Accessing Azure SQL DB from Azure VM using a static Public IP adress
As it's known Azure SQL DB relies on the FQDN of the server the database is on for resolution. So how can we access Azure SQL DB from an Azure VM using a Public IP and make sure that it remains the same?further how we can disallow arbitrary machines from within the Windows Azure environment to have access to your Azure SQL Database servers, while still allowing specificmachines within the Azure environment to have access to Azure SQL Database servers? Let's see!
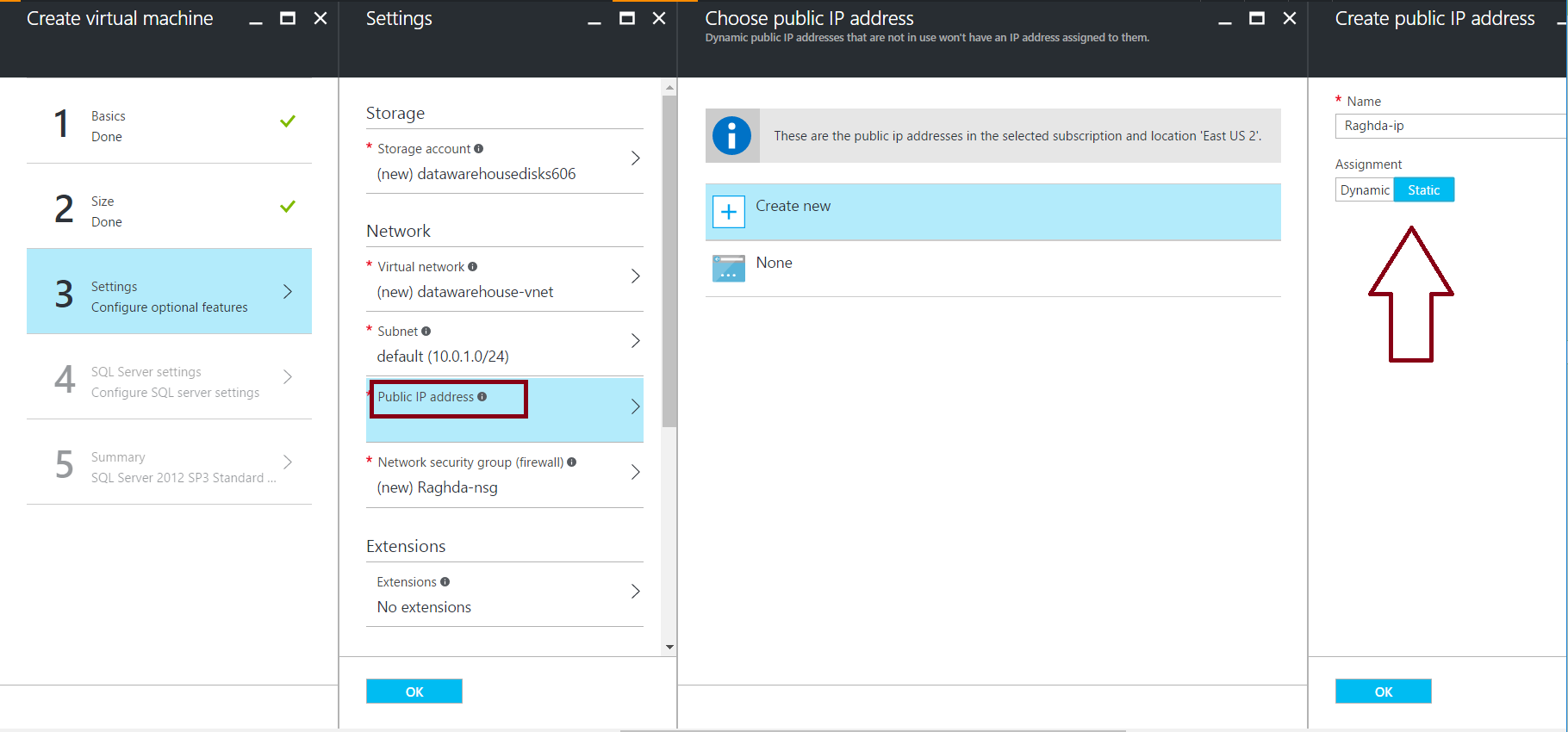
- when creating an Azure VM, you have the choice to use one of the two methods in which an IP address is allocated to public IP resource - dynamic or static, taking in consideration that the NONE option means that you will not be able to connect to Azure SQL DB, because there is no Public IP to connect to the Proxy.
