connector is using a locally created account named “WIEC_USER”.
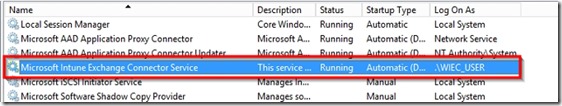
And we can verify that the Exchange Connector Service is using that account.
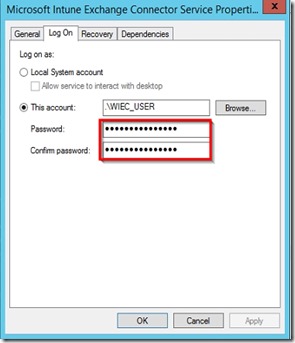
This time, it’s an user that you can use to connect to a session and set manually the proxy by opening IE. Since the “WIEC_USER” doesn’t have any password set by default, I set one and changed the service account password for “Microsoft Intune Exchange Connector Service”
To finish, I just needed to log into “WIEC_USER” session and set the proxy settings into IE. Log out the “WIEC_USER” session, come back to your session and restart the “Microsoft Intune Exchange Connector Service”.
On the Intune admin portal, run a quick sync and you should see in logs that everything is going smoothly this time!
UPDATE: I’ve seen the exactly same issue with Azure AD Connect at customer’s site. We had to follow the exactly same steps for the AAD_xxxxx account created by Azure AD Connect installer!