Missing Source Information in Azure Security Center Alerts
 Hello Azure security community!
Hello Azure security community!
Yuri Diogenes (CSI Enterprise Mobility and Azure Security team) here. Recently we updated our Managing and responding to security alerts in Azure Security Center article to add more details regarding alerts for suspicious activities. When the Azure Security Center attack detection mechanism triggers an alert, it will show you which resource was attacked and it will provide more information about the attack.
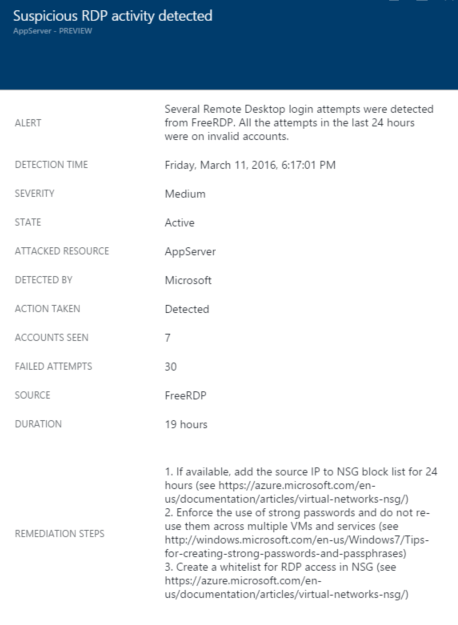
The below is an example of what you might see:
In this particular attack, the AppServer resource was attacked using the free tool FreeRDP. Several logins (30 to be more precise) were attempted in the last 19 hours. This is a useful information and you can follow the recommendation steps to mitigate this attack.
However, in some cases the SOURCE field is empty. There’s no IP address, no utility name nor DNS name.
This occurs for the same reason that security event ID 4625 in the Windows operating system sometimes doesn’t provide the source network address as shown in the example below (notice these fields):
Log Name: Security
Source: Microsoft-Windows-Security-Auditing
Date: 3/25/2016 1:39:56 PM
Event ID: 4625
Task Category: Logon
Level: Information
Keywords: Audit Failure
User: N/A
Computer: BYATACE
Description:
An account failed to log on.
Subject:
Security ID: SYSTEM
Account Name: BYATACE$
Account Domain: WORKGROUP
Logon ID: 0x3E7
Logon Type: 10
Account For Which Logon Failed:
Security ID: NULL SID
Account Name: Administrator
Account Domain: BYATACE
Failure Information:
Failure Reason: Unknown user name or bad password.
Status: 0xC000006D
Sub Status: 0xC000006A
Process Information:
Caller Process ID: 0xed0
Caller Process Name: C:\Windows\System32\winlogon.exe
Network Information:
Workstation Name:
Source Network Address: 0.0.0.0
Source Port: 0
Detailed Authentication Information:
Logon Process: User32
Authentication Package: Negotiate
Transited Services: -
Package Name (NTLM only): -
Key Length: 0
This event is generated when a logon request fails. It is generated on the computer where access was attempted.
The Subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe.
The Logon Type field indicates the kind of logon that was requested. The most common types are 2 (interactive) and 3 (network).
The Process Information fields indicate which account and process on the system requested the logon.
The Network Information fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases.
The Detailed Authentication Information fields provide detailed information about this specific logon request.
- Transited services indicate which intermediate services have participated in this logon request.
- Package name indicates which sub-protocol was used among the NTLM protocols.
- Key length indicates the length of the generated session key. This will be 0 if no session key was requested.
This information is not always available because not every code path in Windows is instrumented for IP address collection or recording. You can also refer to this site for more information about this event.