Note: Even when you set the allocation method to static, you cannot specify the actual IP address assigned to the public IP resource. Instead, it gets allocated from a pool of available IP addresses in the Azure location the resource is created in.
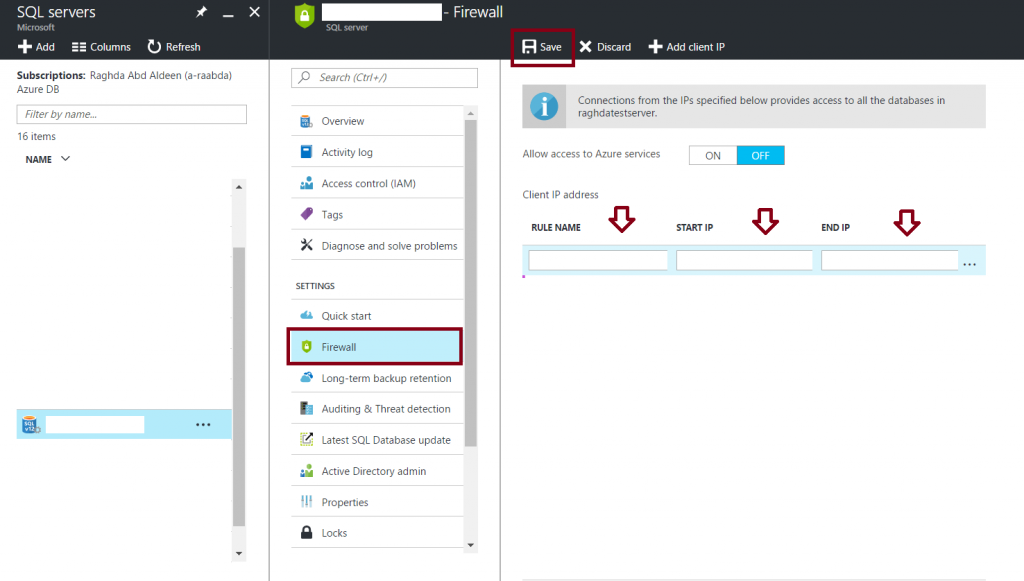
2. Now go to the azure SQL Database server you would like to restrict calls only to external IP addresses, so click on Show Firewall Setting then set the Allow access to azure services to OFF. 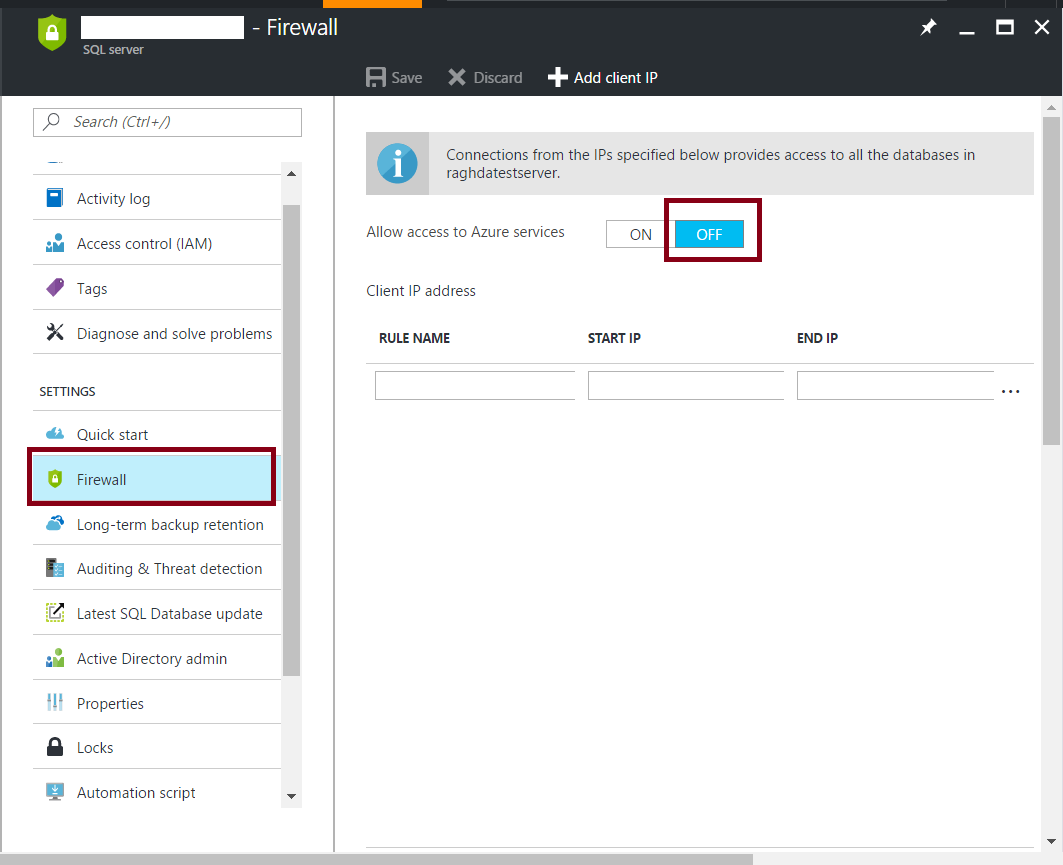
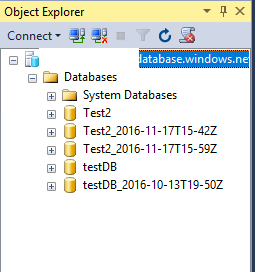
3.Test connection to AZURE SQL DB using SSMS 2016 you should receive the following message, to add the static public IP we got previous to the Azure SQL DB firewall rules in the Portal,
