Get Threat Intelligence Reports with Azure Security Center
 There’s a very cool feature in Azure Security Center that deserves more attention.
There’s a very cool feature in Azure Security Center that deserves more attention.
Actually, there are a lot of such features – but the one I have my mind on today is the integrated Threat Intelligence Reports you get when you enable Azure Security Center on your Azure subscriptions.
You might not have seen them (yet). There’s no button to push to find them, as you’ll find them as part of the details of security alerts you receive.
Here’s how you find them.
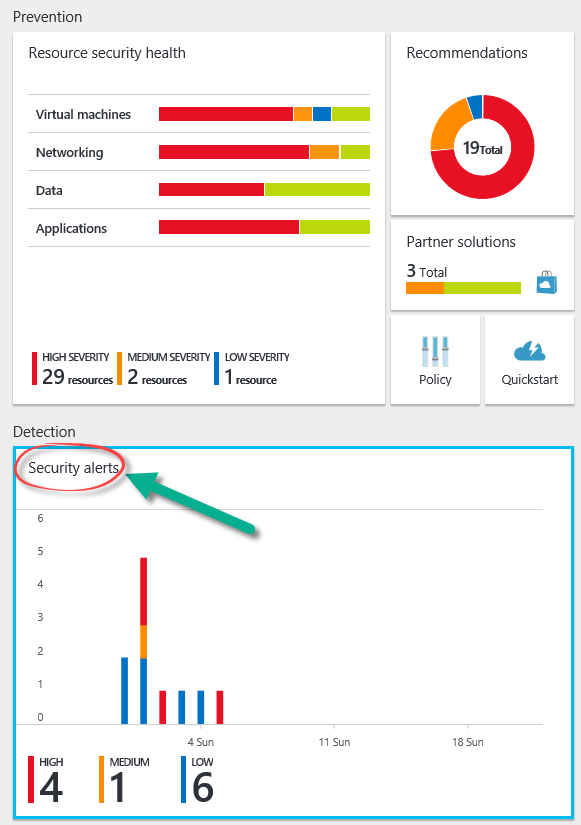
Open up Azure Security Center in your Azure portal. There you’ll see in the Security Alerts tile as highlighted in the figure below. Click (or tap or punch ![]() ) that.
) that.
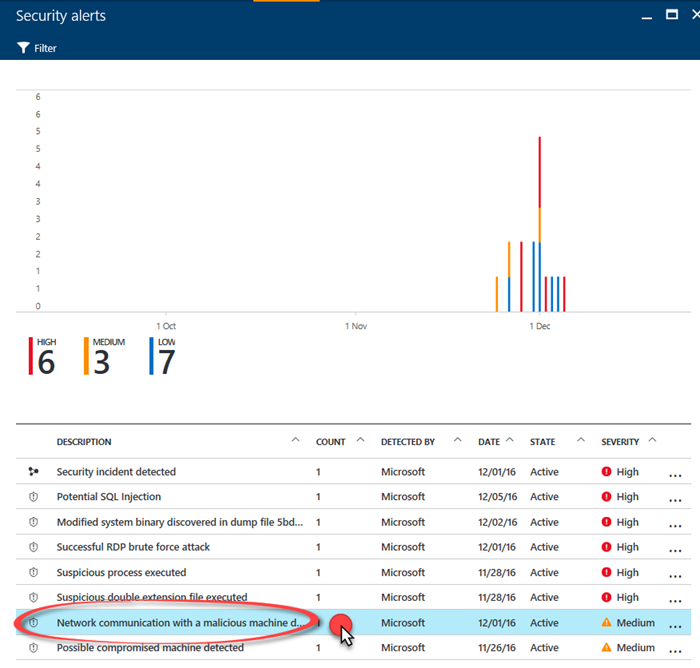
This opens up the Security Alerts blade. At the bottom of this blade is a list of security alerts.
Let’s click on the Network communication with a malicious machine detected alert, as seen in the figure below.
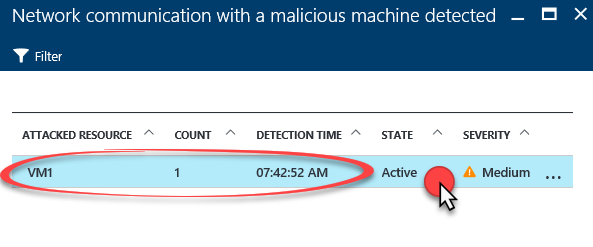
This opens the Network communication with a malicious machine detected blade. Here we see that VM1 generated this alert. Let’s click on that.
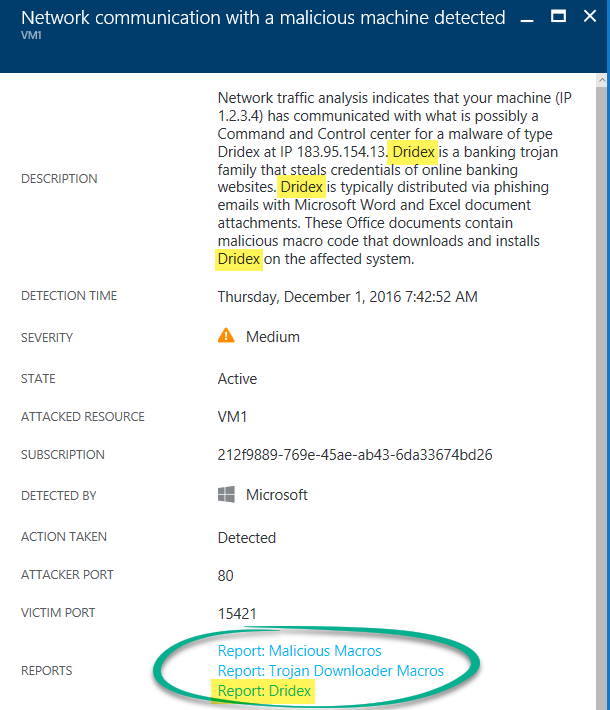
Here we see a number of details regarding this alert. It appears that this VM has been communicating with an IP address that has been identified as a Command and Control Server for the Dridex banking Trojan.
You’ll see at the bottom of the figure that are some Reports associated with this attack. These are Threat Intelligence Reports.
You can click on any of these links and get to a PDF Threat Intelligence Report.
To learn more about Azure Security Center Threat Intelligence Reports, check out the article Azure Security Center Threat Intelligence Report.
Thanks!
Tom
Tom Shinder
Program Manager, Azure Security
@tshinder | Facebook | LinkedIn | Email | Web | Bing me! | GOOG me