Azure Disk Encryption Management for Windows and Linux Virtual Machines
CLICK HERE TO SEE THE MOST RECENT POST ON AZURE DISK ENCRYPTION
Also check out cool Azure Disk Encryption PowerShell tutorials!
Explore Azure Disk Encryption with Azure Powershell
Explore Azure Disk Encryption with Azure PowerShell – Part 2
======================================================
This post comes from Devendra Tiwari, a senior security program manager in the Azure Security engineering team.
While making strong commitments about the privacy and sovereignty of your data, Microsoft Azure enables you to control your Azure hosted data through a range of advanced technologies to encrypt, control and manage encryption keys, control & audit access of data. This provides Azure customers the flexibility to choose the solution that best meets their business needs.
In this blog, we will introduce you to a new technology solution “Azure Disk Encryption Management for Windows and Linux VM’s” to help protect and safeguard your data to meet your organizational security and compliance commitments.
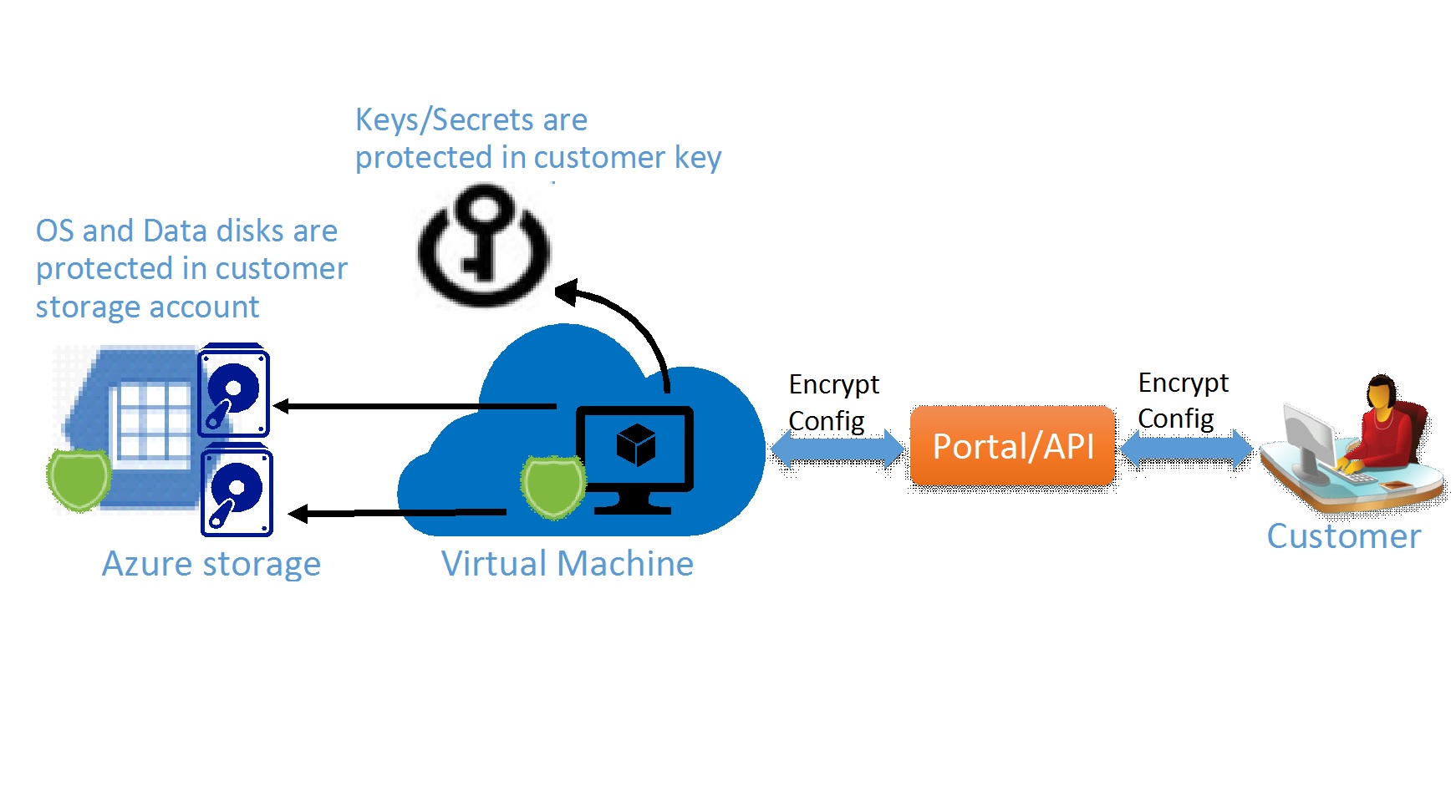
At the Ignite Chicago 2015 conference earlier this week, the Azure Security team demonstrated a new capability that will let you encrypt your Virtual Machine disks including the boot and the data disks. The Azure Disk Encryption for VMs works for both Linux and Windows Operating Systems. The solution is integrated with the Azure Key Vault to help you control and manage your disk encryption keys in your Key Vault subscription, while ensuring all the data in the VM disks are encrypted at rest in your Azure storage accounts.
The Azure Disk Encryption solution for Windows is based on proven Microsoft BitLocker Drive Encryption and the Linux solution is based on DM-Crypt.
Value Proposition
The Azure Disk Encryption Management solution enables the following business needs in the cloud:
- VM’s are secured at rest using industry standard encryption technology to address organizational security and compliance requirements.
- VM’s boot under customer controlled keys and policies, and they can audit their usage in Key Vault.
Encryption Scenarios
The Azure Disk Encryption solution supports the following 3 customer encryption scenarios:
- New VM’s created from Customer Encrypted VHD’s
- New VM’s created from the Azure Gallery
- Existing VM’s already running in Azure
Azure Disk Encryption key management with Azure Key Vault
Using the Azure Disk Encryption solution, customer control their data encryption options, key management and data/key access. The key management is integrated in the customer key vault using HSM technology. The encryption keys and secrets for the Windows BitLocker and the Linux DM-Crypt solution are stored protected in the customer key vault subscription. Customers grant read or write access to their key vault container to Azure Identity to enable volume encryption by specifying the key vault uri to access their key material. Azure personnel does not have any default access to the customer key vault for volume encryption solution.
Azure Disk Encryption Workflow: The high level steps required to enable disk encryption for the Windows and Linux VM’s are:
- Customer choose the encryption scenario from the above 3 encryption scenarios
- Customer opts into enabling disk encryption via the Azure portal or API and specifies the encryption configuration
- For the customer encrypted VHD scenario, the customer uploads the encrypted VHD to their storage account and encryption key material to their key vault and provide the encryption configuration
- For the new VM’s created from the Azure gallery and existing VM’s already running in Azure, customer provide the encryption configuration
- Customer grants access to Azure platform to add or read the encryption key material * from their key vault by specifying their key vault uri
- Azure service management updates the VM service model with encryption and key vault configuration and provisions encrypted VM for the customer
*Key Material – BitLocker Encryption Keys [Windows], Passphrase [Linux]
Stay tuned to this channel for more detailed updates and announcements in the not too distant future as we advance the Azure cloud security infrastructure.
David B. Cross
Engineering Director, Azure Security