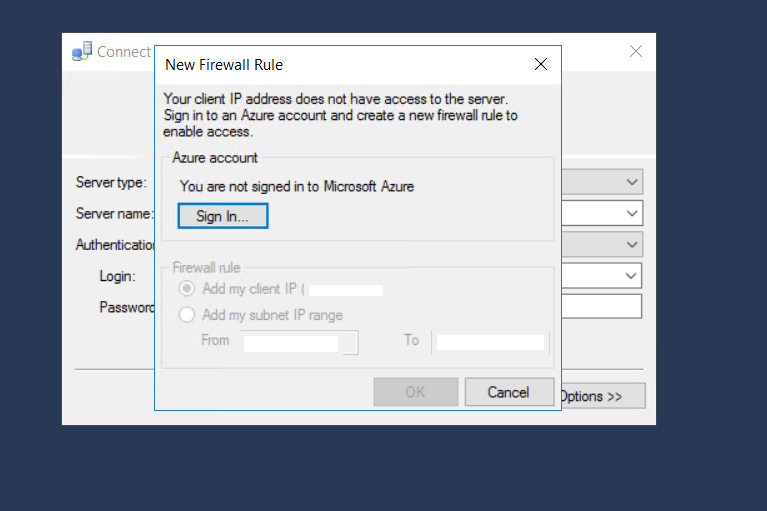 or you can add it manually by opening the Portal and go to your Server and follow the below figure
or you can add it manually by opening the Portal and go to your Server and follow the below figure
4. then you 'll be able to connect to your Azure SQL DB with a public static IP without causing an unexpected failure for your application connecting to Azure SQL DB.
Further, it's better to define the ranges that Azure SQL DB IPs fall into (as well as other Azure services) which are published here: https://www.microsoft.com/en-us/download/confirmation.aspx?id=41653,but keep in mind that they are updated regularly to expand the data center ranges of IP's.